Zero Trust Framework Nattytech The zero trust framework represents a paradigm shift in cybersecurity, emphasizing the importance of strict access controls and continuous monitoring to protect organizations from evolving cyber threats. A zero trust framework is a security model that operates on the principle of "never trust, always verify," meaning it requires strict identity verification for every user and device trying to access resources, regardless of their location.

Zero Trust Framework In today’s world of remote work, cloud adoption, and evolving cyber threats, traditional security models no longer cut it. the zero trust framework is a modern cybersecurity approach that assumes no user, device, or application can be trusted by default — not even those inside the network perimeter. Explore the zero trust assessment to automate security checks, implement industry standards, and strengthen your organization’s zero trust architecture. The challenge lies in transitioning from traditional models to a zero trust approach and ensuring alignment on strategy and tools across the board. when implementing zero trust, what. Learn how to shrink the attack surface and implement a zero trust security model. what is zero trust? defined and explained. zero trust is a security framework. it works on the principle that no user, device, or application should be inherently trusted.
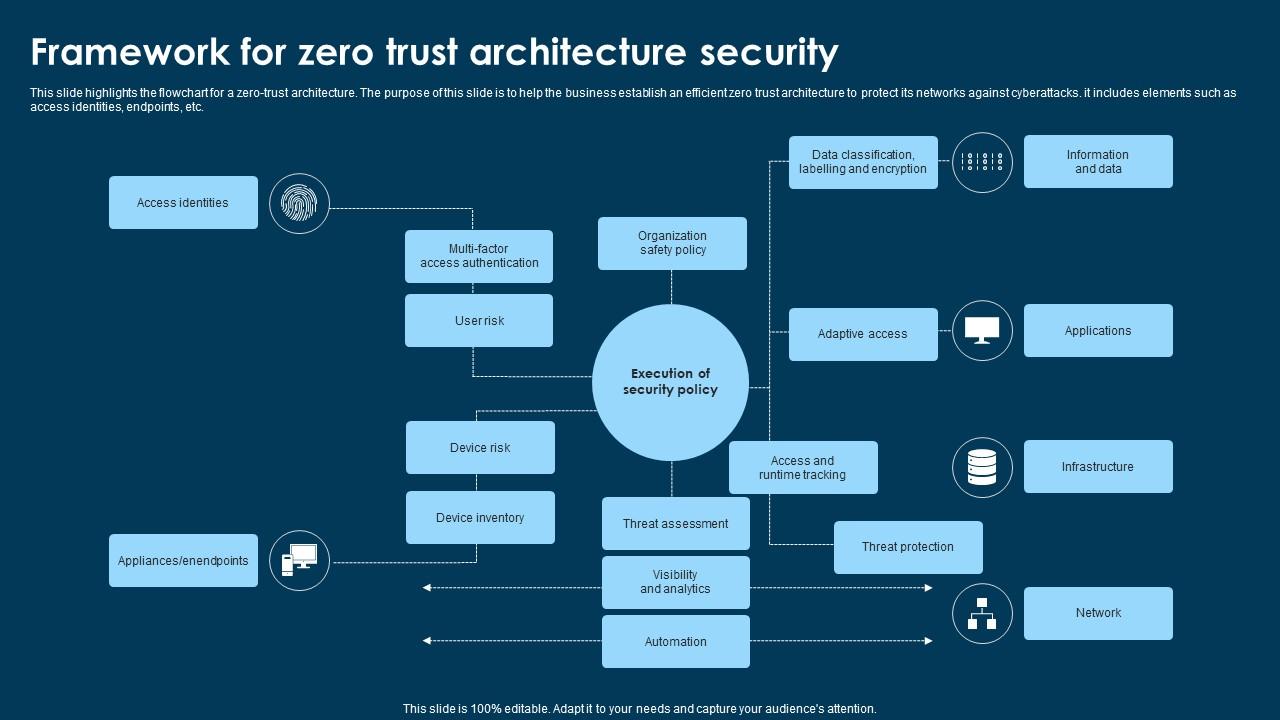
Framework For Zero Trust Architecture Security Ppt Example The challenge lies in transitioning from traditional models to a zero trust approach and ensuring alignment on strategy and tools across the board. when implementing zero trust, what. Learn how to shrink the attack surface and implement a zero trust security model. what is zero trust? defined and explained. zero trust is a security framework. it works on the principle that no user, device, or application should be inherently trusted. A zero trust architecture is not a single technology but a cohesive framework built on multiple interconnected security components. the core of its functionality lies in a comprehensive approach to identity, device, and network security. Discover the evolution of zero trust security, its development, models, and framework, and learn how it can protect your organization from modern threats. Get a comprehensive guide to key zero trust concepts, the most influential frameworks, top zero trust benefits, and best practices for selecting a zero trust vendor. What is zero trust? the zero trust security model uses identity and context information to continually verify trust before granting least privilege access for users, devices, apps, networks, and clouds.