
Free Video Web App Pentesting Http Headers And Methods From So, you should apply this methodology to each discovered domain, subdomain or ip with undetermined web server inside the scope. start by identifying the technologies used by the web server. Enumerate supported http methods to identify potential attack vectors. check common files that may reveal sensitive information or hidden paths. identify the technology stack and frameworks used by the web application. different web servers have unique vulnerabilities that can be exploited.

Testing Http Methods For Web Application Security Techarry Ptes is a comprehensive methodology that provides a structured framework for penetration testing, including web application security assessments. it covers all phases from pre engagement to post assessment, ensuring both business and technical perspectives are addressed. Welcome to the all new, revamped web app pentesting course, in this video, i explain the various http request and response headers as well as http methods and how the put method can. Welcome to the all new, revamped web app pentesting course, in this video, i explain the various http request and response headers as well as http methods and how the put method can be abused. Identify what the methods used are? identify where the methods used are? check whether a user is able to de provision themself or not? test multiple logins allowed or not?.

Web App Pentesting Dianahost Welcome to the all new, revamped web app pentesting course, in this video, i explain the various http request and response headers as well as http methods and how the put method can be abused. Identify what the methods used are? identify where the methods used are? check whether a user is able to de provision themself or not? test multiple logins allowed or not?. Web application penetration testing explained step by step. learn the methodology, tools, and techniques used in real world web app assessments. start free. Explore the intricacies of http headers, response headers, and http methods in this comprehensive video on web application pentesting. delve into the various request and response headers, gaining insights into their significance in web security. Learn what is web application penetration testing methodology, from scoping to remediation, and how to turn findings into actionable improvements. Web application penetration testing works by using manual or automated penetration tests to identify any vulnerability, security flaws or threats in a web application. the tests involve using implementing any of the known malicious penetration attacks on the application.
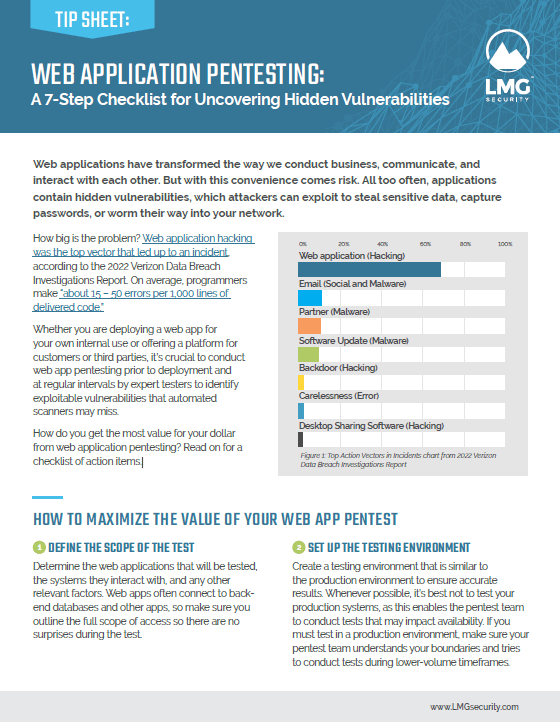
Web App Pentesting Checklist Lmg Security Web application penetration testing explained step by step. learn the methodology, tools, and techniques used in real world web app assessments. start free. Explore the intricacies of http headers, response headers, and http methods in this comprehensive video on web application pentesting. delve into the various request and response headers, gaining insights into their significance in web security. Learn what is web application penetration testing methodology, from scoping to remediation, and how to turn findings into actionable improvements. Web application penetration testing works by using manual or automated penetration tests to identify any vulnerability, security flaws or threats in a web application. the tests involve using implementing any of the known malicious penetration attacks on the application.