Unit 2 Aes Aes Structure Encryption Example Pdf Advanced encryption standard, aes, subbytes, shiftrows, mixcolumns, addroundkey, encryption, decryption, gf polynomial theorem download as a pdf, pptx or view online for free. Unit 2.2 aes free download as powerpoint presentation (.ppt .pptx), pdf file (.pdf), text file (.txt) or view presentation slides online.
Unit 2 Aes Aes Structure Encryption Example Pdf To review the overall structure of aes and to focus particularly on the four steps used in each round of aes: (1) byte substitution, (2) shift rows, (3) mix columns, and (4) add round key. Aes has defined three versions, with 10, 12, and 14 rounds. each version uses a different cipher key size (128, 192, or 256), but the round keys are always 128 bits. figure 7.1 general design of aes encryption cipher • aes encryption algorithm is called cipher. The aes algorithm is a symmetric block cipher that can encrypt (encipher) and decrypt (decipher) digital information. the aes algorithm is capable of using cryptographic keys of 128, 192, and 256 bits to encrypt and decrypt data in blocks of 128 bits. These slides are based on lawrie brown’s slides supplied with william stalling’s book “cryptography and network security: principles and practice,” 6th ed, 2013.
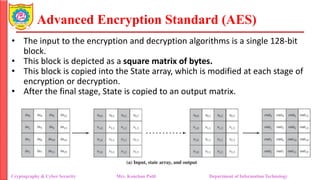
Unit 2 Aes Aes Structure Encryption Example Pdf The aes algorithm is a symmetric block cipher that can encrypt (encipher) and decrypt (decipher) digital information. the aes algorithm is capable of using cryptographic keys of 128, 192, and 256 bits to encrypt and decrypt data in blocks of 128 bits. These slides are based on lawrie brown’s slides supplied with william stalling’s book “cryptography and network security: principles and practice,” 6th ed, 2013. The overall structure of aes can be seen in 7.1. the input is a single 128 bit block both for decrypt on and encryption and is known as the in matrix. this block is copied into a state array which is modified at each stage of the algorithm and. Aes is a subset of the rijndael block cipher developed by two belgian cryptographers vincent rijmen and joan daemen, who submitted a proposal to nist during the aes selection process. The four transformations used in aes. for each stage, we describe the forward (encryption) algorithm, the inverse (decryption) algorithm, and the rationale for the stage. This figure depicts the arrangement of the encryption key in the form of 4 byte words and the expansion of the key into a key schedule consisting of 44 4 byte words.
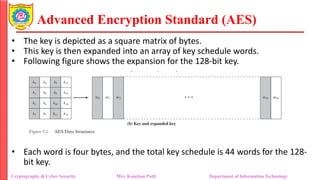
Unit 2 Aes Aes Structure Encryption Example Pdf The overall structure of aes can be seen in 7.1. the input is a single 128 bit block both for decrypt on and encryption and is known as the in matrix. this block is copied into a state array which is modified at each stage of the algorithm and. Aes is a subset of the rijndael block cipher developed by two belgian cryptographers vincent rijmen and joan daemen, who submitted a proposal to nist during the aes selection process. The four transformations used in aes. for each stage, we describe the forward (encryption) algorithm, the inverse (decryption) algorithm, and the rationale for the stage. This figure depicts the arrangement of the encryption key in the form of 4 byte words and the expansion of the key into a key schedule consisting of 44 4 byte words.
Unit 2 Aes Aes Structure Encryption Example Pdf The four transformations used in aes. for each stage, we describe the forward (encryption) algorithm, the inverse (decryption) algorithm, and the rationale for the stage. This figure depicts the arrangement of the encryption key in the form of 4 byte words and the expansion of the key into a key schedule consisting of 44 4 byte words.