
Rsa Encryption Algorithm Download Scientific Diagram Based on this revolutionary idea, rsa was invented. rsa is based on simple but magical mathematical results. in the following sections, we explore the underlying mathematics. in the following, n is a positive integer greater than 0. unless otherwise specified, all integers are positive. In rsa, we have two large primes p and q, a modulus n = pq, an encryption exponent e and a decryption exponent d that satisfy ed = 1 mod (p 1) (q 1). the public key is the pair (n,e) and the private key is d.

Rsa Encryption Number Theory Mathtuition88 But with quantum technology quickly evolving, many of our classic mathematical techniques in cryptography are under threat. in the following discussion we will inspect the mathematics behind the most common encryption mechanism: rsa. It is necessary to understand rsa, but also number theory and abstract algebra in general. in mathematics, modular arithmetic is a system of operations for integers, constrained to a set of. Sion method. in this expository paper, we provide a historical and technical overview of the rsa . ryptosystem. we introduce the mathematical methods used in rsa, present the steps of the algorithm, discuss complexity results relating to the security of rsa, and implement a python ve. si. n of rsa. 1. This chapter explores the mathematics behind the rsa cryptosystem including the encryp tion, decryption and signature schemes of rsa. we give a survey of the main methods used in attacks against the rsa cryptosystem.
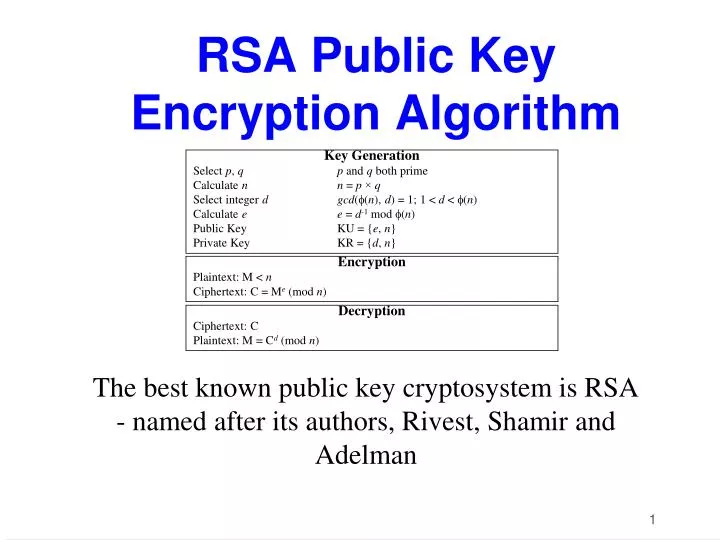
Encryption And Decryption Using Rsa Algorithm In Python Rioklo Sion method. in this expository paper, we provide a historical and technical overview of the rsa . ryptosystem. we introduce the mathematical methods used in rsa, present the steps of the algorithm, discuss complexity results relating to the security of rsa, and implement a python ve. si. n of rsa. 1. This chapter explores the mathematics behind the rsa cryptosystem including the encryp tion, decryption and signature schemes of rsa. we give a survey of the main methods used in attacks against the rsa cryptosystem. The science of employing mathematics to conceal data behind encryption is known as cryptography. number theory is a key component of cryptog raphy, which ensures that information cannot be easily recovered without special knowledge. This paper reviews one such algorithm, the rsa algorithm, and the mathematical concepts behind it. Our research on the rsa algorithm brings a significant amount of mathematics to bear. for instance, we have needed to understand how best to use the algorithm to establish keys and sign messages. Rsa algorithm is based on factorization of large number and modular arithmetic for encrypting and decrypting data. it consists of three main stages: encryption: sender encrypts the data using public key to get cipher text. decryption: decrypting the cipher text using private key to get the original data. 1. key generation.
Understanding The Rsa Algorithm For Encryption Algocademy Blog The science of employing mathematics to conceal data behind encryption is known as cryptography. number theory is a key component of cryptog raphy, which ensures that information cannot be easily recovered without special knowledge. This paper reviews one such algorithm, the rsa algorithm, and the mathematical concepts behind it. Our research on the rsa algorithm brings a significant amount of mathematics to bear. for instance, we have needed to understand how best to use the algorithm to establish keys and sign messages. Rsa algorithm is based on factorization of large number and modular arithmetic for encrypting and decrypting data. it consists of three main stages: encryption: sender encrypts the data using public key to get cipher text. decryption: decrypting the cipher text using private key to get the original data. 1. key generation.
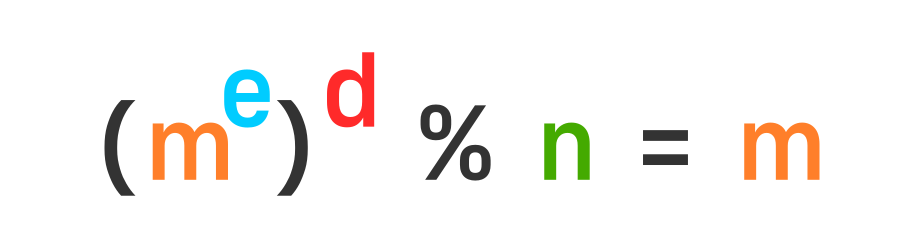
Simplified Explanation Of How Rsa Message Encryption Decryption Works Our research on the rsa algorithm brings a significant amount of mathematics to bear. for instance, we have needed to understand how best to use the algorithm to establish keys and sign messages. Rsa algorithm is based on factorization of large number and modular arithmetic for encrypting and decrypting data. it consists of three main stages: encryption: sender encrypts the data using public key to get cipher text. decryption: decrypting the cipher text using private key to get the original data. 1. key generation.