
Rsa Examples Pdf Cryptography Theoretical Computer Science Rsa algorithm the rsa (rivest shamir adleman) algorithm is an asymmetric cryptography algorithm created in 1977 by three mathematicians: ron rivest, adi shamir, leonard adleman. Practice with examples: practice solving rsa problems with examples to get a better understanding of the algorithm. there are many online resources that provide rsa examples and practice problems.

An Example Of The Rsa Algorithm Pdf Cryptography Key Cryptography It covers multiple examples with different prime numbers and modulus values, demonstrating the rsa algorithm's processes. each question is followed by its solution, illustrating the calculations involved in rsa encryption and decryption. This repository contains the different cryptography protocols notes and its practical. cryptographic protocols rsa algorithm steps and solved example.pdf at main · hanseeka dhingana cryptographic protocols. Choose e such that 1 < e < φ (n) and e and φ (n) are coprime. let e = 7. compute a value for d such that (d * e) % φ (n) = 1. one solution is d = 3 [ (3 * 7) % 20 = 1]. 12.2.1 the rsa algorithm — putting to use the basic idea the basic idea described in the previous subsection can be used to create a confidential communication channel in the manner described here.
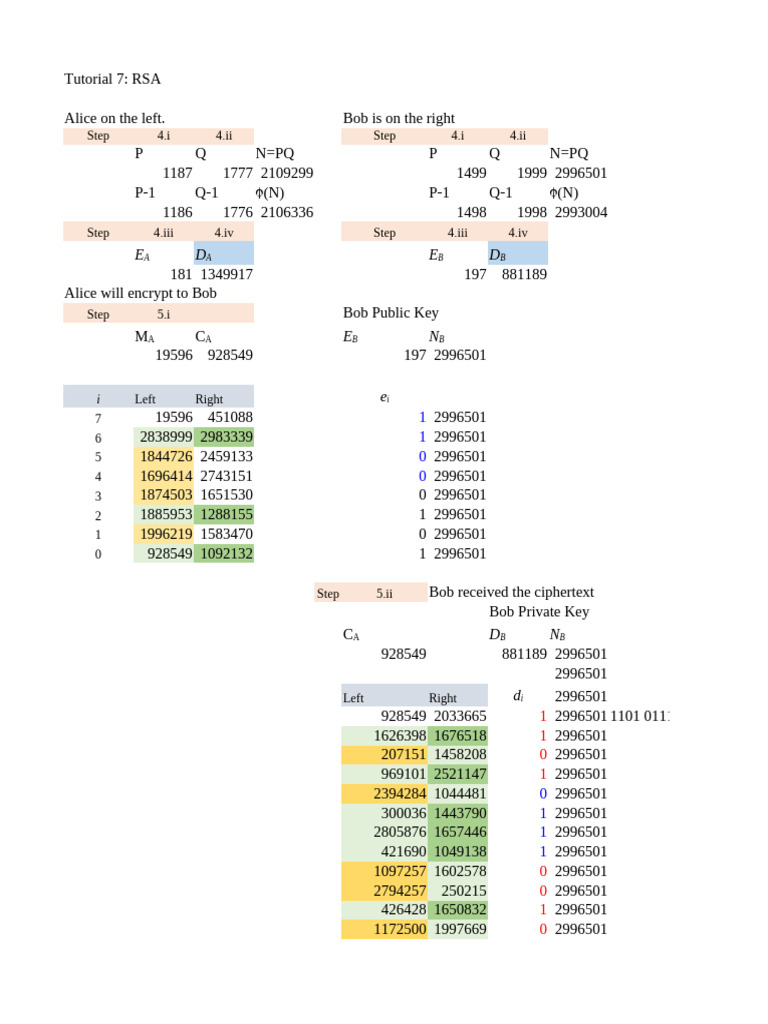
Tutorial 7 Rsa Sample Solution Pdf Public Key Cryptography Encryption Choose e such that 1 < e < φ (n) and e and φ (n) are coprime. let e = 7. compute a value for d such that (d * e) % φ (n) = 1. one solution is d = 3 [ (3 * 7) % 20 = 1]. 12.2.1 the rsa algorithm — putting to use the basic idea the basic idea described in the previous subsection can be used to create a confidential communication channel in the manner described here. The document contains solutions to multiple questions related to rsa and diffie hellman key exchange algorithms. for an rsa question, it calculates the private key d given the public key e and n. Practice with examples: practice solving rsa problems with examples to get a better understanding of the algorithm. there are many online resources that provide rsa examples and practice problems. User generated content is uploaded by users for the purposes of learning and should be used following studypool's honor code & terms of service. This paper focuses on the mathematics behind the algorithm, along with its core functionality and implementation. in addition, the code implementation and the encryption and decryption procedure.

Solution Rsa Algorithm Examples Studypool The document contains solutions to multiple questions related to rsa and diffie hellman key exchange algorithms. for an rsa question, it calculates the private key d given the public key e and n. Practice with examples: practice solving rsa problems with examples to get a better understanding of the algorithm. there are many online resources that provide rsa examples and practice problems. User generated content is uploaded by users for the purposes of learning and should be used following studypool's honor code & terms of service. This paper focuses on the mathematics behind the algorithm, along with its core functionality and implementation. in addition, the code implementation and the encryption and decryption procedure.

Solution Rsa Algorithm Examples Studypool User generated content is uploaded by users for the purposes of learning and should be used following studypool's honor code & terms of service. This paper focuses on the mathematics behind the algorithm, along with its core functionality and implementation. in addition, the code implementation and the encryption and decryption procedure.

Solution Rsa Algorithm Examples Studypool