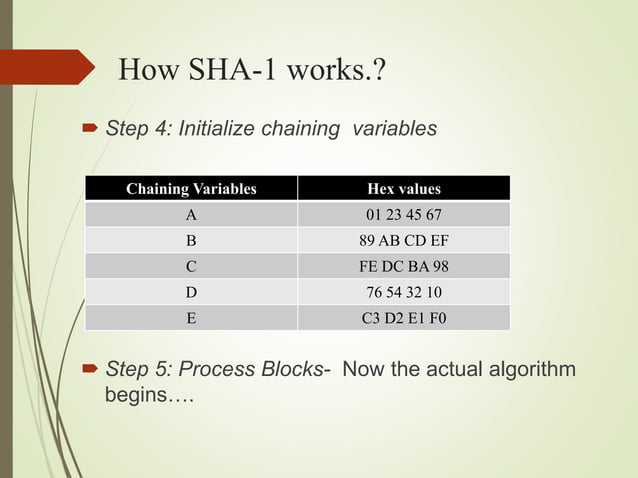
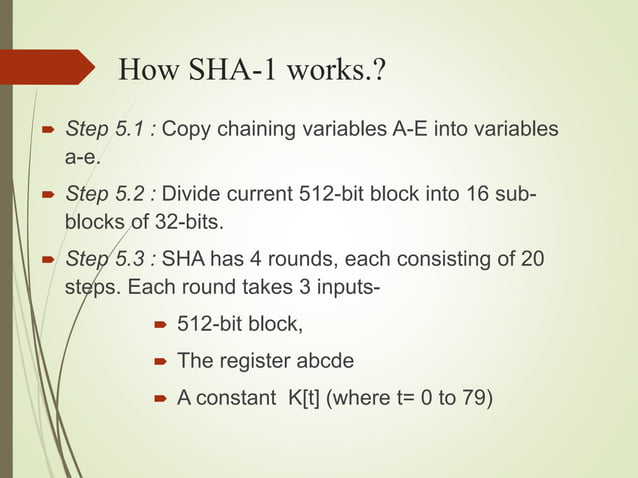
Sha Secure Hashing Algorithm Pptx It details the functioning of sha 1, including its input requirements, operational steps, and the processing of 512 bit blocks through multiple rounds and iterations. This is the main task of sha1 algorithm which loops through the padded and appended message in 512 bit blocks.
Sha Secure Hashing Algorithm Pptx Secure hash algorithm (sha 1).pptx free download as powerpoint presentation (.ppt .pptx), pdf file (.pdf), text file (.txt) or view presentation slides online. the document discusses the secure hash algorithm 1 (sha 1). Objectives of the topic after completing this topic, a student will be able to explain working of the secure hash algorithm (sha). the secure hash function (sha) figures and material in this topic have been adapted from. Sekolah teknik elektro dan informatika itb rinaldi munir ii4031 kriptografi dan koding secure hash algorithm(sha) sha adalahfungsi hash. Sha: secure hash algorithm developed by national institute of standard and technology (nist) based on the md4 fips 180 in 1993.
Sha Secure Hashing Algorithm Pptx Sekolah teknik elektro dan informatika itb rinaldi munir ii4031 kriptografi dan koding secure hash algorithm(sha) sha adalahfungsi hash. Sha: secure hash algorithm developed by national institute of standard and technology (nist) based on the md4 fips 180 in 1993. Sha is used for password logins, digital signatures, integrity checking, and authentication in applications like pgp, ssl, and ssh. download as a pptx, pdf or view online for free. The sha is called secure because it is designed to be computationally infeasible to recover a message corresponding to the message digest. any change to the message in transit will, with a very high probability, result in a different message digest, and the signature will fail to verify. 4.4.secure hash algorithm (sha).pptx free download as pdf file (.pdf), text file (.txt) or read online for free. the secure hash algorithm (sha) was developed by nist and nsa in 1993 for secure hashing, with several versions including sha 1 and sha 512. Sha 512 is closely modeled after sha 1 but produces a 512 bit digest and uses 1024 bit blocks. download as a pptx, pdf or view online for free.
Sha Secure Hashing Algorithm Pptx Sha is used for password logins, digital signatures, integrity checking, and authentication in applications like pgp, ssl, and ssh. download as a pptx, pdf or view online for free. The sha is called secure because it is designed to be computationally infeasible to recover a message corresponding to the message digest. any change to the message in transit will, with a very high probability, result in a different message digest, and the signature will fail to verify. 4.4.secure hash algorithm (sha).pptx free download as pdf file (.pdf), text file (.txt) or read online for free. the secure hash algorithm (sha) was developed by nist and nsa in 1993 for secure hashing, with several versions including sha 1 and sha 512. Sha 512 is closely modeled after sha 1 but produces a 512 bit digest and uses 1024 bit blocks. download as a pptx, pdf or view online for free.
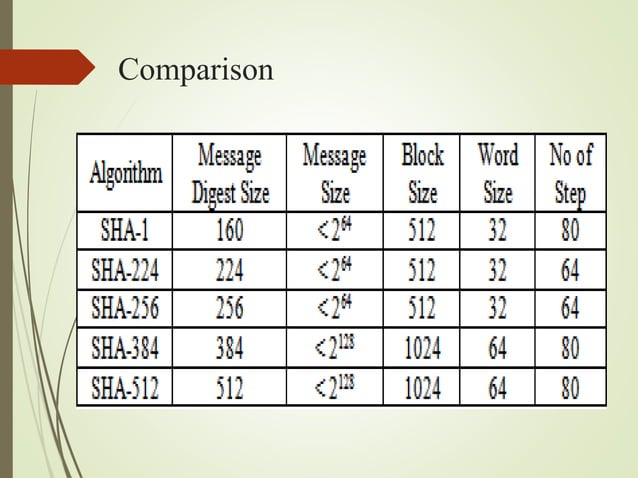
Sha Secure Hashing Algorithm Pptx 4.4.secure hash algorithm (sha).pptx free download as pdf file (.pdf), text file (.txt) or read online for free. the secure hash algorithm (sha) was developed by nist and nsa in 1993 for secure hashing, with several versions including sha 1 and sha 512. Sha 512 is closely modeled after sha 1 but produces a 512 bit digest and uses 1024 bit blocks. download as a pptx, pdf or view online for free.