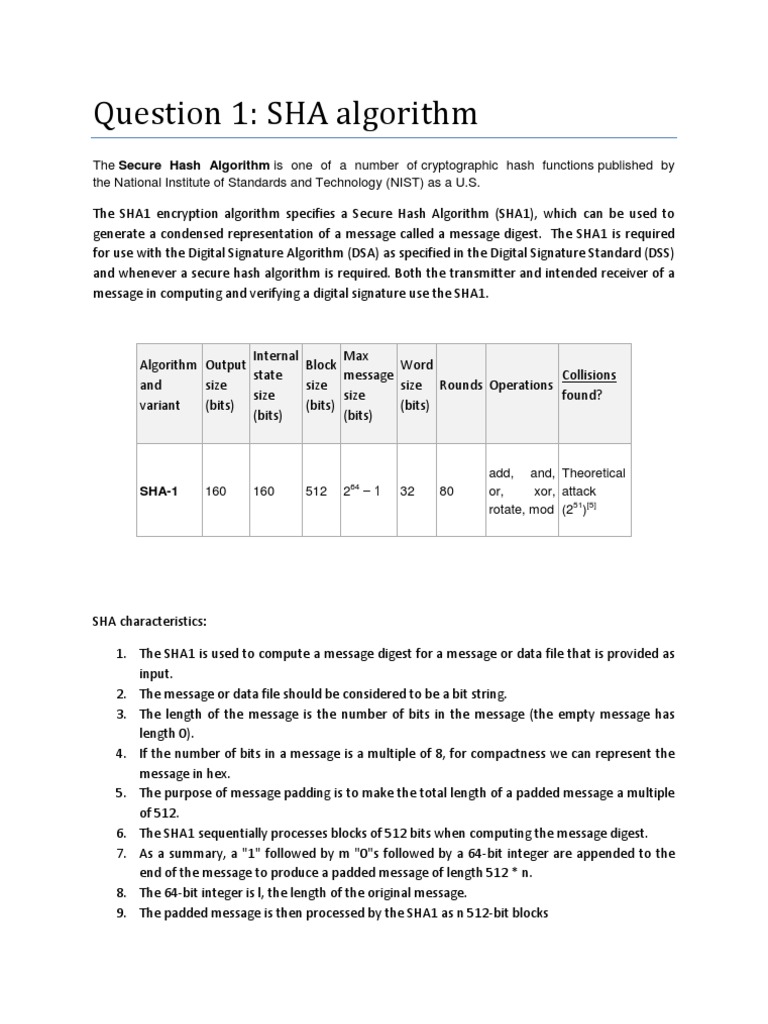
Question 1 Sha Algorithm Pdf Public Key Cryptography Military This standard specifies secure hash algorithms, sha 1, sha 224, sha 256, sha 384, sha 512, sha 512 224 and sha 512 256. all of the algorithms are iterative, one way hash functions that can process a message to produce a condensed representation called a message digest. It is essen tially a 256 bit blo c k cipher algorithm whic h encrypts the in termediate hash v alue using the message blo c kask ey . hence there are t w o main comp onen ts to describ e: (1) the sha 256 compression function, and (2) the sha 256 message sc hedule.

Sha Algorithm Pdf Secure hash algorithm (sha) sha adalah fungsi hash satu arah yang dibuat oleh nist dan digunakan bersama dss (digital signature standard). oleh nsa, sha dinyatakan sebagai standard fungsi hash satu arah. sha didasarkan pada md4 yang dibuat oleh ronald l. rivest dari mit. As a quick example of how the length of a message is included in what gets hashed, here is how the now not so popular sha 1 algorithm pads a message before it is hashed:. The sha has been developed over time by the national institute of standards and technology for security, optimal performance, and robustness. the best known hash standards are sha 1, sha 2, and. Sha 256 (secure hash algorithm, fips 182 2) is a cryptographic hash function with digest length of 256 bits. it is a keyless hash function; that is, an mdc (manipulation detection code).

Sha 512 Secure Hash Algorithm Pdf The sha has been developed over time by the national institute of standards and technology for security, optimal performance, and robustness. the best known hash standards are sha 1, sha 2, and. Sha 256 (secure hash algorithm, fips 182 2) is a cryptographic hash function with digest length of 256 bits. it is a keyless hash function; that is, an mdc (manipulation detection code). The purpose of this paper how to use sha 256 and sha 512 from sha 2 alogrithms. sha 2 is a family of two similar hash functions with different block sizes known as sha 256 and sha 512. This document announces the secure hash standard (shs), which specifies four secure hash algorithms sha 1, sha 256, sha 384, and sha 512 for computing a condensed representation called a message digest of electronic data. Sha originally designed by nist & nsa in 1993 was revised in 1995 as sha 1 us standard for use with dsa signature scheme standard is fips 180 1 1995, also internet rfc3174 nb. the algorithm is sha, the standard is shs based on design of md4 with key differences produces 160 bit hash values. In this work, we conduct a detailed and practical analysis of the sha 1 algorithm's theoretical elements and show how they have been implemented through the use of several different hash configurations.