
Sha 1 Hash Algorithm Board Infinity It works by padding the input message, appending the length, and then processing the message in 512 bit blocks through 80 processing steps using functions and constants to calculate new hash values. the final hash value after all blocks are processed represents the message digest. download as a ppt, pdf or view online for free. Secure hash algorithm (sha 1).pptx free download as powerpoint presentation (.ppt .pptx), pdf file (.pdf), text file (.txt) or view presentation slides online. the document discusses the secure hash algorithm 1 (sha 1).
Sha 1 Algorithm Pdf Sha didasarkan pada md4 yang dibuat oleh ronald l. rivest dari mit. algoritma sha menerima masukan berupa pesan dengan ukuran maksimum 264 bit (2.147.483.648 gigabyte) dan menghasilkan message digest yang panjangnya 160 bit, lebih panjang dari message digest yang dihasilkan oleh md5. The sha is called secure because it is designed to be computationally infeasible to recover a message corresponding to the message digest. any change to the message in transit will, with a very high probability, result in a different message digest, and the signature will fail to verify. Secure hash algorithm (sha) was developed by nist and nsa to hash messages into fixed length message digests. sha has multiple versions including sha 1, sha 2, and sha 3. In practical use cases, presenters can generate a sha 1 hash of their ppt files before sharing them with stakeholders or clients. recipients can then compute the hash of the received file and compare it with the original hash to confirm that the file remains unchanged.
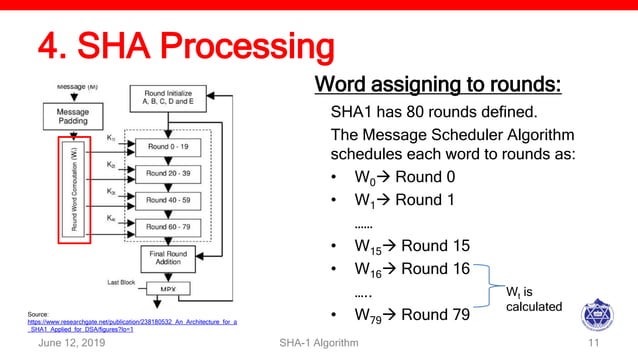
Sha 1 Algorithm Pdf Secure hash algorithm (sha) was developed by nist and nsa to hash messages into fixed length message digests. sha has multiple versions including sha 1, sha 2, and sha 3. In practical use cases, presenters can generate a sha 1 hash of their ppt files before sharing them with stakeholders or clients. recipients can then compute the hash of the received file and compare it with the original hash to confirm that the file remains unchanged. Secure hash algorithm (sha) is the most widely used hash function in recent years. developed by the national institute of standards and technology (nist) fips 180 in 1993. the secure hash function (sha) the actual standards document is entitled “secure hash standard.”. Learn about cryptographic hashing, sha 1 algorithm, collisions, and bitwise operations. explore the importance of hash functions, collision probabilities, and step by step sha 1 process. Sha 1 algorithm 160 bit hash using 512 bit blocks and 32 bit operations five passes (4 in md5 and 3 in md4) maximum message size is 264 bit 512 bits are expanded to 5x512 bits: nth word = xor of n 3, n 8, n 14, and n 16 in sha 1 these words are rotated left by one bit before xor total 80 words: w0, , w79 sha 1 algorithm (contd.) sha. Sha 1 is a secure hash function that converts input data into a fixed size hash value through a series of steps, ensuring data integrity and authenticity.