
Serialization Notes Code Decode Pdf Anonymous Function Method Serialization is the process of converting a java object into a byte stream that can be saved or transferred. to be serialized, a class must implement the serializable interface. deserialization is the reverse process taking the byte stream and recreating the original object. Check the use of unserialize () function and review how the external parameters are accepted. use a safe, standard data interchange format such as json (via json decode () and json encode ()) if you need to pass serialized data to the user.
Mario S Security Blog Decode Pdf And Extract Javascript Before we go into full detail on anonymous functions, we show how to use them in a few simple but powerful ways. the first is in a junit testing class to test whether a statement throws an exception, shown below. We learned about serialization and deserialization, how to generate serialized values, and how to unserialize them. we also reviewed the php code and uncovered the use of a code execution sink, namely the eval function. Serialization refers to the process of converting an object or data structure into a format that can be easily stored, transmitted, or shared across different systems. Anonymous functions help in reducing boilerplate code and make the code more readable and maintainable. this blog will delve into the fundamental concepts of anonymous functions in java, their usage methods, common practices, and best practices.
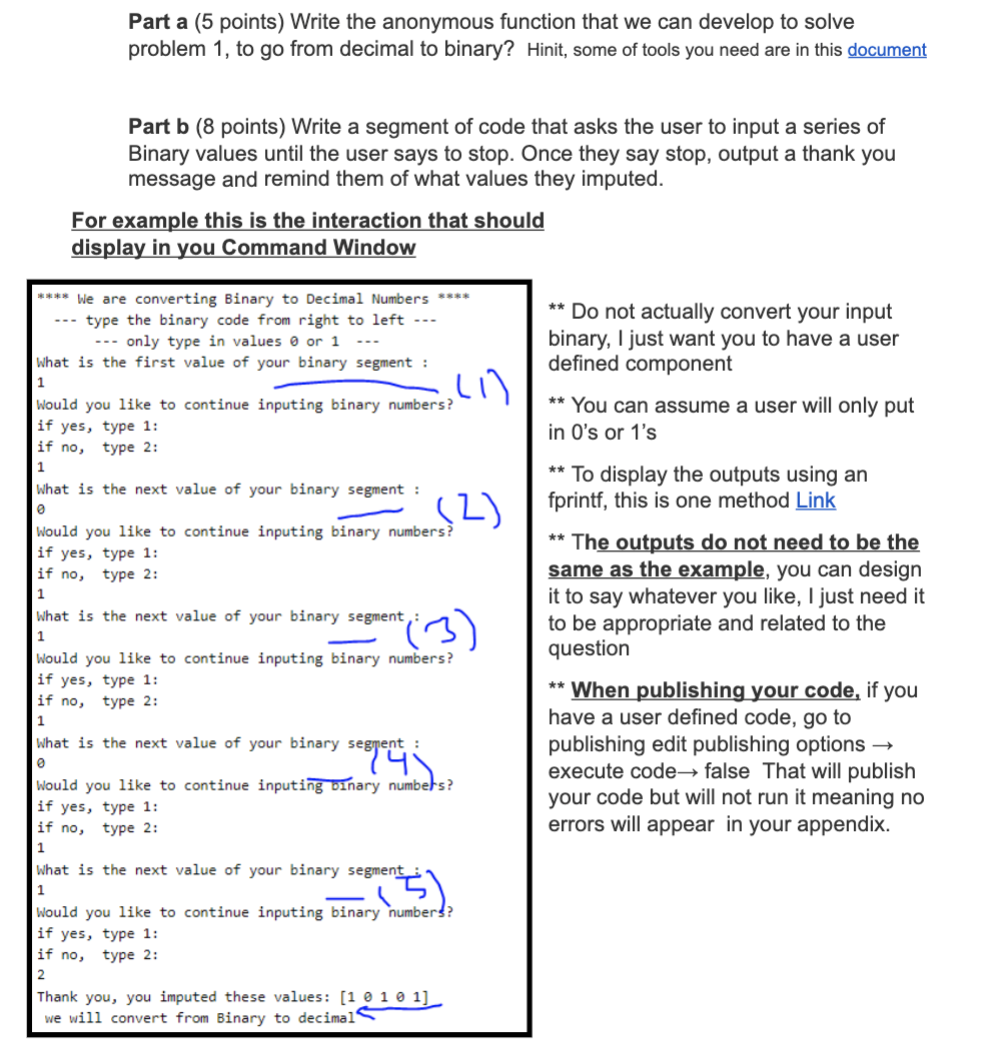
Solved Part A 5 Points Write The Anonymous Function That Chegg Serialization refers to the process of converting an object or data structure into a format that can be easily stored, transmitted, or shared across different systems. Anonymous functions help in reducing boilerplate code and make the code more readable and maintainable. this blog will delve into the fundamental concepts of anonymous functions in java, their usage methods, common practices, and best practices. Anonymous inner classes are very handy when you need to implement an interface which may not be highly reusable (and therefore not worth refactoring to its own named class). an instructive example is using a custom java.util parator
Github R89m Pdf Anonymisation Python Script For Automating The Anonymous inner classes are very handy when you need to implement an interface which may not be highly reusable (and therefore not worth refactoring to its own named class). an instructive example is using a custom java.util parator