
Rsa Examples Pdf Cryptography Applied Mathematics Rsa (rivest shamir adleman) algorithm is an asymmetric or public key cryptography algorithm which means it works on two different keys: public key and private key. A fully working example of rsa’s key generation, encryption, and signing capabilities. it should be noted here that what you see above is what is regarded as “vanilla” rsa.

Rsa Examples Pdf Cryptography Theoretical Computer Science Here you can see how to encrypt and decrypt using the rsa procedure step by step. the security of rsa is based on the fact that it is easy to calculate the product n n of two large prime numbers p p and q q. however, it is very difficult to determine the two primes only from the product n n. Small examples (like n=3233) help us understand the concept, but in practice rsa relies on extremely large keys (2048 bits or more) that make it virtually impossible to break with current. For example, rsa works with transport layer security (tls) to installation secure connections among net servers and browsers. also, rsa allows secure email communication by enabling message encryption and decryption. For another example, in the ssl tls protocol, an https web server makes its public key available through a certificate of the sort you’ll see in the next lecture.

Rsa Examples Pdf Encryption Applied Mathematics For example, rsa works with transport layer security (tls) to installation secure connections among net servers and browsers. also, rsa allows secure email communication by enabling message encryption and decryption. For another example, in the ssl tls protocol, an https web server makes its public key available through a certificate of the sort you’ll see in the next lecture. Choose e such that 1 < e < φ (n) and e and φ (n) are coprime. let e = 7. compute a value for d such that (d * e) % φ (n) = 1. one solution is d = 3 [ (3 * 7) % 20 = 1]. Master rsa encryption with our comprehensive tutorial. learn prime numbers, modular arithmetic, and public key cryptography with interactive examples and practice problems. Now let's demonstrate how the rsa algorithms works by a simple example in python. the below code will generate random rsa key pair, will encrypt a short message and will decrypt it back to its original form, using the rsa oaep padding scheme. You’ll see a real example, learn where rsa is used in real life, understand the types of attacks it can face, and how it compares to other methods like aes. let’s dive in!.
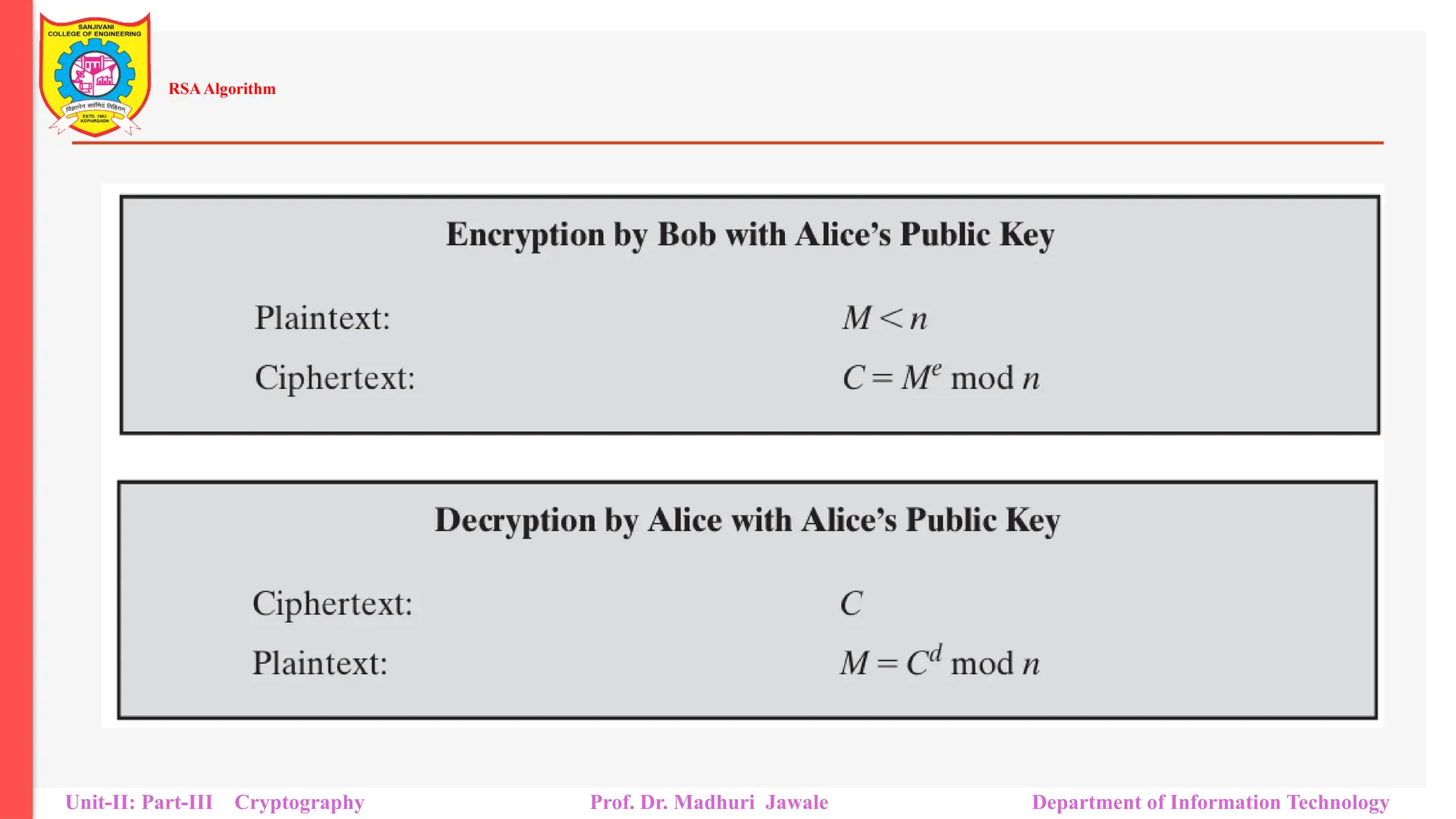
Cryptography Rsa Algorithm Rsa Examples Pptx Choose e such that 1 < e < φ (n) and e and φ (n) are coprime. let e = 7. compute a value for d such that (d * e) % φ (n) = 1. one solution is d = 3 [ (3 * 7) % 20 = 1]. Master rsa encryption with our comprehensive tutorial. learn prime numbers, modular arithmetic, and public key cryptography with interactive examples and practice problems. Now let's demonstrate how the rsa algorithms works by a simple example in python. the below code will generate random rsa key pair, will encrypt a short message and will decrypt it back to its original form, using the rsa oaep padding scheme. You’ll see a real example, learn where rsa is used in real life, understand the types of attacks it can face, and how it compares to other methods like aes. let’s dive in!.
Cryptography Rsa Algorithm Rsa Examples Pptx Now let's demonstrate how the rsa algorithms works by a simple example in python. the below code will generate random rsa key pair, will encrypt a short message and will decrypt it back to its original form, using the rsa oaep padding scheme. You’ll see a real example, learn where rsa is used in real life, understand the types of attacks it can face, and how it compares to other methods like aes. let’s dive in!.

Cryptography Rsa Algorithm Rsa Examples Pptx