
Speed Improvement For The Rsa Encryption Method Rsa encryption is a public key method that uses two large prime numbers to encrypt and decrypt information. it’s used in digital signatures, secure credit card transactions and other applications. Learn what rsa encryption is, how it works with public and private keys, and why it's still crucial for securing websites and digital communications.
How Rsa Encryption Works The rsa algorithm involves four steps: key generation, key distribution, public key operation (used for encryption or verifying a signature), and private key operation (used for decryption or signing a message). a basic principle behind rsa is the observation that it is practical to find three very large positive integers e, d, and n, such that for all integers x (0 ≤ x < n), both (xe)d and. In this method, the sender first takes the recipient’s public key and uses it to encrypt the message. once encrypted, the message becomes unreadable to anyone except the intended recipient. One of the most reliable and secure encryption algorithms available today is the rsa algorithm, which provides great encryption and performance using asymmetric cryptography, also known as. The rsa algorithm is one of the essential algorithms used in public key cryptosystems. understanding the rsa algorithm requires knowledge regarding number theory, modular arithmetic, etc., which is often beyond the knowledge pool of many beginners in cybersecurity.

Rsa Encryption Method Rsb Tech One of the most reliable and secure encryption algorithms available today is the rsa algorithm, which provides great encryption and performance using asymmetric cryptography, also known as. The rsa algorithm is one of the essential algorithms used in public key cryptosystems. understanding the rsa algorithm requires knowledge regarding number theory, modular arithmetic, etc., which is often beyond the knowledge pool of many beginners in cybersecurity. Transmitting confidential and sensitive data over the internet through this technology is safe due to its standard encryption method. it was developed by scientist rivest, shamir, and adleman at rsa data security inc. in 1978. Rsa gives the only known instantiation of a trapdoor one way permutation, which we will define shortly. rsa has a number of esoteric properties that are useful for advanced cryptographic constructions. for example, it gives a “group of unknown order”—see boneh shoup, chapter 10.9 for details. Rsa (rivest shamir adleman) is a famous encryption scheme that makes use of a combination of public and private keys. this means you have a non public key and one that can be shared publicly. each key can be used to encrypt data, but only the opposite can be decrypted. Rsa encryption may sound complex at first glance, but its underlying mechanisms are actually quite straightforward once broken down. this extensive guide aims to make rsa fully accessible to readers of all technical levels – no advanced math or cryptography expertise required!.

Rsb Tech Linkedin Transmitting confidential and sensitive data over the internet through this technology is safe due to its standard encryption method. it was developed by scientist rivest, shamir, and adleman at rsa data security inc. in 1978. Rsa gives the only known instantiation of a trapdoor one way permutation, which we will define shortly. rsa has a number of esoteric properties that are useful for advanced cryptographic constructions. for example, it gives a “group of unknown order”—see boneh shoup, chapter 10.9 for details. Rsa (rivest shamir adleman) is a famous encryption scheme that makes use of a combination of public and private keys. this means you have a non public key and one that can be shared publicly. each key can be used to encrypt data, but only the opposite can be decrypted. Rsa encryption may sound complex at first glance, but its underlying mechanisms are actually quite straightforward once broken down. this extensive guide aims to make rsa fully accessible to readers of all technical levels – no advanced math or cryptography expertise required!.
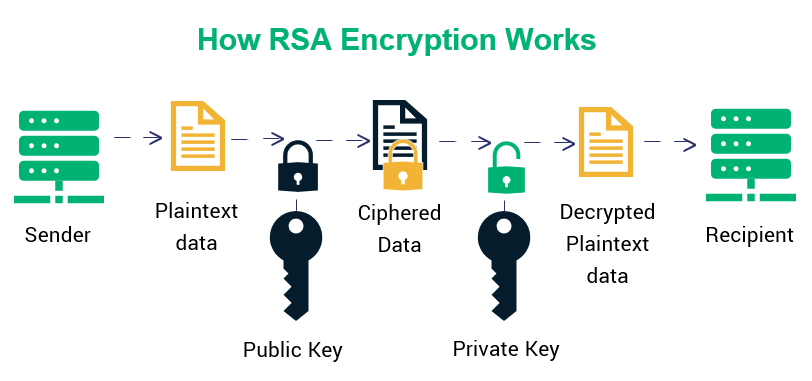
Rsa Cryptosystem Rsa (rivest shamir adleman) is a famous encryption scheme that makes use of a combination of public and private keys. this means you have a non public key and one that can be shared publicly. each key can be used to encrypt data, but only the opposite can be decrypted. Rsa encryption may sound complex at first glance, but its underlying mechanisms are actually quite straightforward once broken down. this extensive guide aims to make rsa fully accessible to readers of all technical levels – no advanced math or cryptography expertise required!.