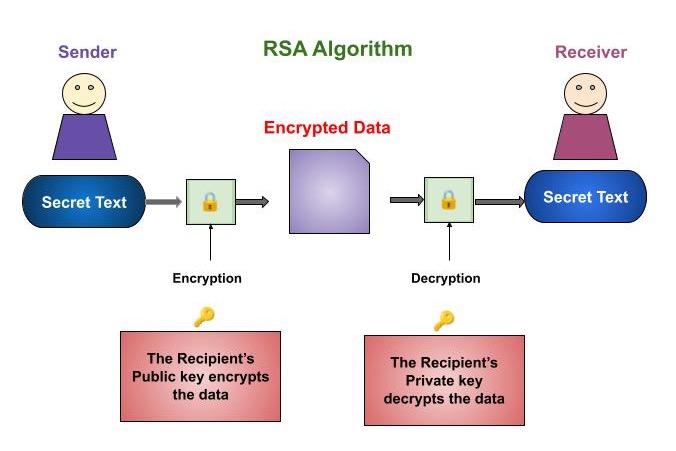
Cryptography Rsa Algorithm The rsa algorithm involves four steps: key generation, key distribution, public key operation (used for encryption or verifying a signature), and private key operation (used for decryption or signing a message). Public key cryptography: rsa algorithm is a public key cryptography algorithm, which means that it uses two different keys for encryption and decryption. the public key is used to encrypt the data, while the private key is used to decrypt the data.

Understanding The Rsa Algorithm In Cryptography Analytics Steps Learn how rsa works, its applications and security, and an example of encryption and decryption. rsa is a public key cryptography scheme that uses large prime numbers and modular arithmetic. Hu abstract. in the field of cryptography, which aims to ensure secure message communica tion, the rsa public key cryptosystem is the oldest widely applied secure data transmi. sion method. in this expository paper, we provide a historical and technical overview of the rsa . In this handbook, we’ll begin by exploring the foundational principles of the rsa algorithm. by examining its mathematical underpinnings and historical evolution, you will gain insight into the diverse array of attacks that have emerged over the years. Learn how rsa, a public key cryptography algorithm, works based on the difficulty of factoring large numbers. see the steps of the algorithm, examples, proof, and applications and vulnerabilities of rsa.

Rsa Algorithm Public Key Cryptography Ppt In this handbook, we’ll begin by exploring the foundational principles of the rsa algorithm. by examining its mathematical underpinnings and historical evolution, you will gain insight into the diverse array of attacks that have emerged over the years. Learn how rsa, a public key cryptography algorithm, works based on the difficulty of factoring large numbers. see the steps of the algorithm, examples, proof, and applications and vulnerabilities of rsa. Learn about the rsa algorithm, a crucial public key encryption method. discover how it secures data, its workings, and its applications in modern cryptography. Discover rsa cryptography in depth: its history, how the algorithm works, current applications, advantages, and future challenges. Rsa encryption, type of public key cryptography widely used for data encryption of e mail and other digital transactions over the internet. a user secretly chooses a pair of prime numbers p and q so large that factoring their product is well beyond projected computing capabilities. Rsa is an asymmetric cryptographic algorithm named after its inventors: ron rivest, adi shamir, and leonard adleman. it's one of the first public key cryptosystems and is widely used for secure data transmission, digital signatures, and key exchange.
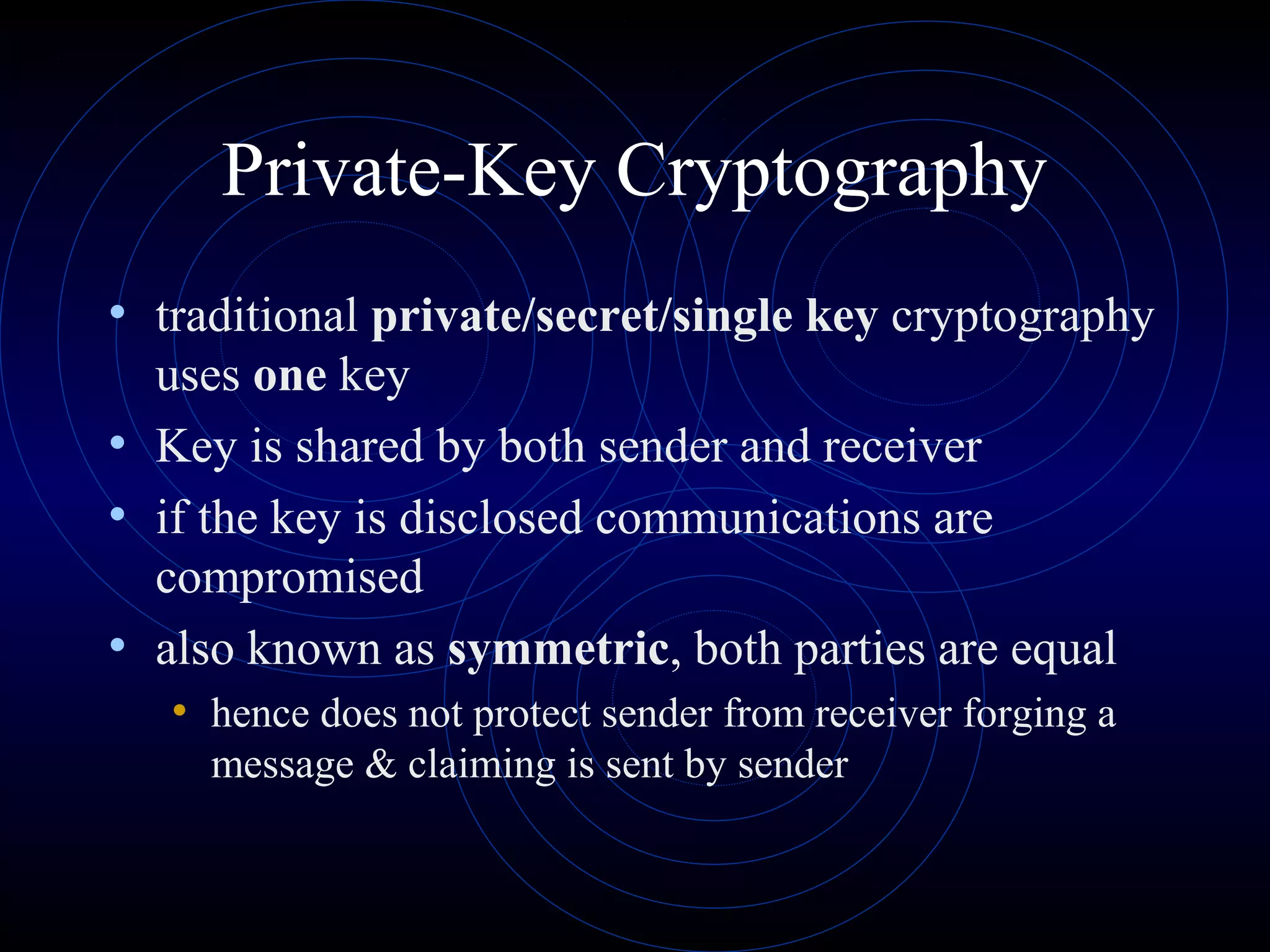
Rsa Algorithm Public Key Cryptography Ppt Learn about the rsa algorithm, a crucial public key encryption method. discover how it secures data, its workings, and its applications in modern cryptography. Discover rsa cryptography in depth: its history, how the algorithm works, current applications, advantages, and future challenges. Rsa encryption, type of public key cryptography widely used for data encryption of e mail and other digital transactions over the internet. a user secretly chooses a pair of prime numbers p and q so large that factoring their product is well beyond projected computing capabilities. Rsa is an asymmetric cryptographic algorithm named after its inventors: ron rivest, adi shamir, and leonard adleman. it's one of the first public key cryptosystems and is widely used for secure data transmission, digital signatures, and key exchange.
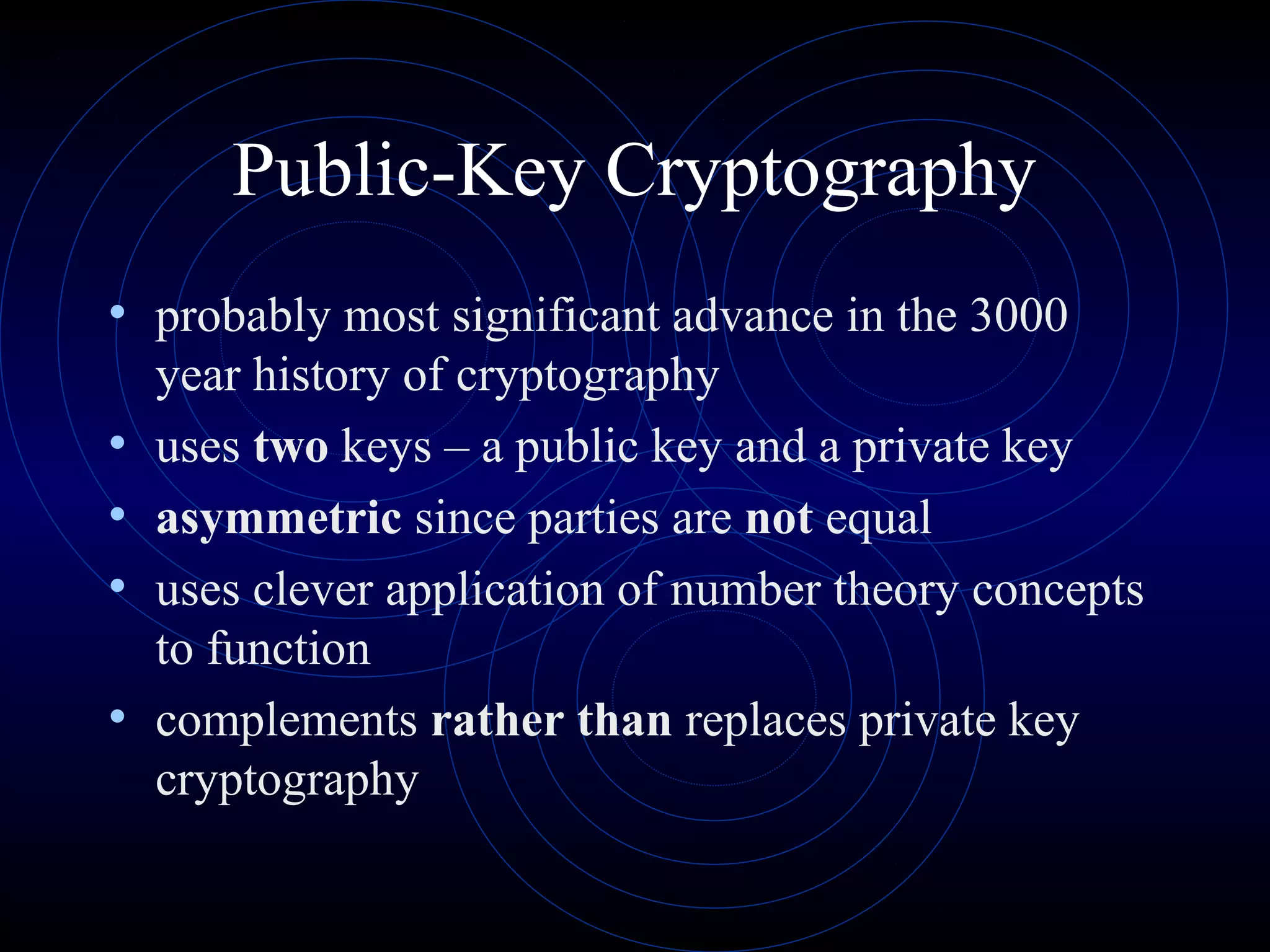
Rsa Algorithm Public Key Cryptography Ppt Rsa encryption, type of public key cryptography widely used for data encryption of e mail and other digital transactions over the internet. a user secretly chooses a pair of prime numbers p and q so large that factoring their product is well beyond projected computing capabilities. Rsa is an asymmetric cryptographic algorithm named after its inventors: ron rivest, adi shamir, and leonard adleman. it's one of the first public key cryptosystems and is widely used for secure data transmission, digital signatures, and key exchange.
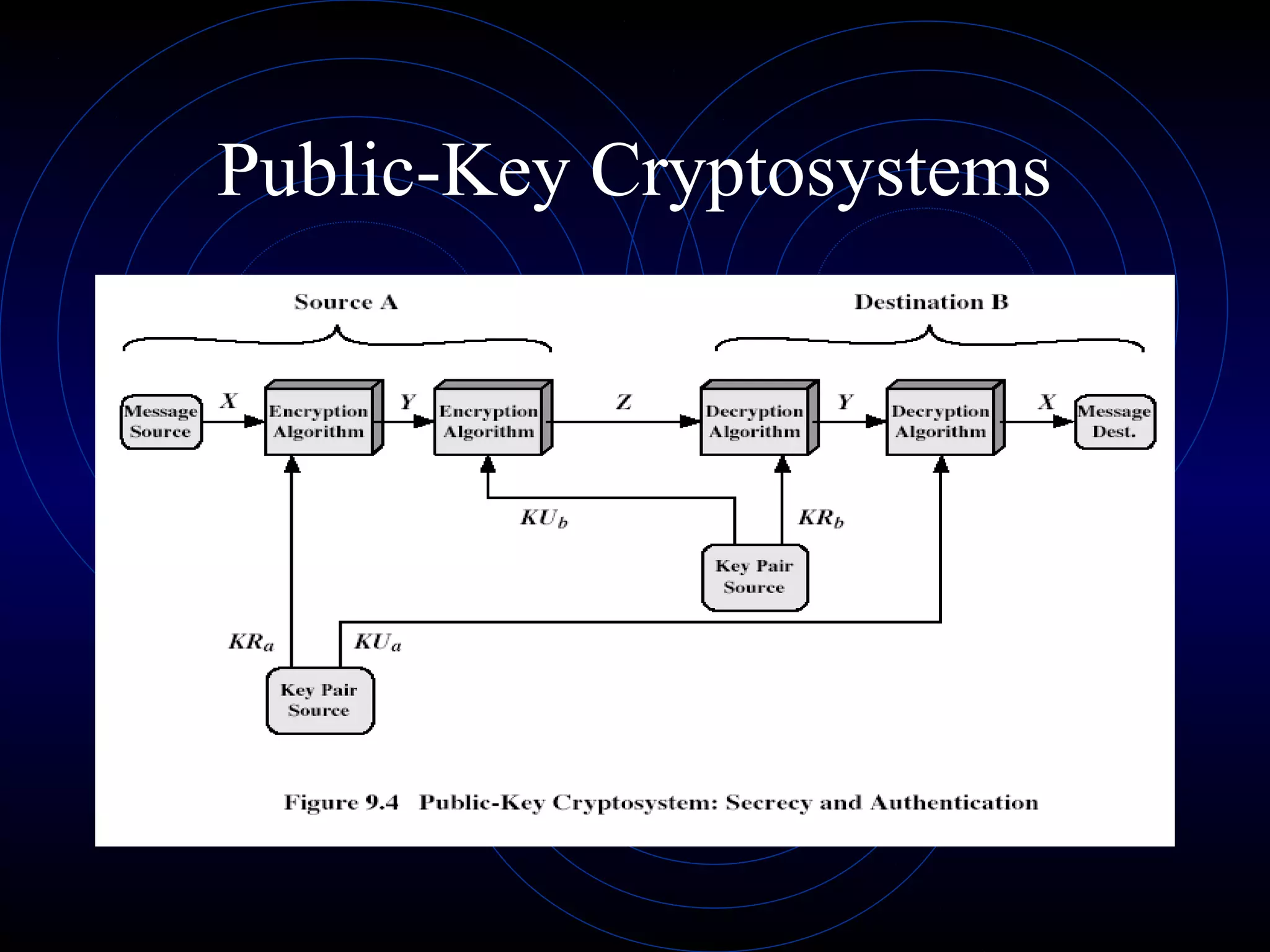
Rsa Algorithm Public Key Cryptography Ppt