
Rsa Type Pdf Prime Number Encryption Master rsa encryption with our comprehensive tutorial. learn prime numbers, modular arithmetic, and public key cryptography with interactive examples and practice problems. Next, we explained the rsa algorithm and showed the application of encryption decryption. finally, we explored the impracticality of a n factorization attack on the algorithm and stressed the importance of destroying everything but the public key and private key.

Rsa Encryption Prime Numbers Coprime Integer Pairs The Euler Phi This paper addresses the computational methods and challenges associated with prime number generation, a critical component in encryption algorithms for ensuring data security. Since every integer (except 0 and 1) can be factored into primes, these numbers are essential for constructing secure data transmission or generating cryptographic keys. here we will discuss the rsa algorithm and diffie hellman algorithm in detail, and some other applications based on primes. Unlike symmetric encryption, where the same key locks and unlocks data, rsa uses a public key to encrypt and a private key to decrypt. the link between them? two massive prime numbers. Through this optimization process, the paper offered a refined solution to the intricate balance between speed and security in prime number generation for the rsa encryption scheme.
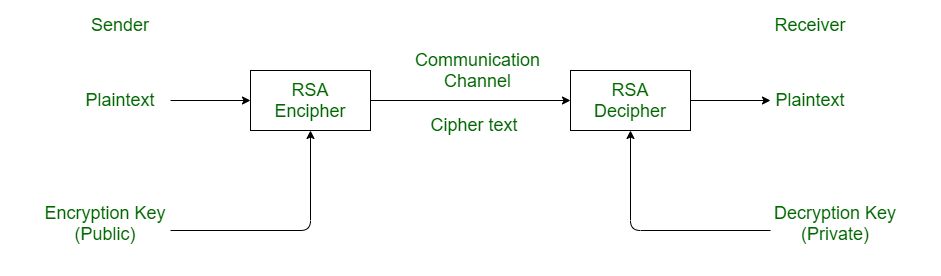
Prime Numbers And Rsa Encryption Databall Unlike symmetric encryption, where the same key locks and unlocks data, rsa uses a public key to encrypt and a private key to decrypt. the link between them? two massive prime numbers. Through this optimization process, the paper offered a refined solution to the intricate balance between speed and security in prime number generation for the rsa encryption scheme. The security of the rsa cryptosystem lies in the difficulty of factoring an integer that is the product of two large prime numbers. several businesses rely on the rsa cryptosystem for making sure that sensitive information does not end up in the wrong hands. The concept of an n base (or base n) number system is important in cryptography for several reasons, from binary computations in algorithms to encoding and even novel cryptographic schemes. Numerous cryptographic primitives rely on prime numbers, a good representative being the rsa cryptosystem used for encryption or digital signatures. the output distribution of the primes that are generated also matters. Learn about prime numbers, primality testing, and the rsa encryption algorithm. this academic paper explains the mathematical foundations and provides a practical example of encryption and decryption, highlighting the importance of large prime numbers in cryptography.

Appnbytes Rsa Encryption Prime Numbers Appenate The security of the rsa cryptosystem lies in the difficulty of factoring an integer that is the product of two large prime numbers. several businesses rely on the rsa cryptosystem for making sure that sensitive information does not end up in the wrong hands. The concept of an n base (or base n) number system is important in cryptography for several reasons, from binary computations in algorithms to encoding and even novel cryptographic schemes. Numerous cryptographic primitives rely on prime numbers, a good representative being the rsa cryptosystem used for encryption or digital signatures. the output distribution of the primes that are generated also matters. Learn about prime numbers, primality testing, and the rsa encryption algorithm. this academic paper explains the mathematical foundations and provides a practical example of encryption and decryption, highlighting the importance of large prime numbers in cryptography.

Rsa Encryption Encrypting Data Prime Numbers Modular Arithmetic Numerous cryptographic primitives rely on prime numbers, a good representative being the rsa cryptosystem used for encryption or digital signatures. the output distribution of the primes that are generated also matters. Learn about prime numbers, primality testing, and the rsa encryption algorithm. this academic paper explains the mathematical foundations and provides a practical example of encryption and decryption, highlighting the importance of large prime numbers in cryptography.

Encryption With Prime Numbers Learn Java Coding