
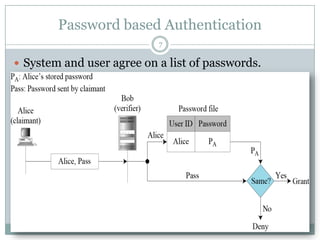
Cryptography Pptx Lecture File For Student S Pptx This document discusses password based cryptography and common attacks on passwords. it introduces password based authentication techniques that use hashing, salting, and iteration counts to strengthen passwords. This document discusses password and authentication in cyber security. it covers topics like password management, hashing passwords with salt to make them more secure, choosing suitable passwords to prevent brute force attacks, updating passwords regularly, and multi factor authentication.
Password Based Cryptography Pptx Authenticationis the act of establishing or confirming something (or someone) as authentic, that is, that claims made by or about the subject are true. This browser version is no longer supported. please upgrade to a supported browser. Discover the intricacies of pkcs #5, a standard for password based cryptography, with details on key derivation, encryption schemes, and message authentication. Course goal: realize when to consult an expert! cryptography (historically) “…the art of writing or solving codes…” historically, cryptography focused exclusively on ensuring private communication between two parties sharing secret information in advance using “codes” (aka private key encryption.

Password Based Cryptography Pptx Discover the intricacies of pkcs #5, a standard for password based cryptography, with details on key derivation, encryption schemes, and message authentication. Course goal: realize when to consult an expert! cryptography (historically) “…the art of writing or solving codes…” historically, cryptography focused exclusively on ensuring private communication between two parties sharing secret information in advance using “codes” (aka private key encryption. 7.8.1 password based encoding with jce|. 7.8.2 decorator design pattern. 7.9 digital signatures. 7.10 public key infrastructure, certificates and certification authorities. 7.10.1 java keystores and keytool. 7.11 java policy files. 7.12 digital signatures for java code. These attacks leverage additional information based on physical implementation of a cryptographic algorithm, including hardware used to encrypt or decrypt data. Symmetric (secret key) encryption and the des and aes algorithms. asymmetric (public key) encryption and the rsa algorithm. key exchange protocols and certificates. digital signatures. cryptographic hash functions. csc 519 information security. concepts of encryption. cryptography is rooted in higher mathematics: . group and field theory. Explore our fully editable and customizable powerpoint presentations on cryptography, designed to enhance your understanding of this essential field in information security.
Password Based Cryptography Pptx 7.8.1 password based encoding with jce|. 7.8.2 decorator design pattern. 7.9 digital signatures. 7.10 public key infrastructure, certificates and certification authorities. 7.10.1 java keystores and keytool. 7.11 java policy files. 7.12 digital signatures for java code. These attacks leverage additional information based on physical implementation of a cryptographic algorithm, including hardware used to encrypt or decrypt data. Symmetric (secret key) encryption and the des and aes algorithms. asymmetric (public key) encryption and the rsa algorithm. key exchange protocols and certificates. digital signatures. cryptographic hash functions. csc 519 information security. concepts of encryption. cryptography is rooted in higher mathematics: . group and field theory. Explore our fully editable and customizable powerpoint presentations on cryptography, designed to enhance your understanding of this essential field in information security.
Password Based Cryptography Pptx Symmetric (secret key) encryption and the des and aes algorithms. asymmetric (public key) encryption and the rsa algorithm. key exchange protocols and certificates. digital signatures. cryptographic hash functions. csc 519 information security. concepts of encryption. cryptography is rooted in higher mathematics: . group and field theory. Explore our fully editable and customizable powerpoint presentations on cryptography, designed to enhance your understanding of this essential field in information security.
Password Based Cryptography Pptx