
Okta Palo Alto Networks Okta palo alto networks combine leading identity, network and cloud security technologies to deliver end to end protection across users, devices, applications, and infrastructure. Learn how palo alto networks and okta deliver comprehensive identity protection, secure remote access and zero trust solutions to safeguard your it ecosystem and prevent credential theft.
Okta Palo Alto Networks Learn how you can put the world class unit 42 incident response team on speed dial. cyberforce represents the top 1% of partner engineers trusted for their security expertise. why palo alto networks? under attack? for technical details and to configure the integration between our two products, download this integration guide. For technical details and to configure the integration between our two products, download secure remote access with palo alto networks and okta briefs. Palo alto networks (panw) stock fell $146 and okta (okta) dropped to $73.50 after a leak about anthropic’s claude mythos ai model sparked fears of commoditized cybersecurity solutions. Palo alto networks and okta have partnered to help organizations bring identity and security together for the enforcement of access policy, regardless of where customer applications reside.

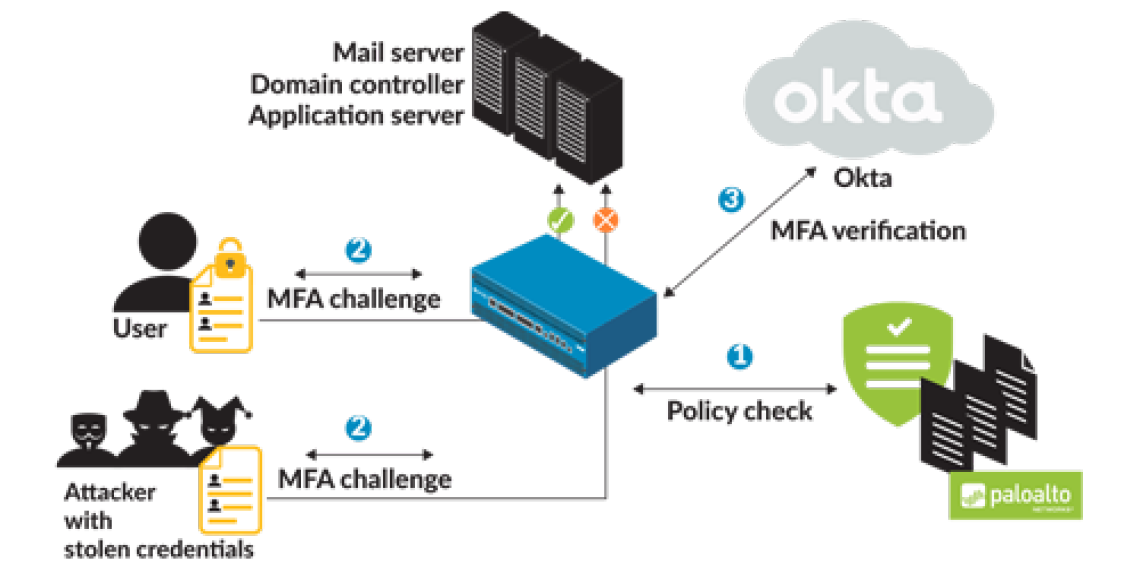
Okta Palo Alto Networks Palo alto networks (panw) stock fell $146 and okta (okta) dropped to $73.50 after a leak about anthropic’s claude mythos ai model sparked fears of commoditized cybersecurity solutions. Palo alto networks and okta have partnered to help organizations bring identity and security together for the enforcement of access policy, regardless of where customer applications reside. Palo alto networks and okta work together to prevent successful phishing attacks and credential abuse as well as simplify mfa deployment and management. This playbook explores how okta’s identity first security works with palo alto networks’ advanced threat protection to strengthen authentication, automate threat response, and secure hybrid workforces. With palo alto networks and okta, your remote workers enjoy the same simple, convenient identity management and secure connection experience whether they are accessing the inter net; saas; or public, hybrid, or private clouds. Okta and palo alto networks interoperate through either radius or saml 2.0. for each palo alto gateway, you can assign one or more authentication providers. each authentication profile maps to an authentication server, which can be radius, tacas , ldap, etc.
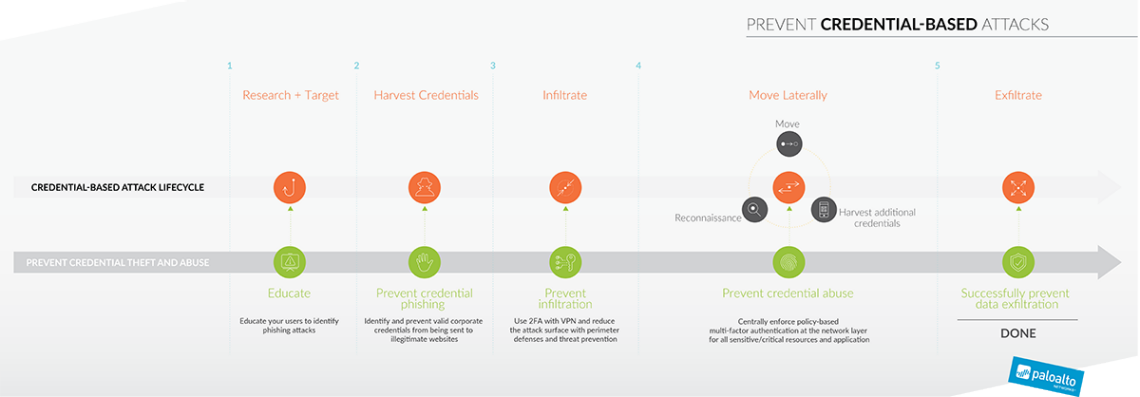
Okta Palo Alto Networks Palo alto networks and okta work together to prevent successful phishing attacks and credential abuse as well as simplify mfa deployment and management. This playbook explores how okta’s identity first security works with palo alto networks’ advanced threat protection to strengthen authentication, automate threat response, and secure hybrid workforces. With palo alto networks and okta, your remote workers enjoy the same simple, convenient identity management and secure connection experience whether they are accessing the inter net; saas; or public, hybrid, or private clouds. Okta and palo alto networks interoperate through either radius or saml 2.0. for each palo alto gateway, you can assign one or more authentication providers. each authentication profile maps to an authentication server, which can be radius, tacas , ldap, etc.

Palo Alto Networks Globalprotect Okta With palo alto networks and okta, your remote workers enjoy the same simple, convenient identity management and secure connection experience whether they are accessing the inter net; saas; or public, hybrid, or private clouds. Okta and palo alto networks interoperate through either radius or saml 2.0. for each palo alto gateway, you can assign one or more authentication providers. each authentication profile maps to an authentication server, which can be radius, tacas , ldap, etc.