Tutorial 7 Rsa Sample Solution Pdf Public Key Cryptography Encryption We propose a variation on the rsa cryptosystem: namely, an extension of the rsa en cryption and decryption methods to matrix values in addition to scalars. we first explore the mathematics behind the rsa cryptosystem, after which, we investigate the theory of the pro posed variation to the system. Abstract this paper describes a new method for performing secure encryption of blocks of streaming data. this algorithm is an extension of the rsa encryption algorithm.

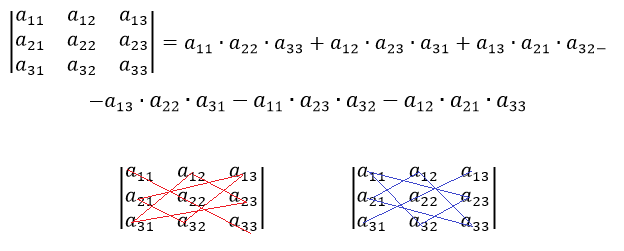
Rsa Matrix Pdf This document proposes a matrix extension of the rsa cryptosystem, allowing encryption and decryption methods to apply to matrix values instead of just scalar integers. This project demonstrates a simple rsa matrix encryption system using python and a makefile to automate the process. the system reads a text input, converts it to numerical values, and performs encryption using a matrix transformation. In this section we will examine a method of encryption that uses matrix multiplication and matrix inverses. this method, known as the hill algorithm, was created by lester hill, a mathematics professor who taught at several us colleges and also was involved with military encryption. Section 2 provides a high level overview of how matrix based rsa encryption works, and illustrates encryption and decryption of a simple message using this approach.

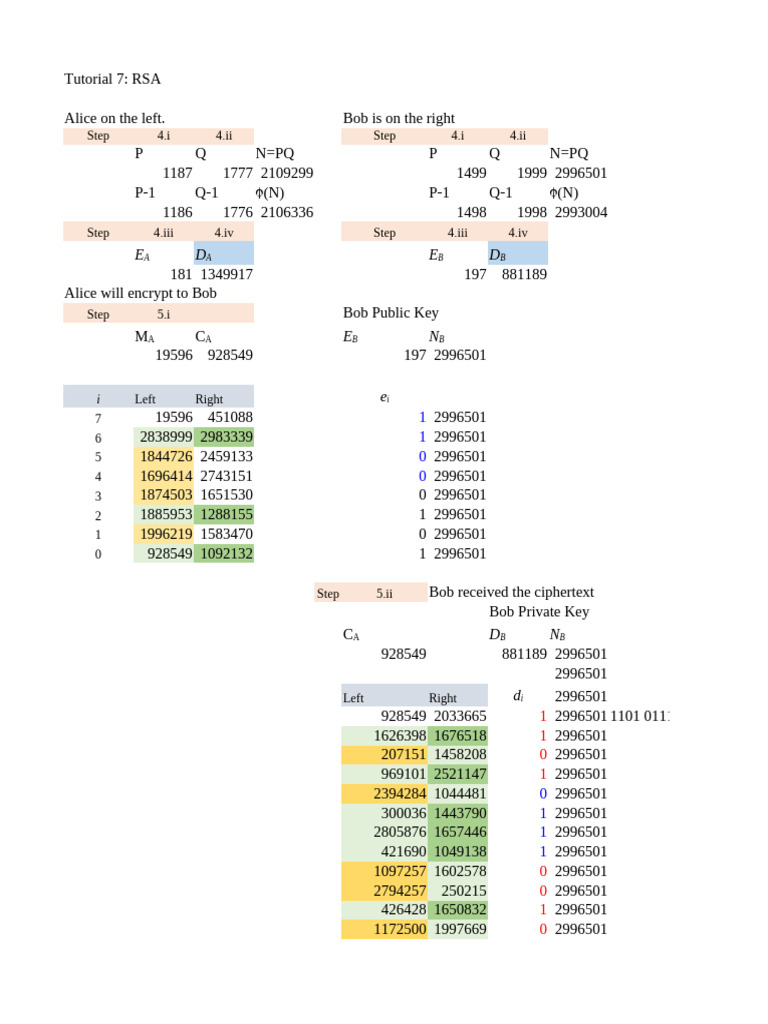
Block Diagram Of Rsa Encryption Algorithms Iv Design Of The Rsa In this section we will examine a method of encryption that uses matrix multiplication and matrix inverses. this method, known as the hill algorithm, was created by lester hill, a mathematics professor who taught at several us colleges and also was involved with military encryption. Section 2 provides a high level overview of how matrix based rsa encryption works, and illustrates encryption and decryption of a simple message using this approach. A new matrix extension of the rsa algorithm is proposed which is based on the cayley hamilton theor. m and a one way function. the security of this algo rithm rests upon both that of the rsa. Rsa (rivest shamir adleman) algorithm is an asymmetric or public key cryptography algorithm which means it works on two different keys: public key and private key. the public key is used for encryption and is known to everyone, while the private key is used for decryption and must be kept secret by the receiver. The journey from understanding the basic factorization problem to breaking rsa challenges in ctfs provides deep insight into cryptographic principles that extend far beyond rsa itself. In rsa, we have two large primes p and q, a modulus n = pq, an encryption exponent e and a decryption exponent d that satisfy ed = 1 mod (p 1) (q 1). the public key is the pair (n,e) and the private key is d.
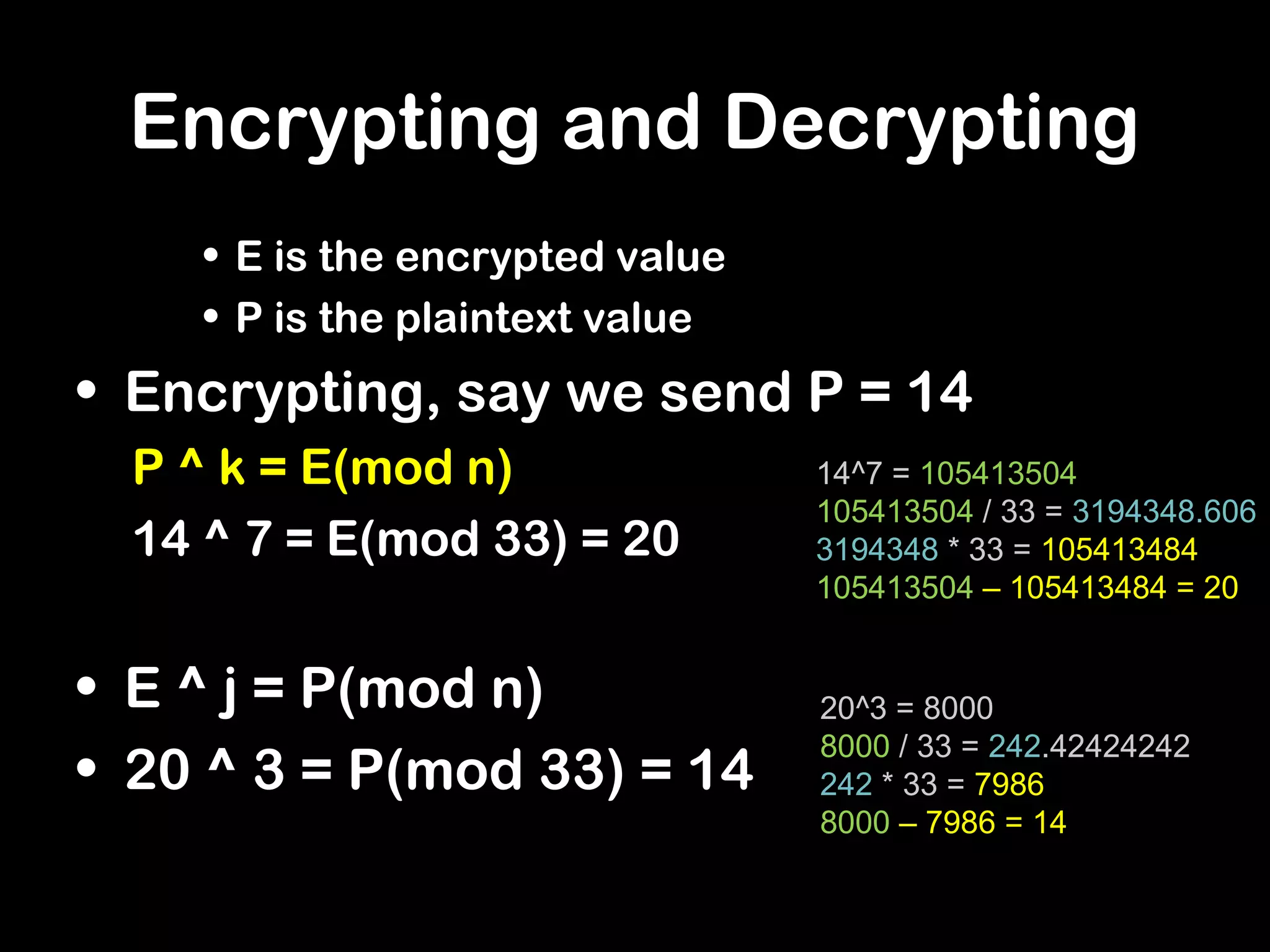
Rsa Encryption Ppt Information And Network Security Computing A new matrix extension of the rsa algorithm is proposed which is based on the cayley hamilton theor. m and a one way function. the security of this algo rithm rests upon both that of the rsa. Rsa (rivest shamir adleman) algorithm is an asymmetric or public key cryptography algorithm which means it works on two different keys: public key and private key. the public key is used for encryption and is known to everyone, while the private key is used for decryption and must be kept secret by the receiver. The journey from understanding the basic factorization problem to breaking rsa challenges in ctfs provides deep insight into cryptographic principles that extend far beyond rsa itself. In rsa, we have two large primes p and q, a modulus n = pq, an encryption exponent e and a decryption exponent d that satisfy ed = 1 mod (p 1) (q 1). the public key is the pair (n,e) and the private key is d.
Github Nightlyds Matrix Encryption Matrix Encryption And Decryption The journey from understanding the basic factorization problem to breaking rsa challenges in ctfs provides deep insight into cryptographic principles that extend far beyond rsa itself. In rsa, we have two large primes p and q, a modulus n = pq, an encryption exponent e and a decryption exponent d that satisfy ed = 1 mod (p 1) (q 1). the public key is the pair (n,e) and the private key is d.