
Simplified Aes Example Pdf Key Cryptography Cryptography Let's illustrate the aes encryption and aes decryption concepts through working source code in python. the first example below will illustrate a simple password based aes encryption (pbkdf2 aes ctr) without message authentication (unauthenticated encryption). Aes is a method of turning normal text into unreadable text (encryption) and then back to normal (decryption) using the same secret key (symmetric algorithm). when you need to protect sensitive information—such as passwords, financial data, or confidential messages—encryption is essential.

2 4 1 Aes Example 1 Pdf Aes (advanced encryption standard) is a symmetric key cryptographic algorithm and also a block cipher that is superior and replaces the des. this article aims to break down the tutorial,. Learn to use aes 256 bit encryption to create secure passwords and decryption for password validation in java, with examples. This code snippet demonstrates aes (advanced encryption standard) encryption and decryption using java's built in security features. aes is a symmetric key algorithm widely used for securing data due to its speed and strong security. Simplified aes example free download as pdf file (.pdf), text file (.txt) or read online for free. the document provides a step by step example of encrypting and decrypting a 16 bit plaintext using a simplified version of the aes algorithm.

Example Aes 2 Pdf Cipher Applied Mathematics This code snippet demonstrates aes (advanced encryption standard) encryption and decryption using java's built in security features. aes is a symmetric key algorithm widely used for securing data due to its speed and strong security. Simplified aes example free download as pdf file (.pdf), text file (.txt) or read online for free. the document provides a step by step example of encrypting and decrypting a 16 bit plaintext using a simplified version of the aes algorithm. This example uses aes gcm to perform an aes encryption on a string, and a file. examples included password bases aes encryption. Aes is a method of turning normal text into unreadable text (encryption) and then back to normal (decryption) using the same secret key (symmetric algorithm). when you need to protect sensitive information—such as passwords, financial data, or confidential messages—encryption is essential. Aes example round 1, substitution bytes • current state matrix is 00 3c 6e 47 1f 4e 22 74 0e 08 1b 31 54 59 0b 1a • substitute each entry (byte) of current state matrix by corresponding entry in aes s box • for instance: byte 6e is substituted by entry of s box in row 6 and column e, i.e., by 9f • this leads to new state matrix 63 eb. In the following piece, you’ll learn what aes is, how its main components work, and how to correctly use aes encryption and decryption in your project. there are dozens of encryption algorithms out there, but the most commonly used is aes―short for advanced encryption standard, also known as rijndael.

Aes Solved Example On Encryption All Rounds Pdf This example uses aes gcm to perform an aes encryption on a string, and a file. examples included password bases aes encryption. Aes is a method of turning normal text into unreadable text (encryption) and then back to normal (decryption) using the same secret key (symmetric algorithm). when you need to protect sensitive information—such as passwords, financial data, or confidential messages—encryption is essential. Aes example round 1, substitution bytes • current state matrix is 00 3c 6e 47 1f 4e 22 74 0e 08 1b 31 54 59 0b 1a • substitute each entry (byte) of current state matrix by corresponding entry in aes s box • for instance: byte 6e is substituted by entry of s box in row 6 and column e, i.e., by 9f • this leads to new state matrix 63 eb. In the following piece, you’ll learn what aes is, how its main components work, and how to correctly use aes encryption and decryption in your project. there are dozens of encryption algorithms out there, but the most commonly used is aes―short for advanced encryption standard, also known as rijndael.
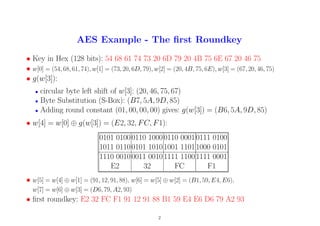
Aes Solved Example On Encryption All Rounds Pdf Aes example round 1, substitution bytes • current state matrix is 00 3c 6e 47 1f 4e 22 74 0e 08 1b 31 54 59 0b 1a • substitute each entry (byte) of current state matrix by corresponding entry in aes s box • for instance: byte 6e is substituted by entry of s box in row 6 and column e, i.e., by 9f • this leads to new state matrix 63 eb. In the following piece, you’ll learn what aes is, how its main components work, and how to correctly use aes encryption and decryption in your project. there are dozens of encryption algorithms out there, but the most commonly used is aes―short for advanced encryption standard, also known as rijndael.
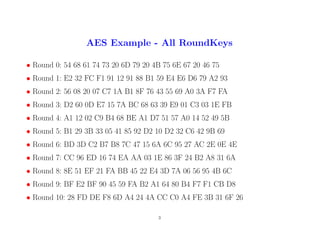
Aes Solved Example On Encryption All Rounds Pdf