
Homomorphic Encryption Part iii: generic fully homomorphic encryption explains the generic techniques of fhe adopted by many existing schemes, such as homomorphic addition, multiplication, modulus switching, and key switching. Previously we explained in depth and using simple language about homomorphic encryption and its use cases. in this article, we will introduce a new approach to homomorphic encryption, developed by our team.
Homomorphic Encryption Part 3 Information security — fully homomorphic encryption — part 3: mechanisms for arithmetic on approximate numbers. Homomorphic encryption is a form of encryption with an additional evaluation capability for computing over encrypted data without access to the secret key. the result of such a computation remains encrypted. Homomorphic encryption, in simple terms, is a cryptographic approach that permits information to be processed even as it remains in an encrypted form. unlike conventional encryption, which calls for statistics to be decrypted for any significant operation, homomorphic encryption permits computations to be performed at once on encrypted statistics. We are a community of researchers and developers interested in advancing homomorphic encryption and other secure computation techniques.

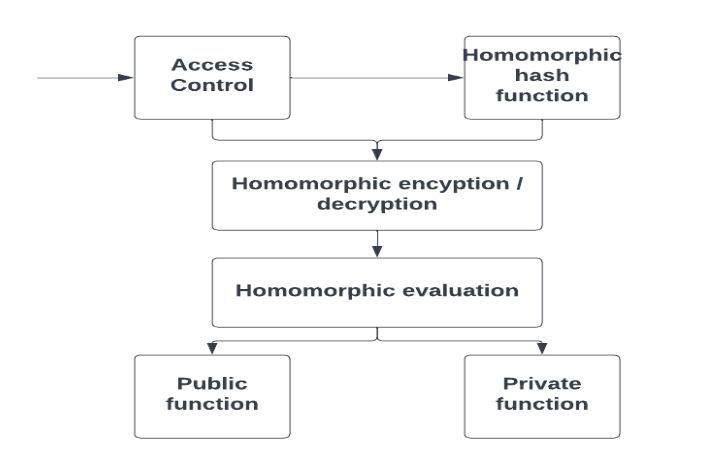
Homomorphic Encryption Part 3 Homomorphic encryption, in simple terms, is a cryptographic approach that permits information to be processed even as it remains in an encrypted form. unlike conventional encryption, which calls for statistics to be decrypted for any significant operation, homomorphic encryption permits computations to be performed at once on encrypted statistics. We are a community of researchers and developers interested in advancing homomorphic encryption and other secure computation techniques. This repository implements homomorphic encryption using the ckks scheme. it supports encoding and decoding, encryption and decryption, and addition and multiplication for approximate arithmetic ope. Encryption schemes have evolved tremendously over the past decades, and homomorphic encryption (he) is one of the most fascinating areas. while most people are familiar with partially homomorphic encryption (phe) schemes like rsa or paillier that support either addition or multiplication, the boneh goh nissim (bgn) cryptosystem, introduced in 2005, by dan boneh and eu jin goh from stanford. The two clients use threshold fully homomorphic encryption that allows them to use a joint public key to encrypt their datasets. the joint public key is used to encrypt the data. This chapter provides an overview of homomorphic encryption, beginning with an introduction to public key encryption and the foundational concepts of homomorphic encryption.