Hashing Algorithm Network Encyclopedia What is hashing algorithm? a mathematical procedure that takes the information contained in files and scrambles it to create a fixed length string of numbers and characters called a hash. Hashing refers to the process of generating a small sized output (that can be used as index in a table) from an input of typically large and variable size. hashing uses mathematical formulas known as hash functions to do the transformation.

Hashing Algorithm Network Encyclopedia The secure hash algorithms are a family of cryptographic hash functions published by the national institute of standards and technology (nist) as a u.s. federal information processing standard (fips), including:. Currently only the four fixed length sha 3 algorithms are approved hash algorithms, providing alternatives to the sha 2 family of hash functions. the xofs can be specialized to hash functions, subject to additional security considerations. The important message digest (md) algorithms include md2, md4, and md5, all of which produce a 128 bit hash value. the md algorithms are commonly used to generate a digital signature from a message. Collision resolution strategy • algorithm and data structure to handle two keys that hash to the same index.

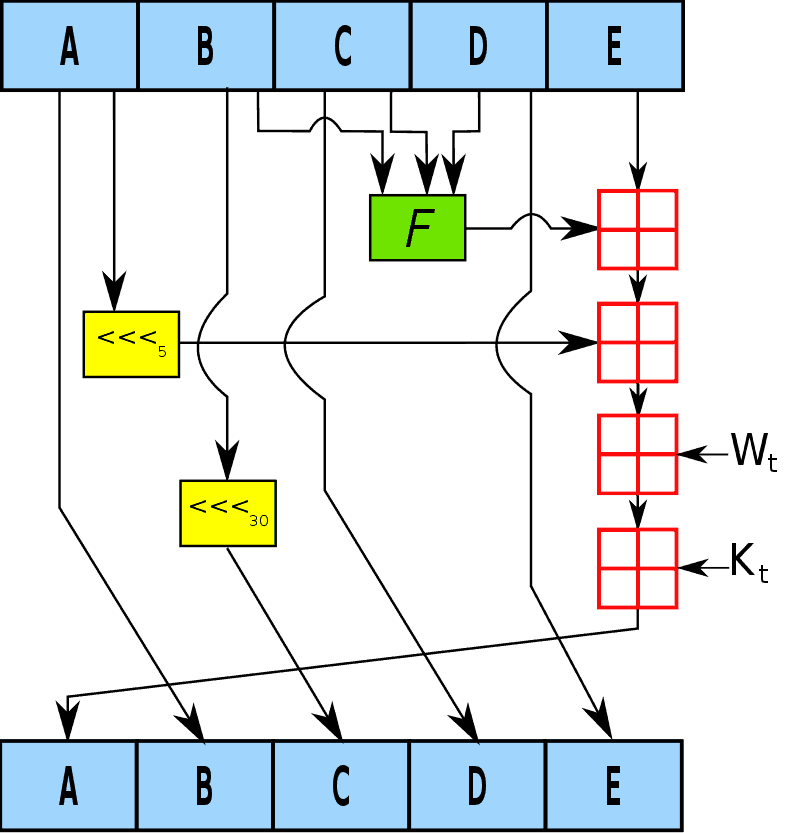
Hashing Algorithm Projects In Network Security Guidance Network The important message digest (md) algorithms include md2, md4, and md5, all of which produce a 128 bit hash value. the md algorithms are commonly used to generate a digital signature from a message. Collision resolution strategy • algorithm and data structure to handle two keys that hash to the same index. This research paper delves into the principles and applications of hashing, focusing on popular cryptographic hash functions like md5, sha 1, sha 2, and sha 3. A hashing algorithm is defined as a technique that applies a hash function to data to create a unique digital fingerprint, or hash value, which is fixed in size. it is a one way process that ensures data integrity and authentication, producing different outputs for any changes in the input data. As to why we append a single bit of ’1’ at the end of the actual message, see section 15.7.3 where i have described my python and perl implementations of the sha 1 hashing algorithm. Hashing is used in cryptography for secure (encrypted) communication and maintaining data integrity. for example, when you communicate over a wifi network: is this website secure?.

Understanding The Hashing Algorithm This research paper delves into the principles and applications of hashing, focusing on popular cryptographic hash functions like md5, sha 1, sha 2, and sha 3. A hashing algorithm is defined as a technique that applies a hash function to data to create a unique digital fingerprint, or hash value, which is fixed in size. it is a one way process that ensures data integrity and authentication, producing different outputs for any changes in the input data. As to why we append a single bit of ’1’ at the end of the actual message, see section 15.7.3 where i have described my python and perl implementations of the sha 1 hashing algorithm. Hashing is used in cryptography for secure (encrypted) communication and maintaining data integrity. for example, when you communicate over a wifi network: is this website secure?.
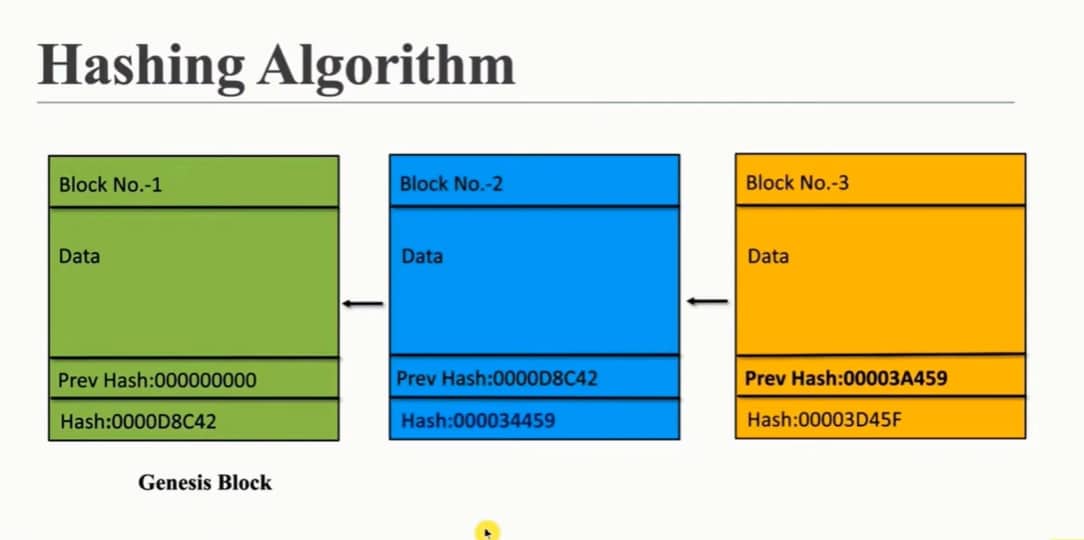
What Is Hashing Algorithm In Blockchain As to why we append a single bit of ’1’ at the end of the actual message, see section 15.7.3 where i have described my python and perl implementations of the sha 1 hashing algorithm. Hashing is used in cryptography for secure (encrypted) communication and maintaining data integrity. for example, when you communicate over a wifi network: is this website secure?.

What S A Hashing Algorithm An Introduction