
Hash Functions Cryptography Powerpoint Presentation Notes Security Cryptographic hash functions are algorithms that take a variable length input and produce a fixed length output (hash value) that uniquely identifies the input. Hash functions cryptography powerpoint presentation notes security free download as powerpoint presentation (.ppt), pdf file (.pdf), text file (.txt) or view presentation slides online. cryptographic hash functions condense arbitrary messages into fixed size hashes.
Ppt Cryptography And Network Security Various Hash Algorithms Learn about the structure, properties, and applications of cryptographic hash functions in ensuring data integrity and security. explore hash function usages, such as file integrity verification and password storage. understand properties like preimage resistance and collision resistance. * to get some feel for the security considerations involved in cryptographic hash functions, we present two simple, insecure hash functions in this section. one of the simplest hash functions is the bit by bit exclusive or (xor) of every block, which can be expressed as shown. Hash functions a hash function maps a message of an arbitrary length to a m bit output output known as the fingerprint or the message digest what is an example of hash functions?. Introduction to applied cryptography. instructor: ali aydin selcuk. cryptographic hash functions maps an arbitrary length input to a fixed size output. was originally proposed to generate input to digital signatures.
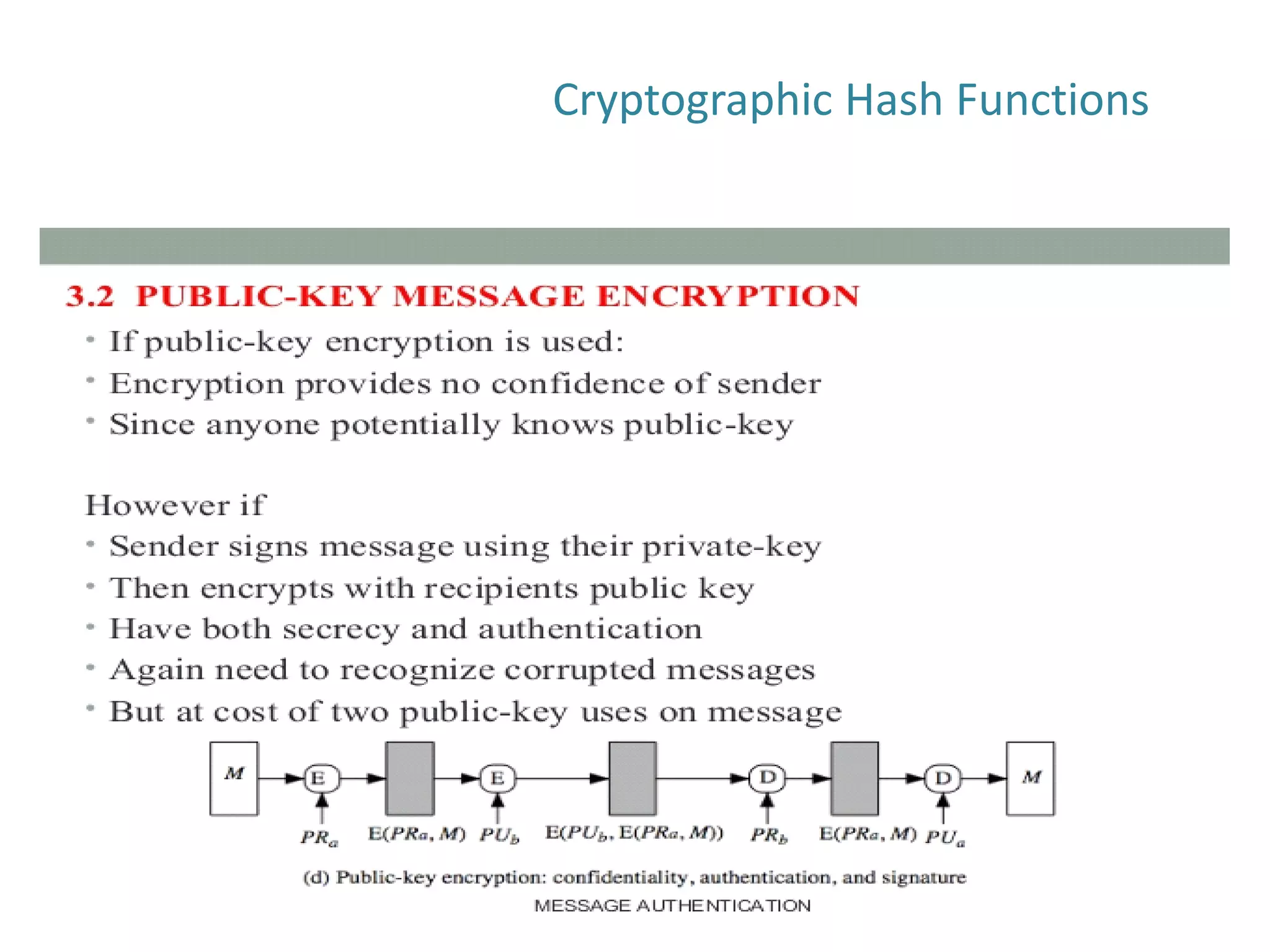
Cryptography Network Security Cryptographic Hash Functions Pdf Hash functions a hash function maps a message of an arbitrary length to a m bit output output known as the fingerprint or the message digest what is an example of hash functions?. Introduction to applied cryptography. instructor: ali aydin selcuk. cryptographic hash functions maps an arbitrary length input to a fixed size output. was originally proposed to generate input to digital signatures. Transcript and presenter's notes title: cryptographic hash functions 1 cryptographic hash functions cs 470 introduction to applied cryptography instructor ali aydin selcuk 2 cryptographic hash functions maps an arbitrary length input to a fixed size output. was originally proposed to generate input to digital signatures. desirable features. Unlock the power of cryptography with our comprehensive powerpoint presentation on hash functions. this engaging deck covers essential concepts, applications, and real world examples, making it perfect for professionals and students alike. Hash functions • a hash function maps a message of an arbitrary length to a m bit output – output known as the fingerprint or the message digest • what is an example of hash functions?. Basic uses of hash function. h = h(m) m is a variable length message, h is a fixed length hash value, h is a hash function. the hash value is appended at the source. the receiver authenticates the message by recomputing the hash value. because the hash function itself is not considered to be secret, some means is required to protect the hash value.
Cryptography Network Security Cryptographic Hash Functions Pdf Transcript and presenter's notes title: cryptographic hash functions 1 cryptographic hash functions cs 470 introduction to applied cryptography instructor ali aydin selcuk 2 cryptographic hash functions maps an arbitrary length input to a fixed size output. was originally proposed to generate input to digital signatures. desirable features. Unlock the power of cryptography with our comprehensive powerpoint presentation on hash functions. this engaging deck covers essential concepts, applications, and real world examples, making it perfect for professionals and students alike. Hash functions • a hash function maps a message of an arbitrary length to a m bit output – output known as the fingerprint or the message digest • what is an example of hash functions?. Basic uses of hash function. h = h(m) m is a variable length message, h is a fixed length hash value, h is a hash function. the hash value is appended at the source. the receiver authenticates the message by recomputing the hash value. because the hash function itself is not considered to be secret, some means is required to protect the hash value.