
M 3 Cryptographic Hash Functions Pdf Public Key Cryptography A hash function is a function that maps data of arbitrary size to fixed size values, used to index a hash table or perform other operations. learn about the types, design, implementation and applications of hash functions, as well as their advantages and limitations. Hash functions are a fundamental concept in computer science and play a crucial role in various applications such as data storage, retrieval, and cryptography. a hash function creates a mapping from an input key to an index in hash table.

Hash Function Pdf Cryptography Secure Communication Learn what a hash function is, how it works, and why it matters for cybersecurity. explore common hashing algorithms, their strengths and limitations, and how they power digital signatures, blockchain, and more. Learn everything about hash functions, their properties, and applications in cryptography, data integrity, and password storage. discover how they work, their benefits, and common challenges in this comprehensive guide. Explore the in depth guide on hashing and hash functions. common examples, working, benefits and algorithms. Learn what hash functions are, how they work, and why they are important in cryptography. see examples of hash functions such as sha 256 and sha3 256, and how to use them in python and javascript.

Hash Functions And What They Offer For Security In Cryptography Ip Explore the in depth guide on hashing and hash functions. common examples, working, benefits and algorithms. Learn what hash functions are, how they work, and why they are important in cryptography. see examples of hash functions such as sha 256 and sha3 256, and how to use them in python and javascript. Learn about hash functions, their types, and when to use them hash functions are like digital fingerprints for the process of hashing. they take any data and create a unique code from it. A hash function is a deterministic function that maps a set of strings or keys to a set of bounded integers. it can also include objects, data structures, or anything that can be represented unambiguously as a string. Learn what hash functions are, how they work, and why they are important in cryptography. explore the key properties, characteristics, and applications of hash functions, such as md5, sha, and ripemd. List of hash functions this is a list of hash functions, including cyclic redundancy checks, checksum functions, and cryptographic hash functions.
4 Hash Functions Cryptography Lecture Notes Learn about hash functions, their types, and when to use them hash functions are like digital fingerprints for the process of hashing. they take any data and create a unique code from it. A hash function is a deterministic function that maps a set of strings or keys to a set of bounded integers. it can also include objects, data structures, or anything that can be represented unambiguously as a string. Learn what hash functions are, how they work, and why they are important in cryptography. explore the key properties, characteristics, and applications of hash functions, such as md5, sha, and ripemd. List of hash functions this is a list of hash functions, including cyclic redundancy checks, checksum functions, and cryptographic hash functions.
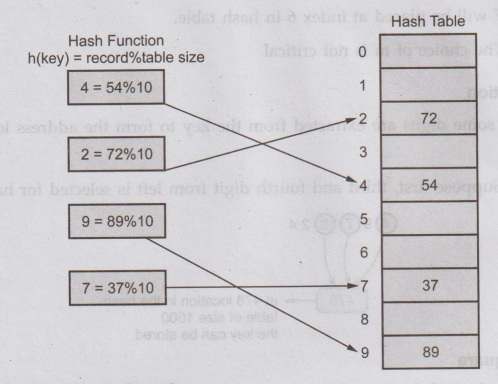
Hash Functions Types Learn what hash functions are, how they work, and why they are important in cryptography. explore the key properties, characteristics, and applications of hash functions, such as md5, sha, and ripemd. List of hash functions this is a list of hash functions, including cyclic redundancy checks, checksum functions, and cryptographic hash functions.