
Analysis Of Various Hash Function Pdf Cryptography Secure This document discusses hash functions and their analysis for a network security seminar. it begins by defining a hash function as a mathematical function that converts a large amount of data into a small string of integers. A hash function that satisfies the first five properties in table 11.1 is referred to as a weak hash function. if the sixth property, collision resistant, is also satisfied, then it is referred to as a strong hash function.
Ppt Hash Function Powerpoint Presentation Free Download Id 4653079 Hash functions cryptography powerpoint presentation notes security free download as powerpoint presentation (.ppt), pdf file (.pdf), text file (.txt) or view presentation slides online. cryptographic hash functions condense arbitrary messages into fixed size hashes. Generalize hash function notation: a hash function contains two arguments now: (i) key value, and (ii) probe number h(k,p), p=0,1, ,m 1 probe sequences

Chapter 7 Hash Function In Cryptography Ppt Introduction to applied cryptography. instructor: ali aydin selcuk. cryptographic hash functions maps an arbitrary length input to a fixed size output. was originally proposed to generate input to digital signatures. Collision function is quadratic. the popular choice is f(i) = i2. if the hash function evaluates to h and a search in cell h is inconclusive, we try cells h 12, h 22, … h i2. i.e. it examines cells 1,4,9 and so on away from the original probe. Learn about cryptographic hash functions, one way vs. collision resistance, the birthday paradox, and more. explore hash functions in password hashing, software integrity, and common hash functions like sha 256. Hash functions a hash function maps a message of an arbitrary length to a m bit output output known as the fingerprint or the message digest what is an example of hash functions?. This document discusses cryptographic hash functions including their applications in message authentication and digital signatures. it describes the requirements for hash functions to be secure including resistance to brute force attacks and cryptanalysis. Hashing.ppt free download as powerpoint presentation (.ppt), pdf file (.pdf), text file (.txt) or view presentation slides online. the document discusses hash tables and hashing.
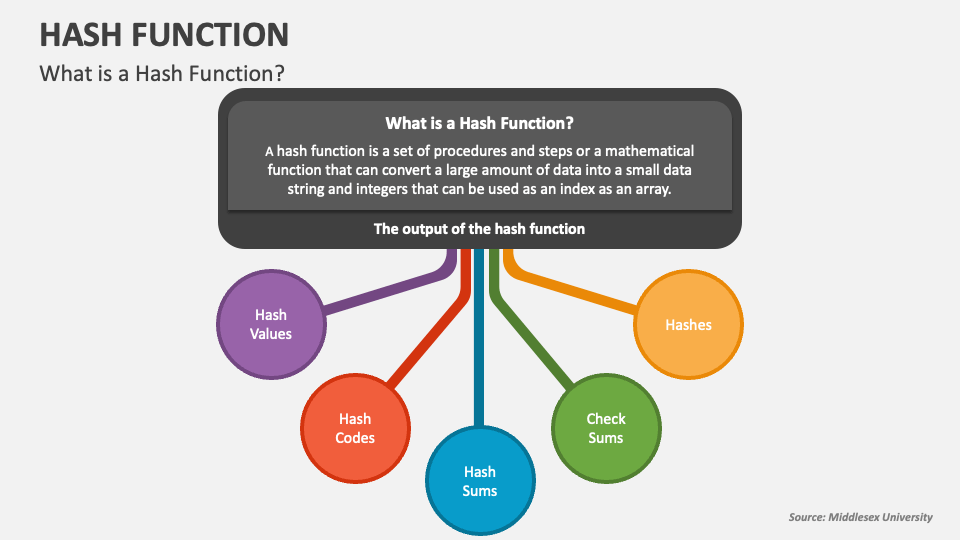
Hash Function Powerpoint Presentation Slides Ppt Template Learn about cryptographic hash functions, one way vs. collision resistance, the birthday paradox, and more. explore hash functions in password hashing, software integrity, and common hash functions like sha 256. Hash functions a hash function maps a message of an arbitrary length to a m bit output output known as the fingerprint or the message digest what is an example of hash functions?. This document discusses cryptographic hash functions including their applications in message authentication and digital signatures. it describes the requirements for hash functions to be secure including resistance to brute force attacks and cryptanalysis. Hashing.ppt free download as powerpoint presentation (.ppt), pdf file (.pdf), text file (.txt) or view presentation slides online. the document discusses hash tables and hashing.