
Standard Cryptography Template En Pdf Contribute to kalanamith cryptography template development by creating an account on github. It took some time to complete, but it’s now ready. built with #rust, this #cli application provides a robust and secure way to handle cryptographic operations.
Github Codeesam Cryptography Contribute to kalanamith kalanamith development by creating an account on github. Contribute to kalanamith kalanamith development by creating an account on github. The aim of this post is to provide a simple, ready for use latex article template for writing research papers on cryptography. this is the setup i generally use in my papers, and i figured it could be useful, e.g. for phd student in crypto. I made a \ (\latex\) template for cryptologic research papers at github rickfreemancui crypto latex template. it features: cryptobib as a submodule, which means that your can access the latest cryptobib in your project by running the git pull commands.
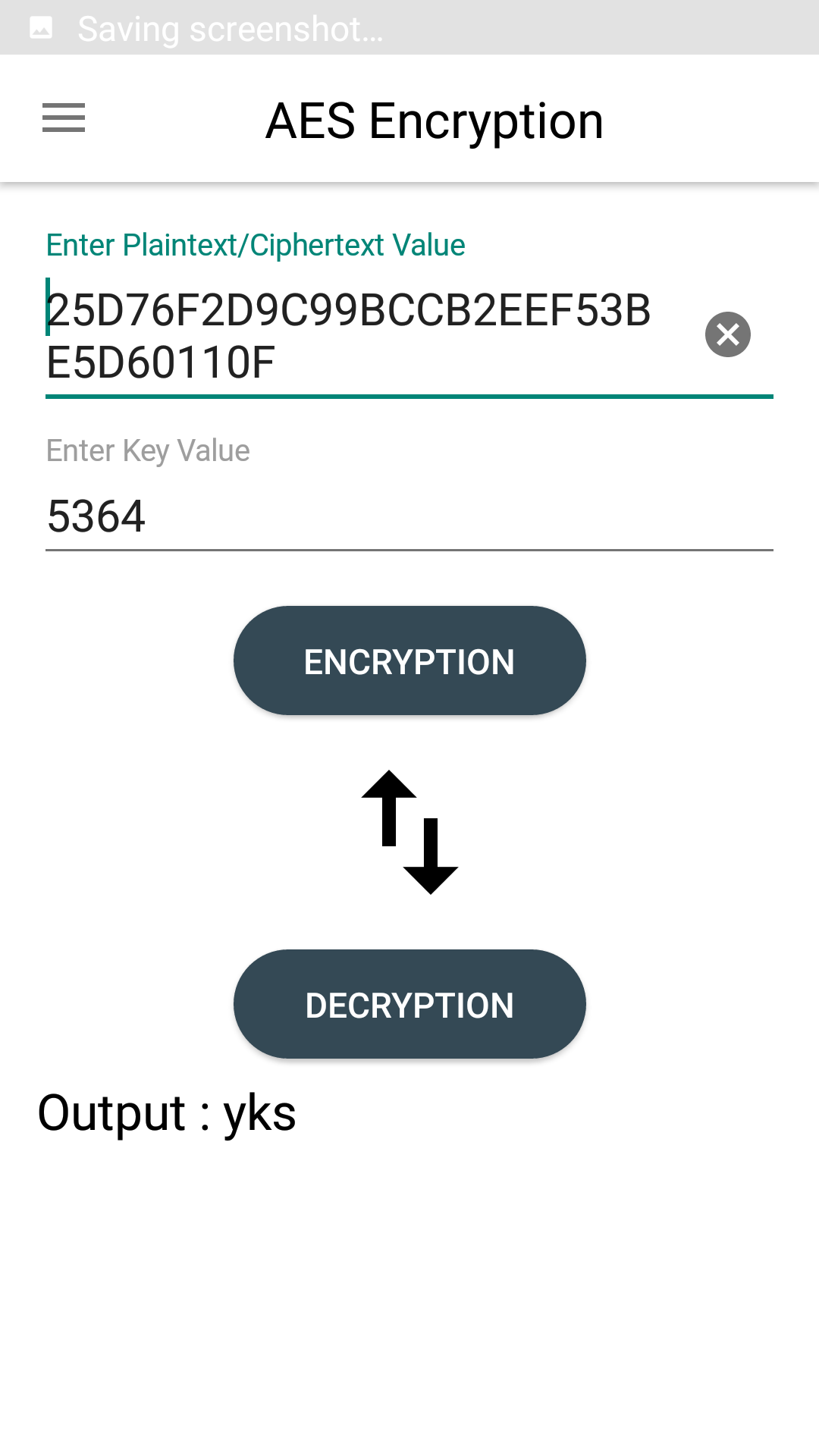
Github Ykstech Cryptography Cryptography The aim of this post is to provide a simple, ready for use latex article template for writing research papers on cryptography. this is the setup i generally use in my papers, and i figured it could be useful, e.g. for phd student in crypto. I made a \ (\latex\) template for cryptologic research papers at github rickfreemancui crypto latex template. it features: cryptobib as a submodule, which means that your can access the latest cryptobib in your project by running the git pull commands. The emphasis of the course will be on general principles, but, for concreteness, we shall also look at a number of examples and applications. I also have a paper template available online in the hope this reduces the start up time of writing a new paper. finally, please consider publishing the latex source code of your paper, so we can all focus on research instead of typesetting. Of all the cryptographic "best practices", this is the one you're least likely to get right on your own. nacl has been designed to prevent you from making stupid mistakes, it's highly favored among the cryptographic community, and focuses on modern, highly secure cryptographic primitives. Cybrary cryptography this online course we will cover how cryptography is the cornerstone of security, and how through its use of different encryption methods, such as ciphers, and public or private keys, you can protect private or sensitive information from unauthorized access.

Github Ykstech Cryptography Cryptography The emphasis of the course will be on general principles, but, for concreteness, we shall also look at a number of examples and applications. I also have a paper template available online in the hope this reduces the start up time of writing a new paper. finally, please consider publishing the latex source code of your paper, so we can all focus on research instead of typesetting. Of all the cryptographic "best practices", this is the one you're least likely to get right on your own. nacl has been designed to prevent you from making stupid mistakes, it's highly favored among the cryptographic community, and focuses on modern, highly secure cryptographic primitives. Cybrary cryptography this online course we will cover how cryptography is the cornerstone of security, and how through its use of different encryption methods, such as ciphers, and public or private keys, you can protect private or sensitive information from unauthorized access.
Github Anshulkamath Cryptography A Minimal Dependency Cryptography Of all the cryptographic "best practices", this is the one you're least likely to get right on your own. nacl has been designed to prevent you from making stupid mistakes, it's highly favored among the cryptographic community, and focuses on modern, highly secure cryptographic primitives. Cybrary cryptography this online course we will cover how cryptography is the cornerstone of security, and how through its use of different encryption methods, such as ciphers, and public or private keys, you can protect private or sensitive information from unauthorized access.