Encryption Vs Decryption A Comprehensive Comparison Learn about encryption and decryption algorithms, key sizes, security, and history. use the universal encrypt decrypt tool to encrypt or decrypt any string with one click. In cybersecurity, encryption and decryption are essential procedures. while decryption enables the intended recipient to view the original data, encryption safeguards data by rendering it unreadable to unauthorized parties.
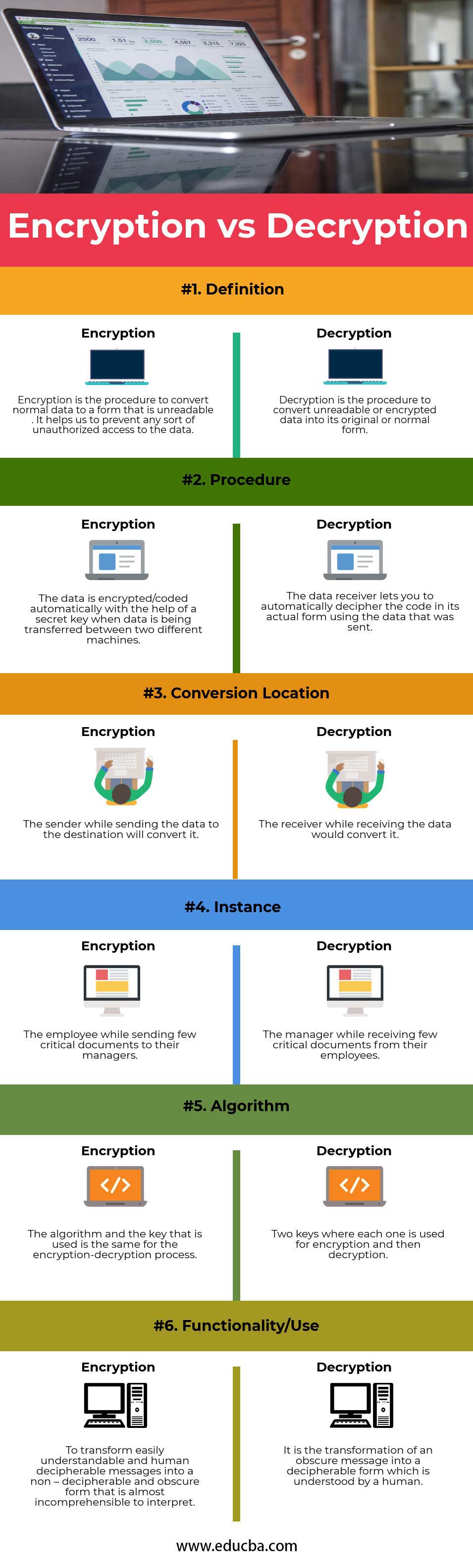
Symmetric Encryption Decryption Stable Diffusion Online Encryption and decryption work together to protect digital data, providing secure communication and safeguarding sensitive information. while encryption jumbles data into an unreadable format, decryption restores it for authorised access. This guide explains encryption & decryption in plain english, with real world examples & tips. secure your messages, files, & privacy. ️ learn everything you need to know, today!. Decryption is the method of converting unreadable or encoded data into its original form. encryption is done by the person who is sending the data to the destination, but decryption is done by the person who is receiving the data. the same algorithm with the same key is used for both the encryption and decryption processes. Encryption and decryption are fundamental processes in cybersecurity and data privacy, ensuring that information remains secure from unauthorized access. here’s a detailed explanation of both.
Free Text Encryption And Decryption Tool Easy To Use Decryption is the method of converting unreadable or encoded data into its original form. encryption is done by the person who is sending the data to the destination, but decryption is done by the person who is receiving the data. the same algorithm with the same key is used for both the encryption and decryption processes. Encryption and decryption are fundamental processes in cybersecurity and data privacy, ensuring that information remains secure from unauthorized access. here’s a detailed explanation of both. Whether you're a developer working on secure applications or simply looking to enhance your understanding of how cryptography works, this article will dive deep into the vital processes of encryption and decryption. Two primary approaches, symmetric and asymmetric cryptography, form the building blocks of modern encryption and decryption methods. each approach comes with its own advantages, drawbacks, and practical considerations, often determined by how keys are generated, managed, and shared. Looking at encryption vs decryption, they might sound similar, but they come with pretty different focus areas. the short version is that encryption makes sure that only authorized users can read the data. whereas with decryption, you’re getting a restoration of data to its original and usable form. Learn how encryption and decryption work, why they are important, and what types of algorithms and applications they use. compare and contrast the key differences between symmetric and asymmetric encryption and decryption.