
E Commerce Security Download Free Pdf Security Computer Security This document discusses the dimensions of e commerce security including integrity, nonrepudiation, authenticity, confidentiality, privacy, and availability. it outlines security threats like malicious code, hacking, credit card fraud, spoofing, and denial of service attacks. E commerce security free download as powerpoint presentation (.ppt .pptx), pdf file (.pdf), text file (.txt) or view presentation slides online. this document discusses e commerce security.

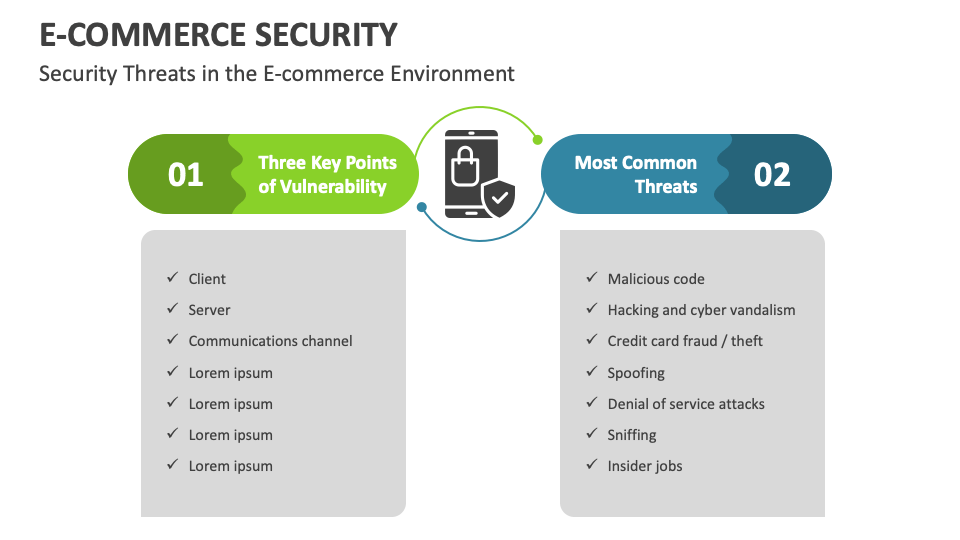
E Commerce Ppt Pptx E Commerce Ppt Pptxx Ppt Electronic commerce, seventh annual edition. The document examines security protocols like ssl that provide encryption, authentication, and integrity. it explores tensions between security and other values. This is an editable powerpoint three stages graphic that deals with topics like e commerce cyber security threats to help convey your message better graphically. Considering each logical link in the commerce chain, the assets that must be protected to ensure secure e commerce include client computers, the messages travelling on the communication channel, and the web and commerce servers – including any hardware attached to the servers.

E Commerce Security Group7 Pptx This is an editable powerpoint three stages graphic that deals with topics like e commerce cyber security threats to help convey your message better graphically. Considering each logical link in the commerce chain, the assets that must be protected to ensure secure e commerce include client computers, the messages travelling on the communication channel, and the web and commerce servers – including any hardware attached to the servers. Albert levi, e commerce security and pkis. ansi x9.59 basic characteristics • x9.59 does not offer encrypted communication. • challenging? here is the justification: • x9.59 uses x9.59 specific prc (payment routing code) instead of account card numbers. Enhance your understanding of e commerce security with our fully editable and customizable powerpoint presentations. explore essential strategies to protect online transactions and safeguard customer data effectively. Use secure transmissions http 1.1 uses digest authentication process use encrypted communications e.g. ssl connection client based certificate system certificates when user logs on (presents their certificate) the authentication server verifies the certificate is valid by opening it with the ca’s public key certificate contains users public key and personal information. This document discusses security issues related to e commerce. it begins by outlining some key threats to e commerce security, including human error, espionage trespassing, and technical vulnerabilities.
E Commerce Security Template For Powerpoint And Google Slides Ppt Slides Albert levi, e commerce security and pkis. ansi x9.59 basic characteristics • x9.59 does not offer encrypted communication. • challenging? here is the justification: • x9.59 uses x9.59 specific prc (payment routing code) instead of account card numbers. Enhance your understanding of e commerce security with our fully editable and customizable powerpoint presentations. explore essential strategies to protect online transactions and safeguard customer data effectively. Use secure transmissions http 1.1 uses digest authentication process use encrypted communications e.g. ssl connection client based certificate system certificates when user logs on (presents their certificate) the authentication server verifies the certificate is valid by opening it with the ca’s public key certificate contains users public key and personal information. This document discusses security issues related to e commerce. it begins by outlining some key threats to e commerce security, including human error, espionage trespassing, and technical vulnerabilities.
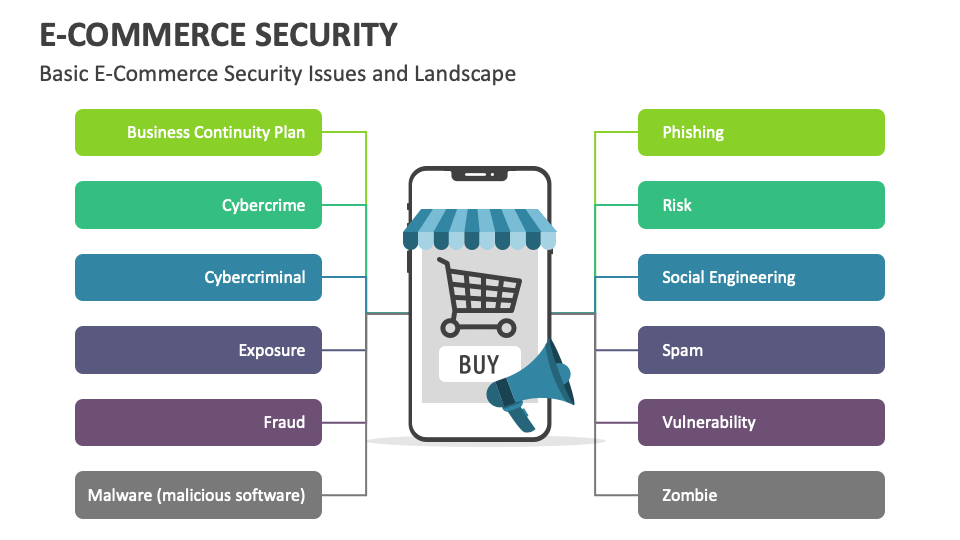
E Commerce Security Template For Powerpoint And Google Slides Ppt Slides Use secure transmissions http 1.1 uses digest authentication process use encrypted communications e.g. ssl connection client based certificate system certificates when user logs on (presents their certificate) the authentication server verifies the certificate is valid by opening it with the ca’s public key certificate contains users public key and personal information. This document discusses security issues related to e commerce. it begins by outlining some key threats to e commerce security, including human error, espionage trespassing, and technical vulnerabilities.