
Diffie Hellman Key Pdf Key Cryptography Public Key Cryptography How does the diffie hellman key exchange work? the diffie hellman algorithm takes two systems parameters referred to as variables “p” and “g.” each of the parameters are in the public and can be seen or used by all users in the given system. The diffie–hellman key exchange method allows two parties that have no prior knowledge of each other to jointly establish a shared secret key over an insecure channel.

89 Diffie Hellman Dh Pdf Key Cryptography Communications Diffie hellman (dh) groups are the key exchange strength setting used in ike (phase 1) and optionally for pfs in esp (phase 2). both peers must have at least one matching group. diffie hellman groups define the cryptographic strength used during key exchange. larger group numbers offer higher security but may increase cpu load. Keys for end to end encrypted calls are generated using the diffie hellman key exchange. users who are on a call can ensure that there is no mitm by comparing key visualizations. This article cuts through the complexity to explain the core mechanics, mathematical foundations, and real world applications of diffie hellman, while also exploring how emerging quantum technologies could disrupt its security. Introduction to diffie hellman key exchange protocol. the article explains the what, why and how of dhke. it also includes information about attacks on diffie hellman key exchange and briefly describes the real life implementations of this protocol.
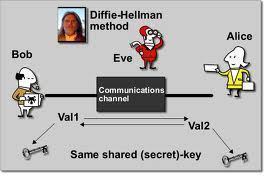
Diffie Hellman Tech Faq This article cuts through the complexity to explain the core mechanics, mathematical foundations, and real world applications of diffie hellman, while also exploring how emerging quantum technologies could disrupt its security. Introduction to diffie hellman key exchange protocol. the article explains the what, why and how of dhke. it also includes information about attacks on diffie hellman key exchange and briefly describes the real life implementations of this protocol. Diffie hellman algorithm: the diffie hellman algorithm is being used to establish a shared secret that can be used for secret communications while exchanging data over a public network using the elliptic curve to generate points and get the secret key using the parameters. In this article, i’ll explain how the key exchange works, why it’s essential for secure communication, and how it protects you in everyday online activities. the diffie hellman key exchange lets two parties create a shared secret key, even if someone else is listening in. The diffie hellman key exchange, introduced in 1976 by whitfield diffie and martin hellman, revolutionized the field of cryptography by providing a method for secure key exchange over an insecure communication channel. The diffie hellman key exchange was one of the most important developments in public key cryptography. find out why it's still such an important aspect of internet security.

Diffie Hellman Obsidian Publish Diffie hellman algorithm: the diffie hellman algorithm is being used to establish a shared secret that can be used for secret communications while exchanging data over a public network using the elliptic curve to generate points and get the secret key using the parameters. In this article, i’ll explain how the key exchange works, why it’s essential for secure communication, and how it protects you in everyday online activities. the diffie hellman key exchange lets two parties create a shared secret key, even if someone else is listening in. The diffie hellman key exchange, introduced in 1976 by whitfield diffie and martin hellman, revolutionized the field of cryptography by providing a method for secure key exchange over an insecure communication channel. The diffie hellman key exchange was one of the most important developments in public key cryptography. find out why it's still such an important aspect of internet security.