Ppt Diffie Hellman Algorithm Powerpoint Presentation Free Download The diffie hellman algorithm, developed in 1976 by whitfield diffie and martin hellman, enables two parties to generate a shared cryptographic key for secure communication over an insecure channel without transferring the key itself. Diffie hellman key exchange explained the diffie hellman key exchange algorithm allows two users to securely exchange a key over an insecure channel by using public key cryptography.
Ppt The Diffie Hellman Algorithm Powerpoint Presentation Free After completing this topic, a student will be able to describe the diffie hellman algorithm. diffie hellman algorithm figures and material in this topic have been adapted from. Learn about the diffie hellman key exchange algorithm for secure key agreement between parties. understand the process, mathematical theory, an example, and the algorithm's vulnerability to man in the middle attacks. In practice the shared encryption key relies on such complex concepts as modular exponentiation, primitive roots and discrete logarithm problems. let’s see though is we can explain the diffie hellman algorithm with no complex mathematics. The document presents an overview of the diffie hellman key exchange method, detailing its origins, workings, advantages, and vulnerabilities such as the risk of man in the middle attacks.
Ppt The Diffie Hellman Algorithm Powerpoint Presentation Free In practice the shared encryption key relies on such complex concepts as modular exponentiation, primitive roots and discrete logarithm problems. let’s see though is we can explain the diffie hellman algorithm with no complex mathematics. The document presents an overview of the diffie hellman key exchange method, detailing its origins, workings, advantages, and vulnerabilities such as the risk of man in the middle attacks. The document explains the diffie hellman key exchange, a foundational method for securely sharing cryptographic keys over a public channel, introduced by whitfield diffie and martin hellman in 1976. The diffie hellman key exchange algorithm allows two users to securely exchange a key over an insecure channel by using discrete logarithm problems. it works by having both users choose a private value and calculating a public value using a prime number and primitive root that are publicly known. Presentation transcript the diffie hellman algorithm overview • introduction • implementation • example • applications • conclusion. The diffie hellman algorithm, proposed by whitfield diffie and martin hellman in 1976, enables two parties to securely agree on a secret key over an insecure channel, addressing key exchange challenges in cybersecurity.
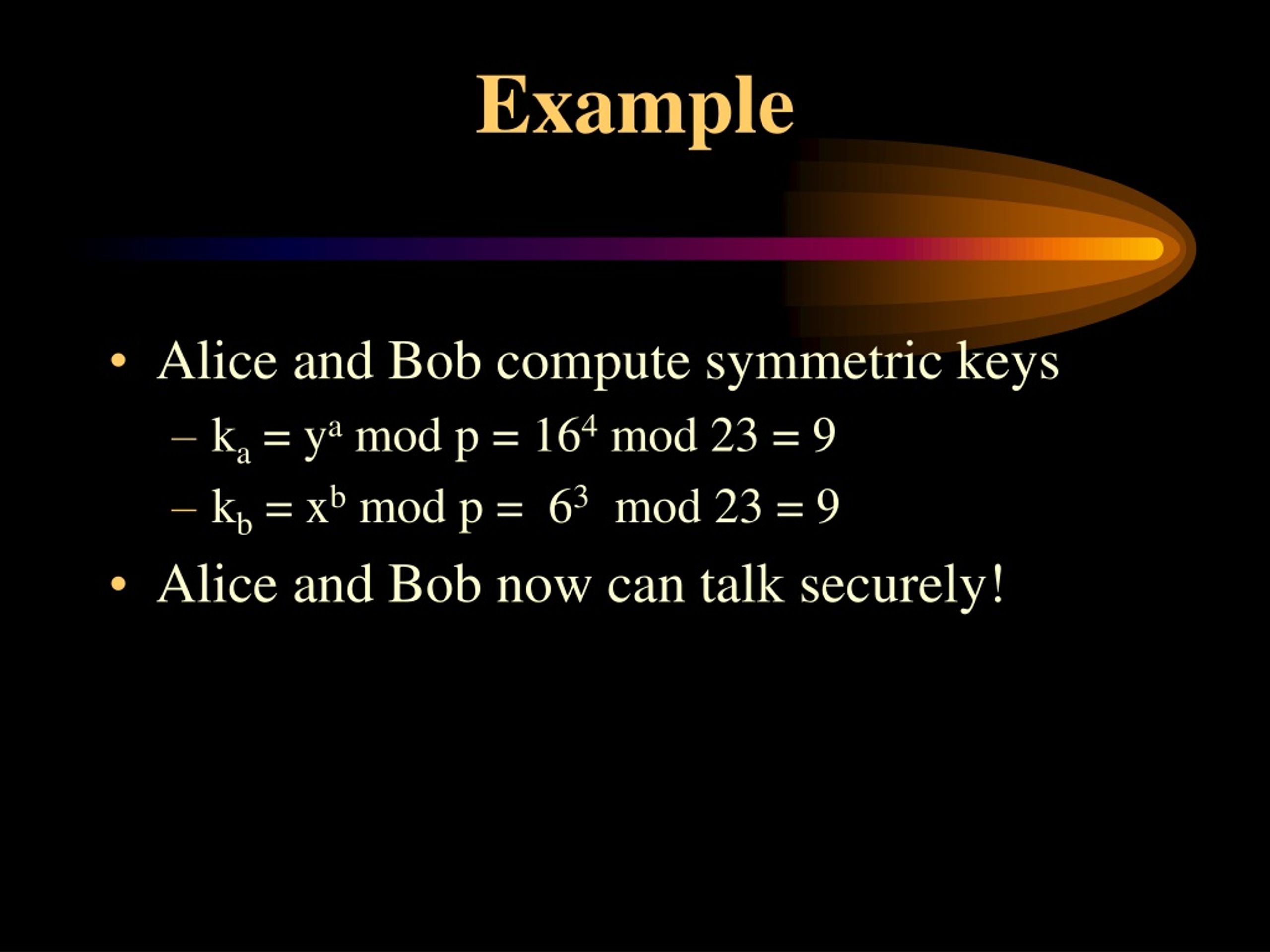
Ppt The Diffie Hellman Algorithm Powerpoint Presentation Free The document explains the diffie hellman key exchange, a foundational method for securely sharing cryptographic keys over a public channel, introduced by whitfield diffie and martin hellman in 1976. The diffie hellman key exchange algorithm allows two users to securely exchange a key over an insecure channel by using discrete logarithm problems. it works by having both users choose a private value and calculating a public value using a prime number and primitive root that are publicly known. Presentation transcript the diffie hellman algorithm overview • introduction • implementation • example • applications • conclusion. The diffie hellman algorithm, proposed by whitfield diffie and martin hellman in 1976, enables two parties to securely agree on a secret key over an insecure channel, addressing key exchange challenges in cybersecurity.