
Cryptography With Python Tutorial Pdf Cipher Cryptography Cryptography with python tutorial free download as pdf file (.pdf), text file (.txt) or read online for free. cryptography with python tutorial. You can download the pdf of this wonderful tutorial by paying a nominal price of $9.99. your contribution will go a long way in helping us serve more readers.
Cryptography 1 Pdf Cipher Cryptography Some useful books related to cybersecurity, linux and more. cybersec books practical cryptography in python.pdf at main · 0x00ctrl cybersec books. By offering a blend of theoretical knowledge and practical exercises, this ebook aims to equip its readers with a comprehensive understanding of how to utilize python for cryptography. Cryptography has a long and important history in protecting critical systems and sensitive information. this book will show you how to encrypt, evaluate, compare, and attack data using python. Prerequisites throughout this tutorial, you will learn the basics of cryptography, algorithm description and its implementation in python. this tutorial is designed with an assumption that the user has an understanding on the basics of cryptography and algorithms.

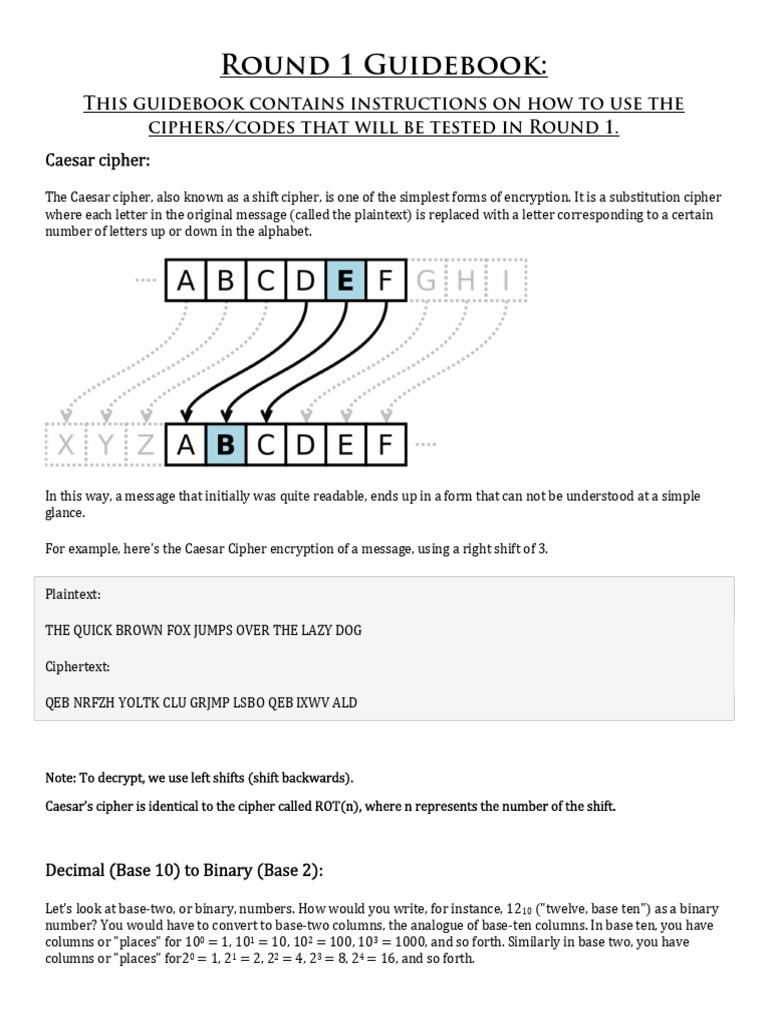
Cryptography Cipher Pdf Cryptography has a long and important history in protecting critical systems and sensitive information. this book will show you how to encrypt, evaluate, compare, and attack data using python. Prerequisites throughout this tutorial, you will learn the basics of cryptography, algorithm description and its implementation in python. this tutorial is designed with an assumption that the user has an understanding on the basics of cryptography and algorithms. Understand the basic concepts of cryptography, its goals, terminology, and how cryptographic systems work. this section explains the fundamentals of securing information and the basic components of cryptographic systems. Key: the piece of information that allows you to either encrypt or decrypt your data. plaintext: the information that you want to keep hidden, in its unencrypted form. the plaintext can be any data at all: a picture, a spreadsheet, or even a whole hard disk. Convention: alicekazam is sending encrypted messages to bobasaur, bobasaur is decrypting them, and eevee is an eavesdropper who overhears everything being sent, but hopefully still can’t understand it. an encryption method together with a decryption method is known as a cryptographic scheme. The chapter discusses variables, operators, strings, loops, and files used in python. it also shows how to write a cipher code that took plaintext and returned the ciphertext.

Python Security Cryptography Pdf Cryptography Key Cryptography Understand the basic concepts of cryptography, its goals, terminology, and how cryptographic systems work. this section explains the fundamentals of securing information and the basic components of cryptographic systems. Key: the piece of information that allows you to either encrypt or decrypt your data. plaintext: the information that you want to keep hidden, in its unencrypted form. the plaintext can be any data at all: a picture, a spreadsheet, or even a whole hard disk. Convention: alicekazam is sending encrypted messages to bobasaur, bobasaur is decrypting them, and eevee is an eavesdropper who overhears everything being sent, but hopefully still can’t understand it. an encryption method together with a decryption method is known as a cryptographic scheme. The chapter discusses variables, operators, strings, loops, and files used in python. it also shows how to write a cipher code that took plaintext and returned the ciphertext.
Lecture 2 Cryptography Pdf Cryptography Key Cryptography Convention: alicekazam is sending encrypted messages to bobasaur, bobasaur is decrypting them, and eevee is an eavesdropper who overhears everything being sent, but hopefully still can’t understand it. an encryption method together with a decryption method is known as a cryptographic scheme. The chapter discusses variables, operators, strings, loops, and files used in python. it also shows how to write a cipher code that took plaintext and returned the ciphertext.
Github Ajmain Khan Python Cryptography Ciphers Implementation Of