
Cryptographic Hash Functions And Their Applications An Exploration Of Cryptographic hash functions are intended to be fast, deterministic, and one way, meaning that even a minor change in input yields a very different hash. these functions are important for securing information digitally by allowing data verification and authentication. Learn about cryptographic hash functions, their algorithms (sha 256, md5), digital signatures, macs, and practical security applications.

M 3 Cryptographic Hash Functions Pdf Public Key Cryptography Learn how cryptographic hash functions work, from md5 to sha 256 and sha 512. covers the avalanche effect, collision attacks, password hashing with bcrypt argon2, hmac authentication, and real world applications in blockchain, tls, and git. Cryptographic hash functions have many information security applications, notably in digital signatures, message authentication codes (macs), and other forms of authentication. The essence of the use of a hash function for message integrity is as follows. the sender computes a hash value as a function of the bits in the message and transmits both the hash value and the message. Despite their critical importance, many developers use hash functions without fully understanding their properties, limitations, and appropriate applications. this comprehensive guide explores the world of cryptographic hashing, from basic concepts to advanced security considerations.

Cryptographic Hash Function Wikipedia Pdf Cryptography Password The essence of the use of a hash function for message integrity is as follows. the sender computes a hash value as a function of the bits in the message and transmits both the hash value and the message. Despite their critical importance, many developers use hash functions without fully understanding their properties, limitations, and appropriate applications. this comprehensive guide explores the world of cryptographic hashing, from basic concepts to advanced security considerations. We'll look at how they're used in real world applications and explore their strengths and weaknesses. understanding hash functions is key to grasping modern cryptography. In this note we discuss the extent to which the hash functions can be thought of as black boxes, review some recent attacks, and, most importantly, revisit common applications of hash functions in programming practice. the note assumes no previous background in cryptography. Hash functions hash functions: applications cryptographic hash functions (like sha 256 and sha3 256) are used in many scenarios. let's review their most common applications. Cryptographic hash functions are an essential component for ensuring data integrity and privacy in digital information systems and find widespread application in many contexts.
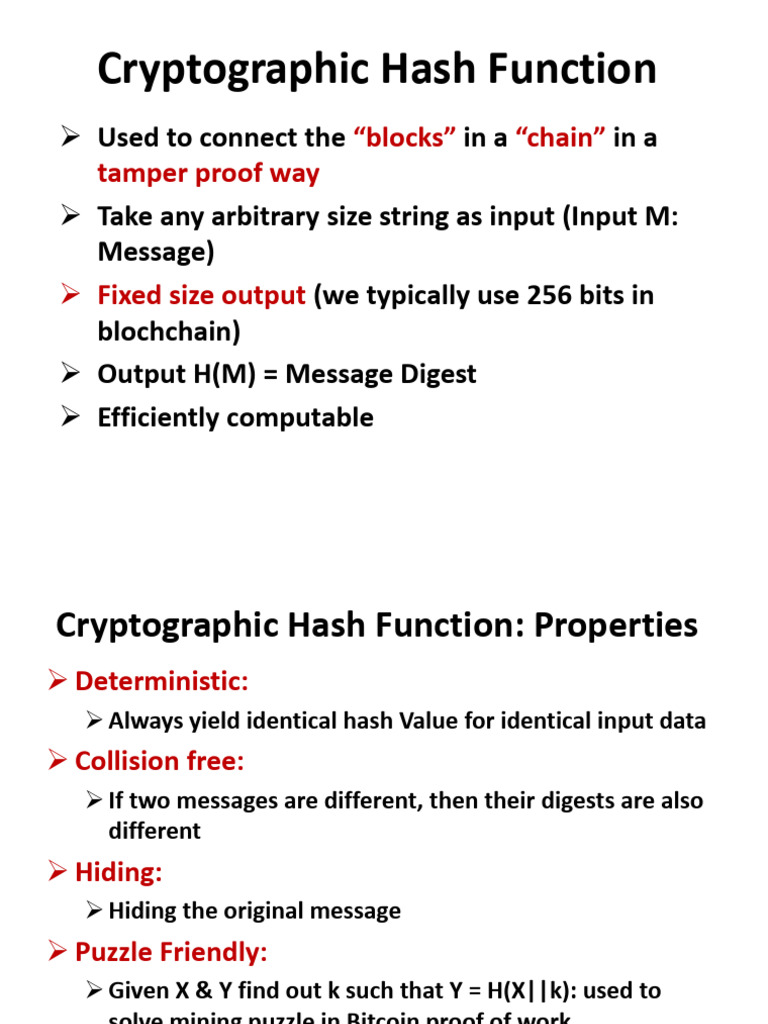
Cryptographic Hash Function And Its Properties Pdf Cryptography We'll look at how they're used in real world applications and explore their strengths and weaknesses. understanding hash functions is key to grasping modern cryptography. In this note we discuss the extent to which the hash functions can be thought of as black boxes, review some recent attacks, and, most importantly, revisit common applications of hash functions in programming practice. the note assumes no previous background in cryptography. Hash functions hash functions: applications cryptographic hash functions (like sha 256 and sha3 256) are used in many scenarios. let's review their most common applications. Cryptographic hash functions are an essential component for ensuring data integrity and privacy in digital information systems and find widespread application in many contexts.
Ppt Cryptographic Hash Functions And Their Many Applications Hash functions hash functions: applications cryptographic hash functions (like sha 256 and sha3 256) are used in many scenarios. let's review their most common applications. Cryptographic hash functions are an essential component for ensuring data integrity and privacy in digital information systems and find widespread application in many contexts.
Cryptographic Hash Functions Namastedev Blogs