Cryptanalysis Notes Pdf Public Key Cryptography Cryptanalysis Their research helps cryptographers strengthen algorithms. cryptanalysts uncover design flaws that can reduce the number of keys tested on a message. their work is used by governments and companies to test security products. download as a pptx, pdf or view online for free. Study of cryptanalysis gives insight into all aspects of crypto also gain insight into attacker’s mindset “black hat” vs “white hat” mentality cryptanalysis is more fun than cryptography cryptographers are boring cryptanalysts are cool but cryptanalysis is hard trudy is the bad guy trudy is our generic “intruder” plaintext key key.

1 Cryptanalysis For Graduate Course Pptx At the end of this course, you will. understand foundational mathematics that drive crypto designs and attacks, including topics in number theory, abstract algebra, linear algebra, and probability. be able to identify appropriate methods of analysis based on algorithm class and properties. Contribute to kmanimala ics ppts development by creating an account on github. Cryptanalysis • four kinds of attacks (recall) • the objective: determine the key (herckhoff principle) • assumption: english plaintext text • basic techniques: frequency analysis based on: • probabilities of occurrences of 26 letters • common digrams and trigrams. The last two (chosen ciphertext and chosen text) are less commonly employed as cryptanalytic techniques but are nevertheless possible avenues of attack. cryptanalysis only a relatively weak algorithm will fail to withstand a ciphertext only attack. generally, an encryption algorithm is designed to withstand a known plaintext attack. cryptanalysis.
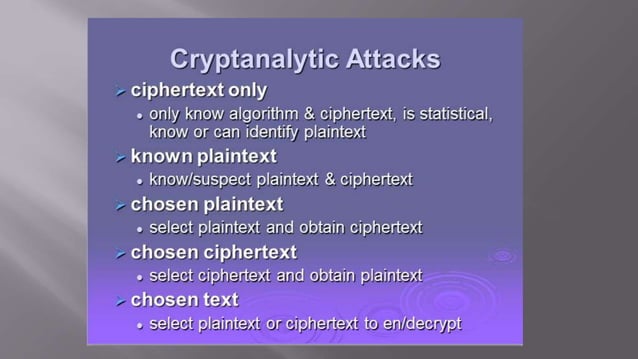
Cryptanalysis 101 Pptx Cryptanalysis • four kinds of attacks (recall) • the objective: determine the key (herckhoff principle) • assumption: english plaintext text • basic techniques: frequency analysis based on: • probabilities of occurrences of 26 letters • common digrams and trigrams. The last two (chosen ciphertext and chosen text) are less commonly employed as cryptanalytic techniques but are nevertheless possible avenues of attack. cryptanalysis only a relatively weak algorithm will fail to withstand a ciphertext only attack. generally, an encryption algorithm is designed to withstand a known plaintext attack. cryptanalysis. The paper introduces the field of cryptanalysis, emphasizing linear cryptanalysis techniques developed by matsui and others. it discusses key elements such as the concept of linear hulls and their implications for cryptographic security, particularly concerning the aes and other symmetric key ciphers. Three important characteristics of this problem enabled us to use a brute force cryptanalysis: 1. the encryption and decryption algorithms are known. 2. there are only 25 keys to try. 3. the language of the plaintext is known and easily recognizable. brute force search (ceaser cipher). Explore the fundamentals of cryptanalysis with our comprehensive powerpoint presentation on cryptanalysis techniques. this deck covers essential cryptosystems, analytical methods, and real world applications, providing valuable insights for professionals and enthusiasts alike. View cryptanalysis ppts online, safely and virus free! many are downloadable. learn new and interesting things. get ideas for your own presentations. share yours for free!.