
Buffer Overflow Attacks Explained Here, we will examine the history of buffer overflows as a security vulnerability, explain how a buffer overflow attacks work and are executed, and replicate a buffer overflow attack in c. Buffer overflow attacks against programs running on remote systems allow attackers to execute code of their choosing on a computer in which they have no access rights.
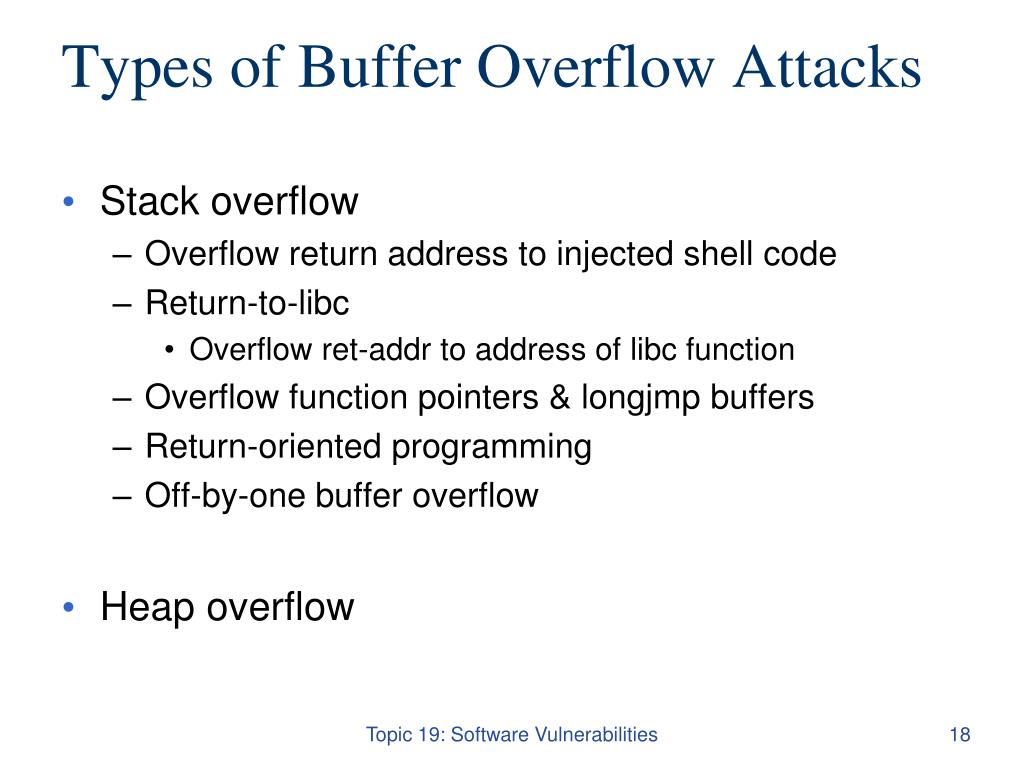
Ppt System Programming Topic 19 Powerpoint Presentation Free Buffer overflow is a software coding error that enables hackers to exploit vulnerabilities, steal data, and gain unauthorized access to corporate systems. discover what is a buffer overflow attack and how fortinet can mitigate and prevent overflow attacks. Understand buffer overflows, types of attacks and prevention strategies, and learn how to mitigate vulnerabilities with secure programming practices. Despite technological advancements and security practices, buffer overflow attacks pose significant threats to software systems worldwide. this article delves into the intricacies of buffer overflow, exploring its mechanisms, exploitation techniques, and mitigation strategies. What are the different types of buffer overflow attacks? there are a number of different buffer overflow attacks which employ different strategies and target different pieces of code. below are a few of the most well known.
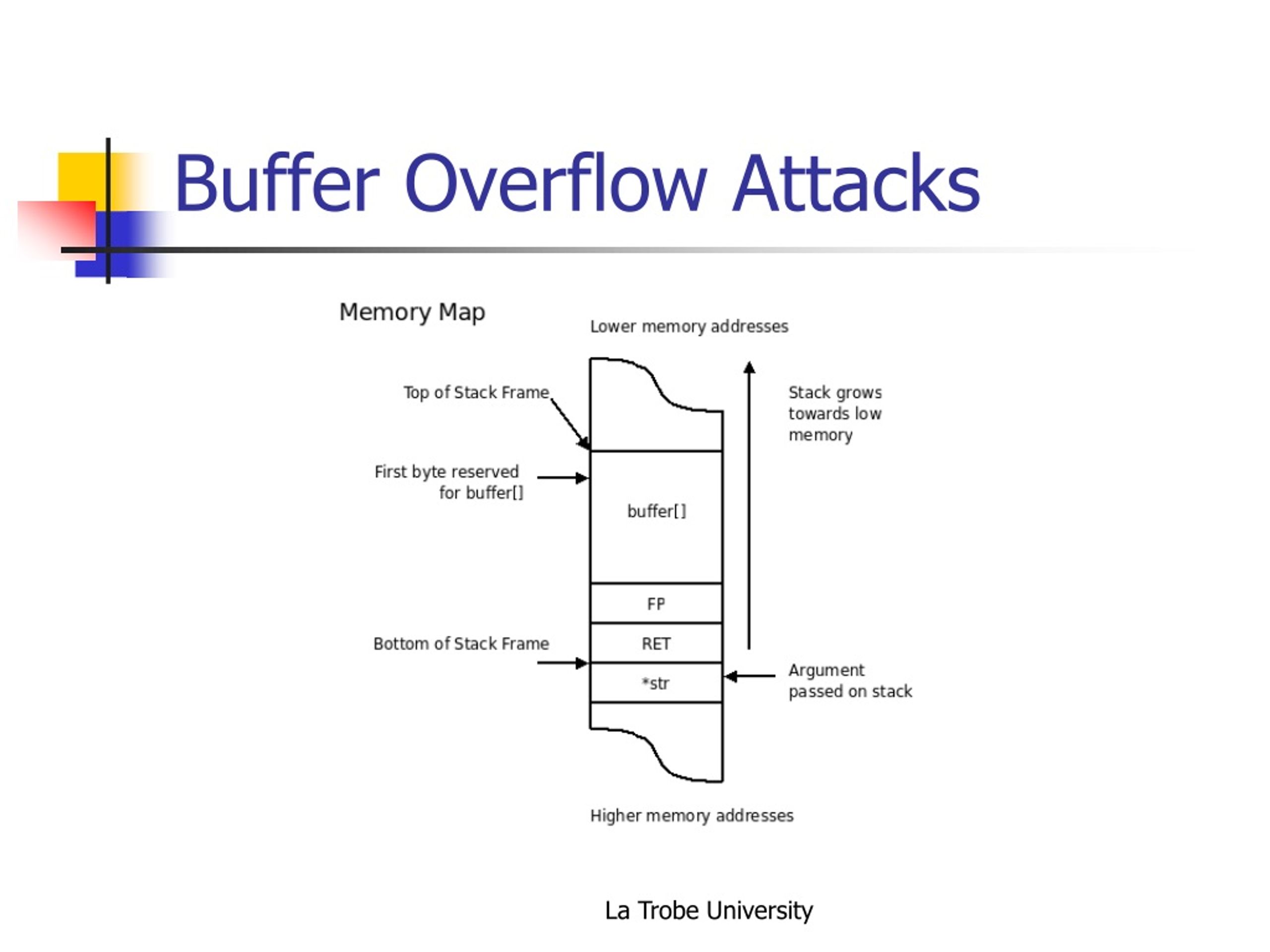
Ppt Operating System Security Ii Powerpoint Presentation Free Despite technological advancements and security practices, buffer overflow attacks pose significant threats to software systems worldwide. this article delves into the intricacies of buffer overflow, exploring its mechanisms, exploitation techniques, and mitigation strategies. What are the different types of buffer overflow attacks? there are a number of different buffer overflow attacks which employ different strategies and target different pieces of code. below are a few of the most well known. Buffer overflow is probably the best known form of software security vulnerability. most software developers know what a buffer overflow vulnerability is, but buffer overflow attacks against both legacy and newly developed applications are still quite common. A buffer overflow (or buffer overrun) occurs when the volume of data exceeds the storage capacity of the memory buffer. as a result, the program attempting to write the data to the buffer overwrites adjacent memory locations. This research paper provides an in depth analysis of buffer overflow attacks, exploring their underlying principles, common exploitation techniques, and potential impacts on software and systems. Learn what buffer overflows are, how exploits work, and practical prevention techniques, with clear examples and mitigation steps for developers.