
Cryptographic Hash Function Wikipedia Pdf Cryptography Password An explanation of what a hash function is, why they're used in bitcoin, and the types of hash functions used in bitcoin. Sha 256 is a cryptographic hashing function that protects transaction records and makes them tamper proof (immutable). bitcoin uses sha 256 to secure every block in the blockchain and power its mining process.
Cryptographic Hash Function And Its Properties Pdf Cryptography Discover how hash functions secure blockchain transactions, ensure data integrity, and support cryptocurrency mining with algorithms like sha 256. Learn how sha 256 hash function creates unhackable transactions, powers bitcoin mining, and secures the bitcoin blockchain. Bitcoin utilizes the sha 256 (secure hash algorithm 256) hash function, which produces a 256 bit (32 byte) hash value. sha 256 is widely regarded for its security and collision resistance. hash functions play a crucial role in bitcoin's block header and transaction verification processes. Sha 256 (secure hash algorithm 256 bit) is a fundamental cryptographic function used for securing data, verifying integrity, and enabling secure authentication. as a core component of bitcoin, it.

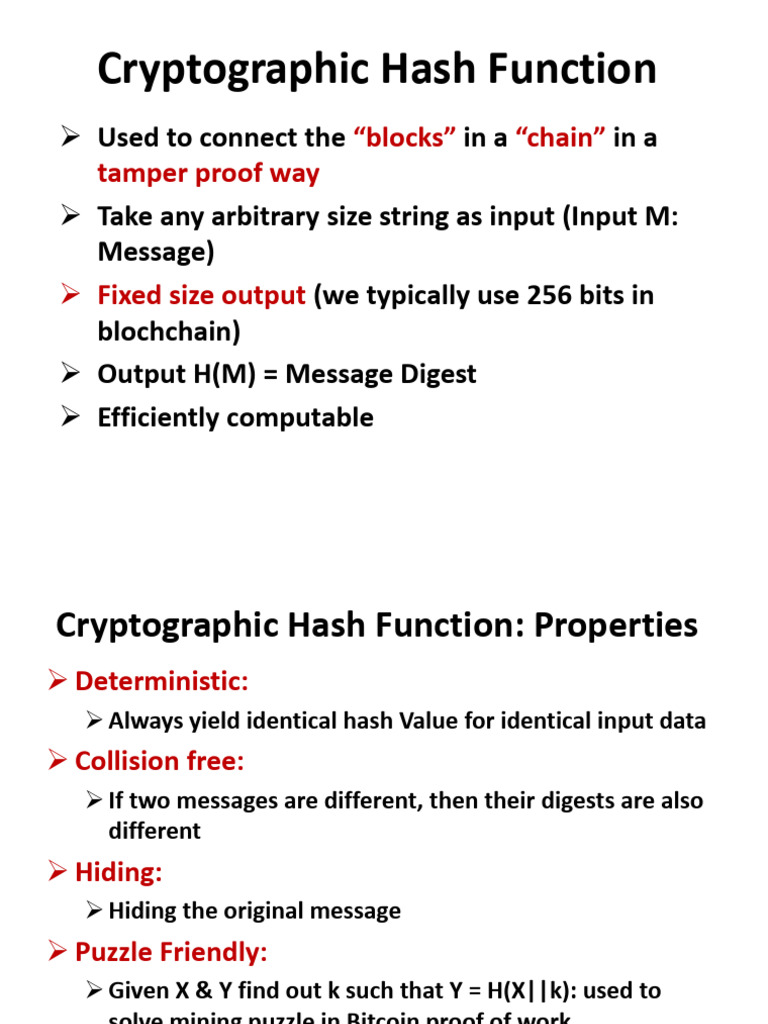
M 3 Cryptographic Hash Functions Pdf Public Key Cryptography Bitcoin utilizes the sha 256 (secure hash algorithm 256) hash function, which produces a 256 bit (32 byte) hash value. sha 256 is widely regarded for its security and collision resistance. hash functions play a crucial role in bitcoin's block header and transaction verification processes. Sha 256 (secure hash algorithm 256 bit) is a fundamental cryptographic function used for securing data, verifying integrity, and enabling secure authentication. as a core component of bitcoin, it. Cryptographic hash functions convert any data into a fixed size unique output that acts like a digital fingerprint for blockchain transactions. sha 256 powers bitcoin and most major blockchains, producing a 256 bit hash that would take billions of years to crack with current technology. A cryptographic hash function has to be computationally efficient but it is its deterministic nature, pre image resistance and collision resistance that constitute the three most important properties of hash functions in the bitcoin mining process learn more about these features here. Sha 256's role in bitcoin: sha 256 is a crucial cryptographic hash function used in bitcoin's proof of work (pow) consensus mechanism. it secures transactions by allowing miners to solve complex mathematical problems, ensuring the integrity of the network. Bitcoin and other cryptos depend on cryptographic hashing for mining, security, and trust. before we dive deeper into the technical details, let’s walk through the essential role hashes play in crypto and blockchain systems.

Cryptographic Foundations Of Bitcoin Understanding Primitives And Cryptographic hash functions convert any data into a fixed size unique output that acts like a digital fingerprint for blockchain transactions. sha 256 powers bitcoin and most major blockchains, producing a 256 bit hash that would take billions of years to crack with current technology. A cryptographic hash function has to be computationally efficient but it is its deterministic nature, pre image resistance and collision resistance that constitute the three most important properties of hash functions in the bitcoin mining process learn more about these features here. Sha 256's role in bitcoin: sha 256 is a crucial cryptographic hash function used in bitcoin's proof of work (pow) consensus mechanism. it secures transactions by allowing miners to solve complex mathematical problems, ensuring the integrity of the network. Bitcoin and other cryptos depend on cryptographic hashing for mining, security, and trust. before we dive deeper into the technical details, let’s walk through the essential role hashes play in crypto and blockchain systems.