Bicep Params Support For Key Vault Secrets Issue 10652 Azure Bicep This article explains how to use azure key vault to pass a secret as a parameter during bicep deployment. instead of entering a secure value like a password directly into your bicep file or parameters file, you can retrieve the value from azure key vault during a deployment. During the compilation time, getsecret() method serialize as a reference typed parameter syntax, so, compiler builder doesn't have to access to the keyvault and get the secret value.
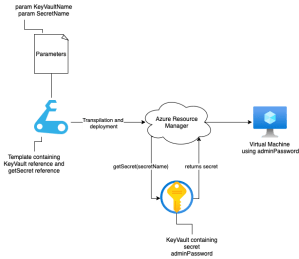
Reference Key Vault Secrets Using Azure Bicep Azure Cloud John Lokerse Use a key vault to manage your secrets, certificates, keys, and other data that needs to be protected and shared. you can use bicep to create and manage vaults and secrets. Learn how to manage secure parameters in bicep using parameter files and azure key vault references. includes best practices and examples. Fortunately, arm templates and azure bicep have built in support for using key vault secrets inside of the templates. in this post, we will discuss how to work with secure parameters and key vault secrets in azure bicep. “allow azure resource manager to retrieve secrets from this vault when it is evaluating and executing templates.” this is a vault level setting that permits arm to access secrets during deployment operations.
Reference Key Vault Secrets Using Azure Bicep John Lokerse Azure Fortunately, arm templates and azure bicep have built in support for using key vault secrets inside of the templates. in this post, we will discuss how to work with secure parameters and key vault secrets in azure bicep. “allow azure resource manager to retrieve secrets from this vault when it is evaluating and executing templates.” this is a vault level setting that permits arm to access secrets during deployment operations. @thomas sorry, i completely forgot to add the error. i added it now to the question. it simply says the parameter (the string that refers to the kv secret) is invalid. Incorporating azure key vault secrets into your bicep deployments can be achieved through either referencing a parameters file or utilizing the getsecret function. both methods provide secure, automated secret management, streamlining your deployment processes. We have seen how to deploy bicep resources that contain secure input parameters that are contained as secret values within an azure key vault. this has enabled us to keep our deployment secure using bicep template scripts. In this example, we have an existing key vault (kv production secure), which contains a stored secret (vmadminpassword). our goal is to retrieve this secret and pass it to an azure virtual machine as the admin password.