Github Renggadiansa Aes256 Encryption Aes 256 is considered to be quantum resistant, as it has similar quantum resistance to aes 128's resistance against traditional, non quantum, attacks at 128 bits of security. Aes 256 is a symmetric encryption algorithm that uses a 256 bit key to protect your data from hackers. learn how it works, what makes it special, and how it can help you prevent data breaches.
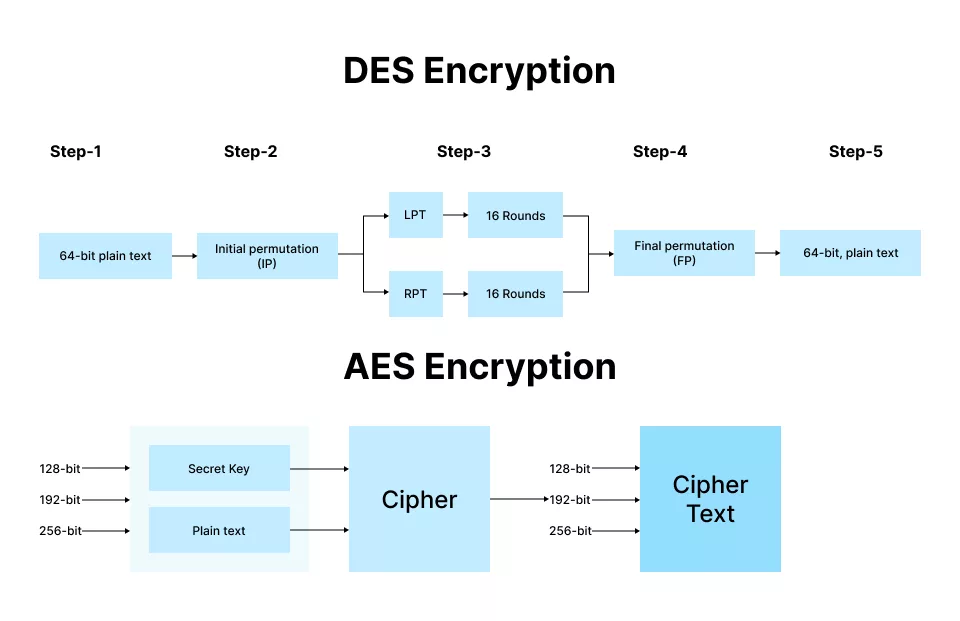
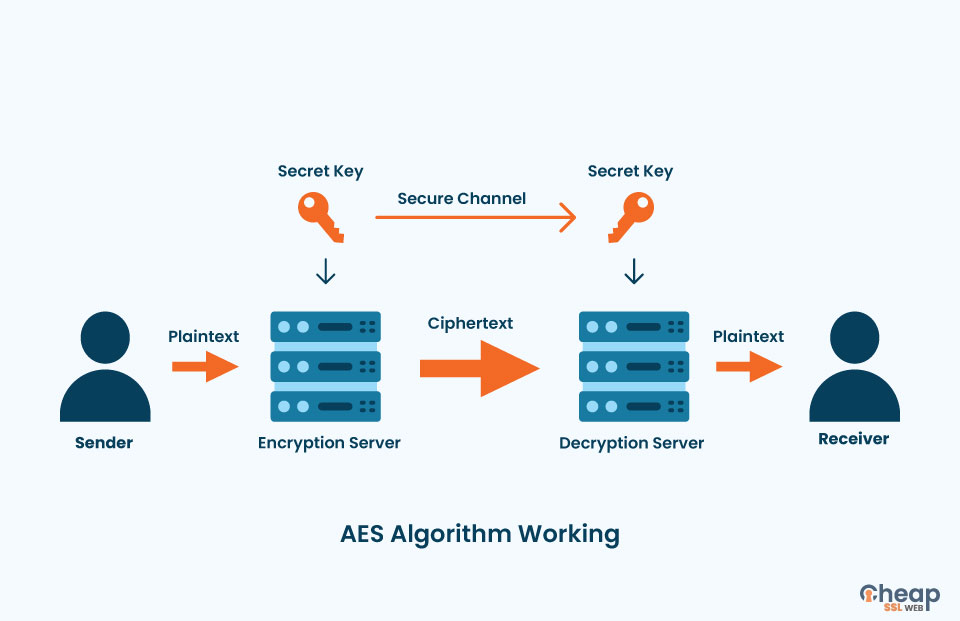
Rsa Aes Encryption Key Differences Explained 54 Off What is aes 256? aes 256 stands for advanced encryption standard with a 256 bit key size. it is a symmetric encryption algorithm, which means the same key is used for both encryption and. Aes encryption uses various key lengths (128, 192, or 256 bits) to provide strong protection against unauthorized access. this data security measure is efficient and widely implemented in securing internet communication, protecting sensitive data, and encrypting files. Three members of the rijndael family are specifed in this standard: aes 128, aes 192, and aes 256. each of them transforms data in blocks of 128 bits, and the numerical suffx indicates the bit length of the associated cryptographic keys. Learn the differences between aes 256 encryption modes like gcm, cbc, and ctr. discover real world use cases, common mistakes to avoid, and which mode offers the best security and performance.

Aes256 Encryption In C Three members of the rijndael family are specifed in this standard: aes 128, aes 192, and aes 256. each of them transforms data in blocks of 128 bits, and the numerical suffx indicates the bit length of the associated cryptographic keys. Learn the differences between aes 256 encryption modes like gcm, cbc, and ctr. discover real world use cases, common mistakes to avoid, and which mode offers the best security and performance. Learn how aes encryption works, why aes 256 is the enterprise standard, and how to implement it across databases, storage, and networks. A deep technical look at aes 256: its design, security properties, performance, and best practices for key management and real world usage. In this guide, we’ll dive into the fundamentals of aes encryption, explore its advantages, and discuss how splashtop integrates aes 256 encryption to ensure secure, reliable remote access for businesses and individuals. A deep dive into aes encryption modes — cbc, ecb, ctr, cfb, and ofb. understand how each works, their trade offs, and when to use them in real world projects.

Aes Algorithm Encryption Structure Download Scientific Diagram Learn how aes encryption works, why aes 256 is the enterprise standard, and how to implement it across databases, storage, and networks. A deep technical look at aes 256: its design, security properties, performance, and best practices for key management and real world usage. In this guide, we’ll dive into the fundamentals of aes encryption, explore its advantages, and discuss how splashtop integrates aes 256 encryption to ensure secure, reliable remote access for businesses and individuals. A deep dive into aes encryption modes — cbc, ecb, ctr, cfb, and ofb. understand how each works, their trade offs, and when to use them in real world projects.

Aes 256 Encryption Types Modes Best Practices Pitfalls Explained In this guide, we’ll dive into the fundamentals of aes encryption, explore its advantages, and discuss how splashtop integrates aes 256 encryption to ensure secure, reliable remote access for businesses and individuals. A deep dive into aes encryption modes — cbc, ecb, ctr, cfb, and ofb. understand how each works, their trade offs, and when to use them in real world projects.
Hardware Aes Encryption At Amy Leighton Blog