Aes Pdf Cryptography Espionage Techniques The aes algorithm is a symmetric block cipher that can encrypt (encipher) and decrypt (decipher) digital information. the aes algorithm is capable of using cryptographic keys of 128, 192, and 256 bits to encrypt and decrypt data in blocks of 128 bits. Abstract— advanced encryption standard (aes) algorithm is one on the most common and widely symmetric block cipher algorithm used in worldwide. this algorithm has an own particular.

Exploring The Advanced Encryption Standard Aes A Technical Overview Security emphasis was on security, resistance to cryptanalysis. nist explicitly demanded a 128 bit key to focus on resistance to cryptanalysis attacks other than brute force attack the criteria defined by nist for selecting aes fall into three areas:. To review the overall structure of aes and to focus particularly on the four steps used in each round of aes: (1) byte substitution, (2) shift rows, (3) mix columns, and (4) add round key. Number of advantages including hardware efficiency, software efficiency, provable security (in the sense that it is at least as secure as the other modes discussed) and simplicity. The main goal of this paper will provide a detail information about advanced encryption standard (aes) algorithm for encryption and decryption data then make a comparison between aes and des algorithm to point out some idea why replacing des to aes algorithm.
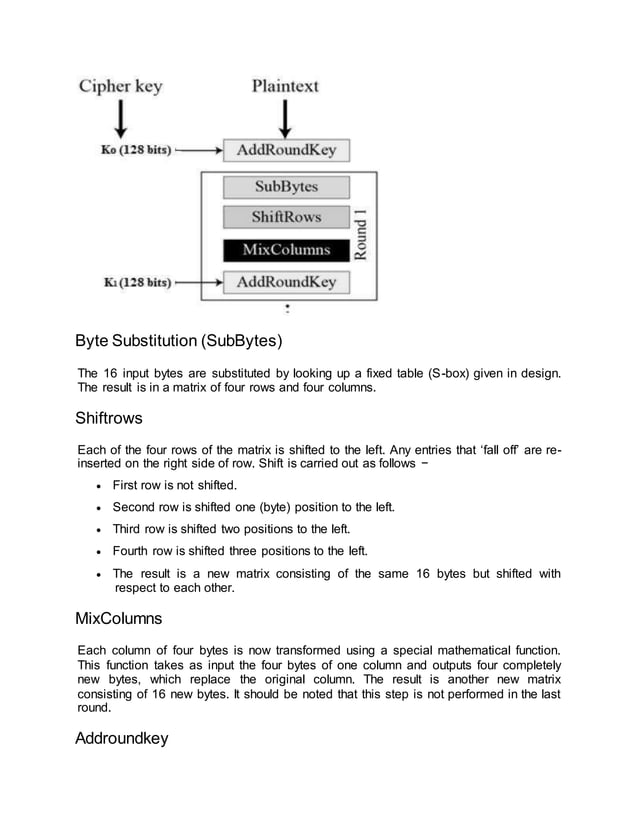
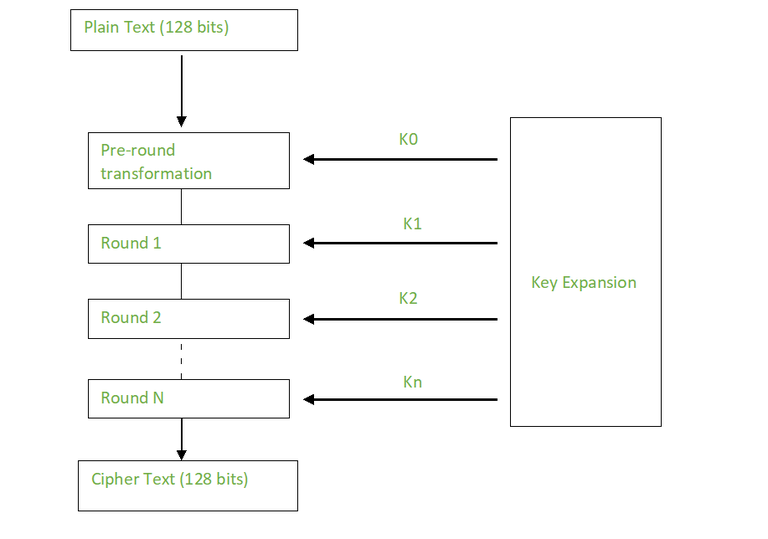
Benefits Of Adopting Aes Encryption For Quantum Security Mmetric, or two key, encryption. public key algorithm is based on mathematical functions rather than on substitution or permutation, although the security of any encryption scheme indeed depends on the length of the key and the computational work involved. An implementation shall of the support aes algorithm at least one specified in sec. 5: 128, 192, or 256 bits may optionally support two or three interoperability key algorithm implementations. The algorithm relies on confusion and diffusion principles to secure plaintext against attacks. aes consists of an initial round, multiple intermediate rounds, and a final round, each employing key transformations. Aes algorithm free download as pdf file (.pdf), text file (.txt) or view presentation slides online. the document provides a quick introduction to the advanced encryption standard (aes) algorithm.
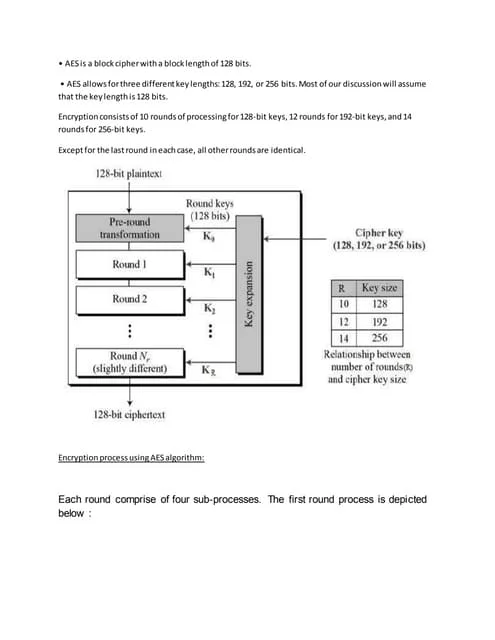
Aes Algorithm Notes Docx The algorithm relies on confusion and diffusion principles to secure plaintext against attacks. aes consists of an initial round, multiple intermediate rounds, and a final round, each employing key transformations. Aes algorithm free download as pdf file (.pdf), text file (.txt) or view presentation slides online. the document provides a quick introduction to the advanced encryption standard (aes) algorithm.
Aes Algorithm Notes Docx Computing Technology Computing

Aes Algorithm Pdf Key Cryptography Cipher

Lecture On Aes Pdf Cryptography Encryption

Cryptography Algorithms Security Standards

Aes Algorithm 31 Download Scientific Diagram

Pdf Implementation Of Aes Algorithm

Aes Encryption Key Features Security Pdf Cryptography Key

Aes Algorithm Pdf Cipher Cryptography

Aes Algorithm Module 4 Pdf Cryptography Cipher

Pdf A Comparative Analysis Of Different Encryption Algorithms Rsa
Basics Of Cryptographic Algorithms Geeksforgeeks

Data Security By Aes Advanced Encryption Standard Pdf

Aes Based Encryption Algorithm Download Scientific Diagram

The Aes Algorithm Pdf Field Mathematics Algebra

Aes 1 Pdf Algorithms Security Technology

4 Aes Algorithm And Block Cipher Modes Of Operations Download Free

Aes Algorithm Pdf
How To Calculate Key For Encrypting Data In Aes Algorithms

Aes Algorithm 31 Download Scientific Diagram

Pdf S A Review Of Des And Aes Algorithms For Image Encryption

Aes Algorithm And Implementation Pdf Computer Architecture Computing

Aes 4 Pdf Computer Security Security

Aes Symmetric Cipher Overview Pdf Algorithms Computer Security

Pdf Performance And Security Analysis Of Symmetric Data Encryption

Pdf Design Engineering Performance Evaluation Of Modified Aes

Aes Pdf Algorithms Computer Security

Pdf Enhancing Hybrid Security Approach Using Aes And Rsa Algorithms

Pdf A Study Of Encryption Algorithms Aes Des And Rsa For Security

Pdf Design And Implementation Of Aes Data Security Protocol

Pdf Enhancing Cloud Computing Security With Aes Algorithm

Aes Based Encryption Algorithm Download Scientific Diagram