
Example Aes 2 Pdf Cipher Applied Mathematics Aes example add roundkey, round 1 state matrix and roundkey no.1 matrix: 0 1 ba 84 e8 1b. Aes example round 1, substitution bytes • current state matrix is 00 3c 6e 47 1f 4e 22 74 0e 08 1b 31 54 59 0b 1a • substitute each entry (byte) of current state matrix by corresponding entry in aes s box • for instance: byte 6e is substituted by entry of s box in row 6 and column e, i.e., by 9f • this leads to new state matrix 63 eb.

Aes Step By Step Pdf Encryption Cipher Aes example (2).pdf free download as pdf file (.pdf), text file (.txt) or view presentation slides online. the document provides an example of the aes encryption process using a 128 bit key and plaintext. Aes, notified by nist as a standard in 2001, is a slight variation of the rijndael cipher invented by two belgian cryptographers joan daemen and vincent rijmen. Apply the matrix multiplication with the constant matrix, me, using gf(24). for gf(24), the addition operation is simply an xor, and for the multiplication operation you can use a lookup table. add round 1 key. now we have the final ciphertext. now lets decrypt. The following document provides a detailed and easy to understand explanation of the implementation of the aes (rijndael) encryption algorithm. the purpose of this paper is to give developers with little or no knowledge of cryptography the ability to implement aes.
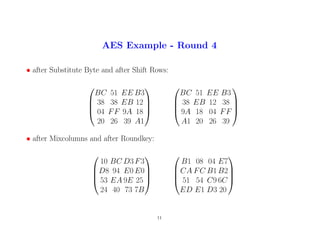
Aes Solved Example On Encryption All Rounds Pdf Apply the matrix multiplication with the constant matrix, me, using gf(24). for gf(24), the addition operation is simply an xor, and for the multiplication operation you can use a lookup table. add round 1 key. now we have the final ciphertext. now lets decrypt. The following document provides a detailed and easy to understand explanation of the implementation of the aes (rijndael) encryption algorithm. the purpose of this paper is to give developers with little or no knowledge of cryptography the ability to implement aes. Security emphasis was on security, resistance to cryptanalysis. nist explicitly demanded a 128 bit key to focus on resistance to cryptanalysis attacks other than brute force attack the criteria defined by nist for selecting aes fall into three areas:. It then describes the aes algorithm which works by repeating rounds that include byte substitution, shifting rows, mixing columns, and adding a round key. the number of rounds depends on the key size, being 10 for a 16 byte key and 14 for a 32 byte key. The document provides a step by step example of encrypting and decrypting a 16 bit plaintext using a simplified version of the aes algorithm. Aes is a subset of the rijndael block cipher developed by two belgian cryptographers vincent rijmen and joan daemen, who submitted a proposal to nist during the aes selection process.

Aes Solved Example On Encryption All Rounds Pdf Security emphasis was on security, resistance to cryptanalysis. nist explicitly demanded a 128 bit key to focus on resistance to cryptanalysis attacks other than brute force attack the criteria defined by nist for selecting aes fall into three areas:. It then describes the aes algorithm which works by repeating rounds that include byte substitution, shifting rows, mixing columns, and adding a round key. the number of rounds depends on the key size, being 10 for a 16 byte key and 14 for a 32 byte key. The document provides a step by step example of encrypting and decrypting a 16 bit plaintext using a simplified version of the aes algorithm. Aes is a subset of the rijndael block cipher developed by two belgian cryptographers vincent rijmen and joan daemen, who submitted a proposal to nist during the aes selection process.