
Simplified Aes Example Pdf Key Cryptography Cryptography Simplified aes example free download as pdf file (.pdf), text file (.txt) or read online for free. the document provides a step by step example of encrypting and decrypting a 16 bit plaintext using a simplified version of the aes algorithm. Aes example add roundkey, round 1 state matrix and roundkey no.1 matrix: 0 1 ba 84 e8 1b.

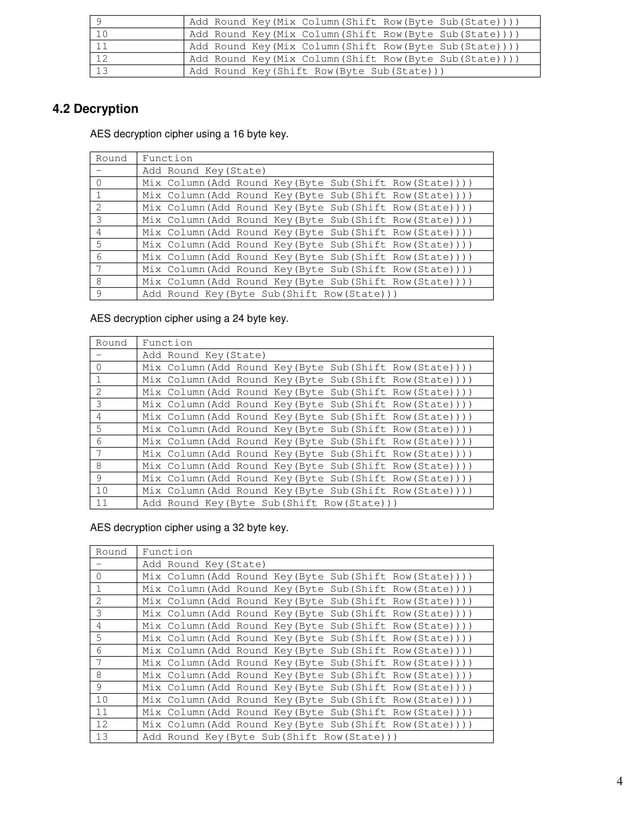
Pr7 Aes Java Final Pdf Computer Security Security It then describes the aes algorithm which works by repeating rounds that include byte substitution, shifting rows, mixing columns, and adding a round key. the number of rounds depends on the key size, being 10 for a 16 byte key and 14 for a 32 byte key. To review the overall structure of aes and to focus particularly on the four steps used in each round of aes: (1) byte substitution, (2) shift rows, (3) mix columns, and (4) add round key. Nist explicitly demanded a 128 bit key to focus on resistance to cryptanalysis attacks other than brute force attack the criteria defined by nist for selecting aes fall into three areas:. The following document provides a detailed and easy to understand explanation of the implementation of the aes (rijndael) encryption algorithm. the purpose of this paper is to give developers with little or no knowledge of cryptography the ability to implement aes.
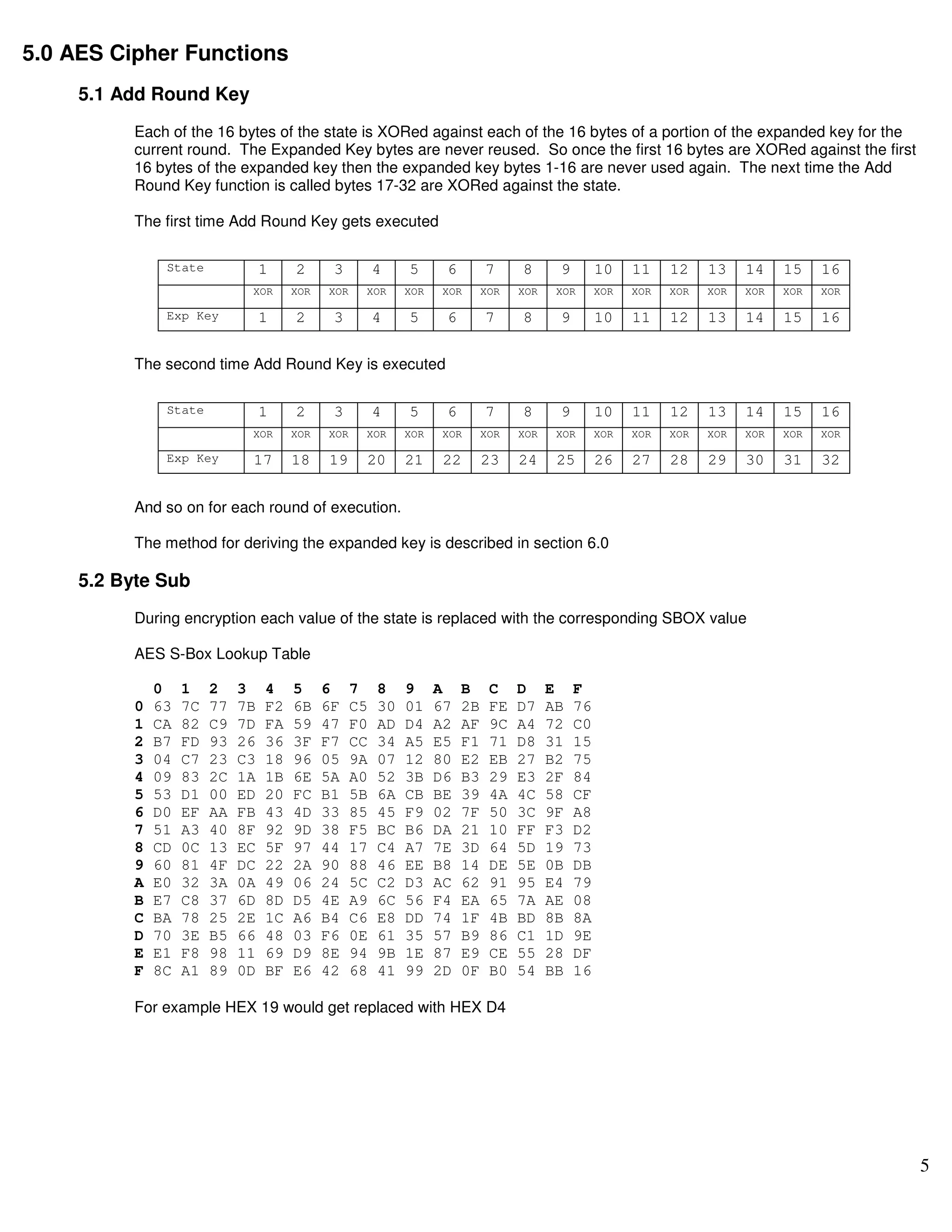
Aes By Example Pdf Nist explicitly demanded a 128 bit key to focus on resistance to cryptanalysis attacks other than brute force attack the criteria defined by nist for selecting aes fall into three areas:. The following document provides a detailed and easy to understand explanation of the implementation of the aes (rijndael) encryption algorithm. the purpose of this paper is to give developers with little or no knowledge of cryptography the ability to implement aes. They solicited algorithms to replace des to be the new government standard, aes. there were five finalists chosen, and of those, the winning entry was submitted by joan daemon and vincent rijment and is called rijndael (pronouced "rain doll".). The advanced encryption standard (aes), which is also known as rijndael (its original name), is a specification for the encryption of electronic data. encryption is a process of encoding messages or vital information in such a way that only canonical parties can read it. Apply the matrix multiplication with the constant matrix, me, using gf(24). for gf(24), the addition operation is simply an xor, and for the multiplication operation you can use a lookup table. add round 1 key. now we have the final ciphertext. now lets decrypt. In present day cryptography, aes is widely adopted and supported in both hardware and software. till date, no practical cryptanalytic attacks against aes has been discovered.
Aes By Example Pdf Programming Languages Computing They solicited algorithms to replace des to be the new government standard, aes. there were five finalists chosen, and of those, the winning entry was submitted by joan daemon and vincent rijment and is called rijndael (pronouced "rain doll".). The advanced encryption standard (aes), which is also known as rijndael (its original name), is a specification for the encryption of electronic data. encryption is a process of encoding messages or vital information in such a way that only canonical parties can read it. Apply the matrix multiplication with the constant matrix, me, using gf(24). for gf(24), the addition operation is simply an xor, and for the multiplication operation you can use a lookup table. add round 1 key. now we have the final ciphertext. now lets decrypt. In present day cryptography, aes is widely adopted and supported in both hardware and software. till date, no practical cryptanalytic attacks against aes has been discovered.

Aes Algorithm Pdf Cipher Cryptography Apply the matrix multiplication with the constant matrix, me, using gf(24). for gf(24), the addition operation is simply an xor, and for the multiplication operation you can use a lookup table. add round 1 key. now we have the final ciphertext. now lets decrypt. In present day cryptography, aes is widely adopted and supported in both hardware and software. till date, no practical cryptanalytic attacks against aes has been discovered.