
Aes Rsa Hybrid Cryptography Pdf Cryptography Key Cryptography A panoramic survey of the advanced encryption standard: from architecture to security analysis, key management, real world applications, and post quantum challenges. Abstract in 2000, nist announced the selection of the rijndael block cipher family as the winner of the advanced encryption standard (aes) competition. block ciphers are the foundation for many cryptographic services, especially those that provide assurance of the confdentiality of data.

Analysis And Comparison Of Symmetric Cryptography Algorithms A Study This proves that the combination of the aes 128 algorithm with the md 5 key can be used as an alternative for securing documents with stronger security, while maintaining standard processing. Python and perl implementations for creating the lookup tables for the byte substitution steps in encryption and decryption. python and perl implementations of the key expansion algorithms for the 128 bit, 192 bit, and 256 bit aes. Through a blend theoretical analysis and empirical investigations, we unravel the mechanisms by which errors propagate within aes, elucidating their effects on ciphertext integrity and decryption fidelity. In this paper two symmetric key security algorithms aes and des are compared .symmetric key algorithms are those algorithms which have same key for encryption and decryption.

5 Aes Pdf Cryptography Abstract Algebra Through a blend theoretical analysis and empirical investigations, we unravel the mechanisms by which errors propagate within aes, elucidating their effects on ciphertext integrity and decryption fidelity. In this paper two symmetric key security algorithms aes and des are compared .symmetric key algorithms are those algorithms which have same key for encryption and decryption. At this stage is the process of introducing aes cryptography algorithm, starting from the definition of aes algorithm, aes algorithm method, how aes cryptography works, key length used, advantages and disadvantages of aes cryptography and other matters relating to aes cryptography. Even if eve knows only part of the cipher key or the values of the words in some round keys, she still needs to find the rest of the cipher key before she can find all round keys. The result of the analysis in encryption of rsa algorithm shows that it has higher security level but only handle small file size and a lot of time and power, the aes algorithm can handle large size of file but have key management problem, and therefore it is less secured. In this paper we had a brief study of different set of algorithms and its implementations and we did examine it on some parameters which is time consumed, bit independence criteria and avalanche effect. keywords aes, des, avalanche effect, cryptography.
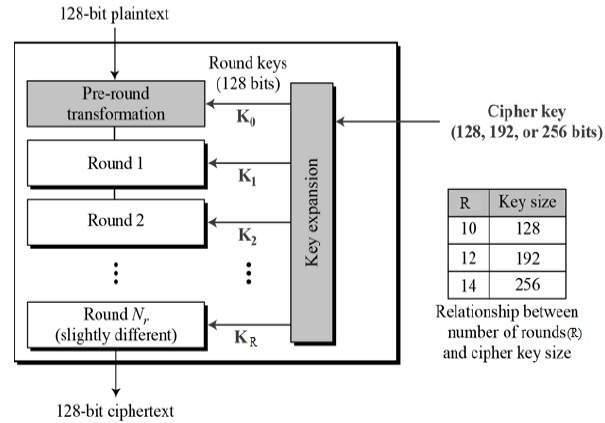
Aes Transformation Function In Cryptography At this stage is the process of introducing aes cryptography algorithm, starting from the definition of aes algorithm, aes algorithm method, how aes cryptography works, key length used, advantages and disadvantages of aes cryptography and other matters relating to aes cryptography. Even if eve knows only part of the cipher key or the values of the words in some round keys, she still needs to find the rest of the cipher key before she can find all round keys. The result of the analysis in encryption of rsa algorithm shows that it has higher security level but only handle small file size and a lot of time and power, the aes algorithm can handle large size of file but have key management problem, and therefore it is less secured. In this paper we had a brief study of different set of algorithms and its implementations and we did examine it on some parameters which is time consumed, bit independence criteria and avalanche effect. keywords aes, des, avalanche effect, cryptography.

Analysis Of Aes Encryption Process Using A 128 Bit Key And Plaintext The result of the analysis in encryption of rsa algorithm shows that it has higher security level but only handle small file size and a lot of time and power, the aes algorithm can handle large size of file but have key management problem, and therefore it is less secured. In this paper we had a brief study of different set of algorithms and its implementations and we did examine it on some parameters which is time consumed, bit independence criteria and avalanche effect. keywords aes, des, avalanche effect, cryptography.