A Detailed Overview On Advanced Encryption Standard Aes Advanced encryption standard (aes) is a highly trusted encryption algorithm used to secure data by converting it into an unreadable format without the proper key. it is developed by the national institute of standards and technology (nist) in 2001. The more popular and widely adopted symmetric encryption algorithm likely to be encountered nowadays is the advanced encryption standard (aes). it is found at least six time faster than triple des. a replacement for des was needed as its key size was too small.

What Is Advanced Encryption Standard Aes The advanced encryption standard (aes) specifes a fips approved cryp tographic algorithm that can be used to protect electronic data. the aes algorithm is a symmetric block cipher that can encrypt (encipher) and decrypt (decipher) digital information. This tutorial explores the need for aes encryption, its origin and process of encryption, all the way up to its applications, and a direct comparison with the des algorithm. Aes is included in the iso iec 18033 3 standard. aes became effective as a us federal government standard on may 26, 2002, after approval by us secretary of commerce donald evans. Aes (advanced encryption standard) is a symmetric key cryptographic algorithm and also a block cipher that is superior and replaces the des. this article aims to break down the tutorial,.
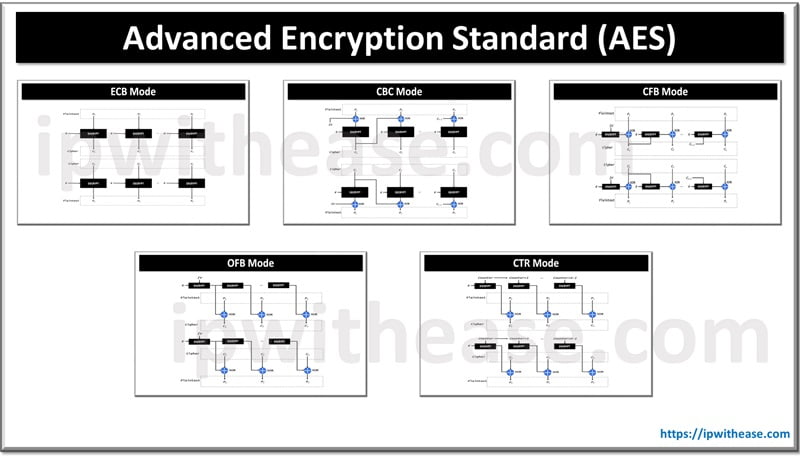
Advanced Encryption Standard Aes Ip With Ease Aes is included in the iso iec 18033 3 standard. aes became effective as a us federal government standard on may 26, 2002, after approval by us secretary of commerce donald evans. Aes (advanced encryption standard) is a symmetric key cryptographic algorithm and also a block cipher that is superior and replaces the des. this article aims to break down the tutorial,. Learn about the advanced encryption standard (aes), a top tier encryption protocol trusted for safeguarding sensitive data. explore its history, functionality, features, and practical applications. Aes (advanced encryption standard) is a symmetric block cipher algorithm that has been the standard for encrypting data since 2001. it was selected by the u.s. national institute of standards and technology (nist) to replace des and is now used worldwide for securing sensitive data. This tutorial is a complete comprehensive understanding of the advanced encryption standard aes with the help of some figures and examples. Aes was designed to replace the outdated data encryption standard (des), which can no longer resist modern cyberattacks. in this article, you’ll learn how aes encryption works, its types, key features, applications, and how it compares to other cryptographic algorithms such as des and rsa.

Here S Everything You Need To Know About Advanced Encryption Standard Aes Learn about the advanced encryption standard (aes), a top tier encryption protocol trusted for safeguarding sensitive data. explore its history, functionality, features, and practical applications. Aes (advanced encryption standard) is a symmetric block cipher algorithm that has been the standard for encrypting data since 2001. it was selected by the u.s. national institute of standards and technology (nist) to replace des and is now used worldwide for securing sensitive data. This tutorial is a complete comprehensive understanding of the advanced encryption standard aes with the help of some figures and examples. Aes was designed to replace the outdated data encryption standard (des), which can no longer resist modern cyberattacks. in this article, you’ll learn how aes encryption works, its types, key features, applications, and how it compares to other cryptographic algorithms such as des and rsa.

The Advanced Encryption Standard Aes Technology Pufsecurity This tutorial is a complete comprehensive understanding of the advanced encryption standard aes with the help of some figures and examples. Aes was designed to replace the outdated data encryption standard (des), which can no longer resist modern cyberattacks. in this article, you’ll learn how aes encryption works, its types, key features, applications, and how it compares to other cryptographic algorithms such as des and rsa.