
User Verification Two Factor Authentication Api Toku How to verify user identity? article about popular verification methods, why verifying user identity is important, and the role of verifying user identity. In this blog, we’ll understand the concept of identity verification, what it is, why it's such an important step for businesses, and how you can ensure your verification processes are secure, reliable, and efficient.
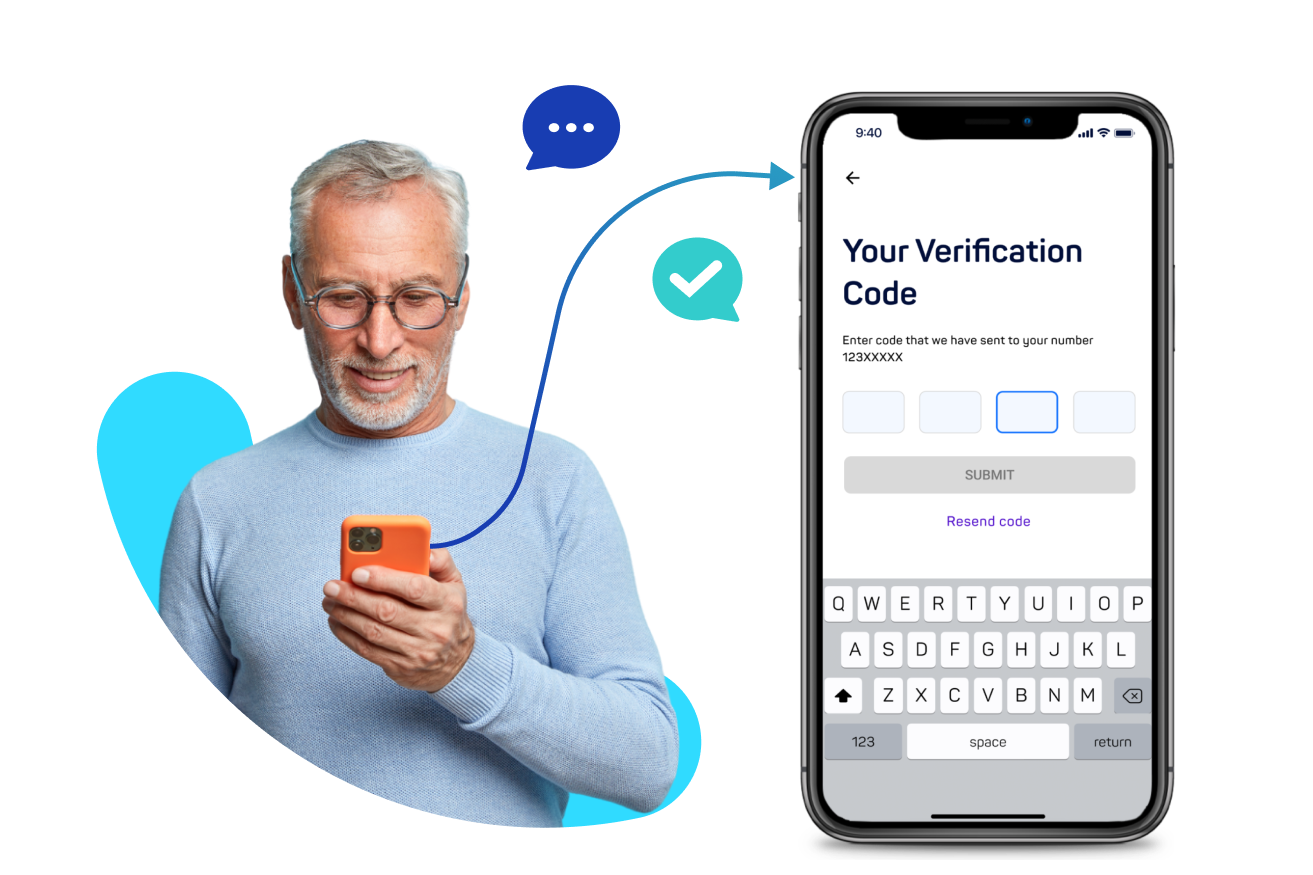
User Verification Two Factor Authentication Api Toku However, many websites and apps struggle to get their users to complete the verification process. in this article, we'll share some tips and tools on how to optimize user verification rates and improve online security. User verification, in the landscape of cybersecurity and antivirus software, is a critical process that relies on authenticating the identity of a user. the goal is to ensure only authorized individuals have access to specific data, accounts, or systems. But what exactly is account verification, and why does it matter? in this article, we delve into the fundamentals of account verification, exploring its significance, best practices, and strategic implementations. join us as we explore the intricacies of this essential user verification process. User authentication is central to this security paradigm as it refers to the mechanism by which the identity of a user is first confirmed before being granted access to a resource.

Streamlined User Verification Process But what exactly is account verification, and why does it matter? in this article, we delve into the fundamentals of account verification, exploring its significance, best practices, and strategic implementations. join us as we explore the intricacies of this essential user verification process. User authentication is central to this security paradigm as it refers to the mechanism by which the identity of a user is first confirmed before being granted access to a resource. Identity proofing is the process of verifying an individual is who they claim they are when they first interact with an organization. it involves collecting and validating identity related information to establish a person’s identity before they can access services or complete transactions. This blog delves into the intricate balance between ensuring robust security, maintaining user accessibility, and managing costs in user verification processes. Think about the value your business can unlock when you aren't worrying about the challenges that come with managing user authentication and identification. explore the different ways twilio customers benefit from buying an out of the box user verification solution. It utilizes advanced technologies like facial recognition, document verification, and biometrics to ensure accurate and secure identity verification, helping businesses and organizations establish trust with their users.".

User Verification Designs Themes Templates And Downloadable Graphic Identity proofing is the process of verifying an individual is who they claim they are when they first interact with an organization. it involves collecting and validating identity related information to establish a person’s identity before they can access services or complete transactions. This blog delves into the intricate balance between ensuring robust security, maintaining user accessibility, and managing costs in user verification processes. Think about the value your business can unlock when you aren't worrying about the challenges that come with managing user authentication and identification. explore the different ways twilio customers benefit from buying an out of the box user verification solution. It utilizes advanced technologies like facial recognition, document verification, and biometrics to ensure accurate and secure identity verification, helping businesses and organizations establish trust with their users.".

User Verification Marketplacekit Think about the value your business can unlock when you aren't worrying about the challenges that come with managing user authentication and identification. explore the different ways twilio customers benefit from buying an out of the box user verification solution. It utilizes advanced technologies like facial recognition, document verification, and biometrics to ensure accurate and secure identity verification, helping businesses and organizations establish trust with their users.".

User Verification Marketplacekit