
Python Hacking Tools Lenaprofessional An ethical hacker finds the weak points or loopholes in a computer, web applications or network and reports them to the organization. so, let’s explore more about ethical hacking step by step. We present the most important and frequently used python commands for ethical hacking and penetration testing.
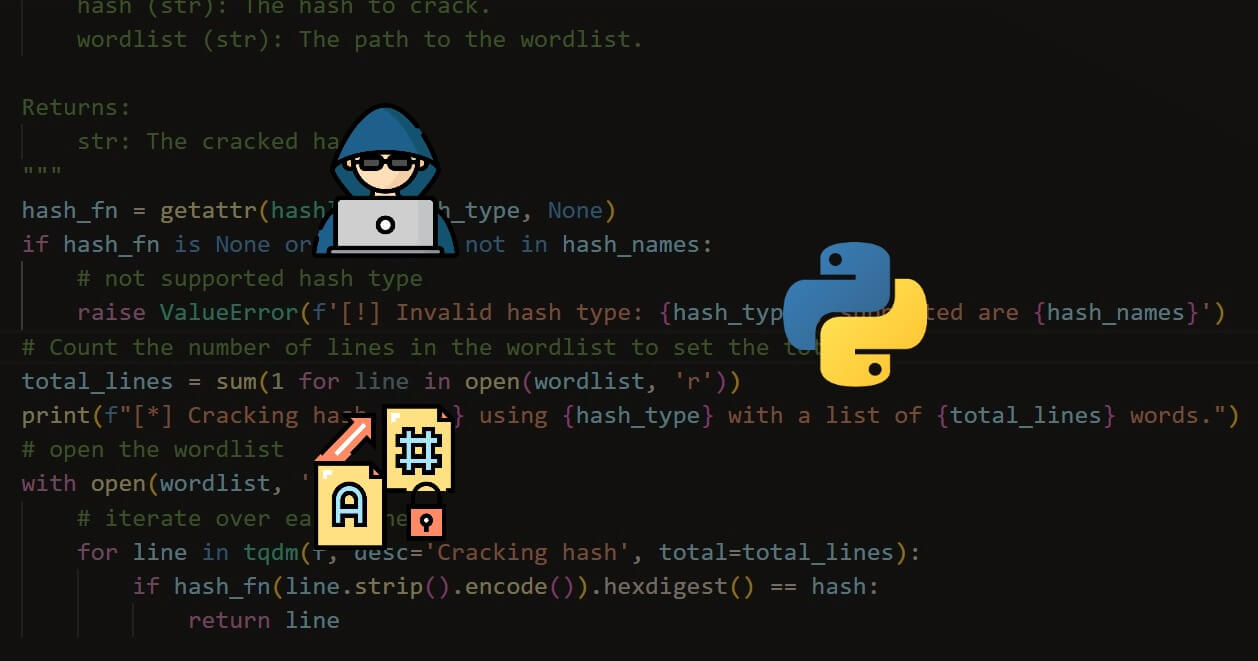
How To Crack Hashes In Python The Python Code In recent years, python has become the language of choice for such tasks, and there are good reasons for this. in this article on ethical hacking tutorial using python, we will discuss the reasons that make these two such a brilliant couple. Master python hacking for information security. our step by step guide helps experienced pros build custom tools and apply ethical hacking techniques in 2025. Discover how to use python for hacking, including coding skills, libraries, and tools to help you understand and practice ethical hacking. Explore the fundamentals of ethical hacking with python, dive into the key python libraries used in ethical hacking, and provide practical examples to help you develop hands on skills.

The Complete Python Hacking Course Joseph Delgadillo Discover how to use python for hacking, including coding skills, libraries, and tools to help you understand and practice ethical hacking. Explore the fundamentals of ethical hacking with python, dive into the key python libraries used in ethical hacking, and provide practical examples to help you develop hands on skills. This comprehensive course will guide you step by step on how to master ethical hacking techniques using python, one of the most versatile and powerful programming languages. With python, ethical hackers can craft custom tools, automate tasks, and orchestrate complex attack scenarios, all tailored to the specific needs of their ethical hacking endeavors. it’s like wielding a magical coding wand to conjure up the perfect spells for cybersecurity defense. The .pth mechanism fires on every python interpreter startup. because the payload spawns a new python subprocess, and that new process also triggers .pth execution, the result was an unintended fork bomb. mcmahon published his findings on futuresearch.ai, and the disclosure spread to r localllama, r python, and hacker news within the hour. On march 31, 2026, anthropic accidentally published the entire source code of claude code its flagship ai coding agent inside an npm package. no hack. no reverse engineering. a missing .npmignore entry shipped a 59.8 mb source map containing 512,000 lines of unobfuscated typescript across roughly 1,900 files. within hours, the code was mirrored, dissected, rewritten in python and rust, and.

Hacking With Python The Complete Beginner S Guide To Learning Ethical This comprehensive course will guide you step by step on how to master ethical hacking techniques using python, one of the most versatile and powerful programming languages. With python, ethical hackers can craft custom tools, automate tasks, and orchestrate complex attack scenarios, all tailored to the specific needs of their ethical hacking endeavors. it’s like wielding a magical coding wand to conjure up the perfect spells for cybersecurity defense. The .pth mechanism fires on every python interpreter startup. because the payload spawns a new python subprocess, and that new process also triggers .pth execution, the result was an unintended fork bomb. mcmahon published his findings on futuresearch.ai, and the disclosure spread to r localllama, r python, and hacker news within the hour. On march 31, 2026, anthropic accidentally published the entire source code of claude code its flagship ai coding agent inside an npm package. no hack. no reverse engineering. a missing .npmignore entry shipped a 59.8 mb source map containing 512,000 lines of unobfuscated typescript across roughly 1,900 files. within hours, the code was mirrored, dissected, rewritten in python and rust, and.